Abstract
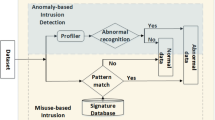
This paper describes a multiagent system with capabilities to analyze and discover knowledge gathered from distributed agents. These enhanced capabilities are obtained through a dynamic self-organizing map and a multiagent communication system. The central administrator agent dynamically obtains information about the attacks or intrusions from the distributed agents and maintains a knowledge pool using a proposed growing self-organizing map. The approach integrates traditional mathematical and data mining techniques with a multiagent system. The proposed system is used to build an intrusion detection system (IDS) as a network security application. Finally, experimental results are presented to confirm the good performance of the proposed system.
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Cannady, J.: Artificial neural networks for misuse detection. In: anonymous (ed.) Proceedings of the 1998 National Information Systems Security Conference (NISSC 1998), Arlington, VA, October 5-8, pp. 443–456 (1998)
Czibula, G., Guran, A., Cojocar, G., Czibula, I.: Multiagent decision support systems based on supervised learning. In: IEEE International Conference on Automation, Quality and Testing, Robotics, 2008. AQTR 2008, vol. 3, pp. 353–358 (2008)
DeLooze, L.L.: Attack characterization and intrusion detection using an ensemble of self-organizing maps. In: 7th Annual IEEE Information Assurance Workshop, pp. 108–115 (2006)
Kohonen, T.: Self-organized formation of topologically correct feature maps. Biological cybernetics 43(1), 59–69 (1982)
Lee, W., Stolfo, S., Chan, P., Eskin, E., Fan, W., Miller, M., Hershkop, S., Zhang, J.: Real time data mining-based intrusion detection. In: DARPA Information Survivability Conference & Exposition II, vol. 1, pp. 89–100 (2001)
Maxion, R., Tan, K.: Anomaly detection in embedded systems. IEEE Transactions on Computers 51(2), 108–120 (2002)
Mitrokotsa, A., Douligeris, C.: Detecting denial of service attacks using emergent self-organizing maps. In: 5th IEEE International Symposium on Signal Processing and Information Technology, pp. 375–380 (2005)
Sarasamma, S., Zhu, Q., Huff, J.: Hierarchical kohonenen net for anomaly detection in network security. IEEE Transactions on Systems Man and Cybernetics Part B-Cybernetics 35(2), 302–312 (2005)
Tan, K., Maxion, R.: Determining the operational limits of an anomaly-based intrusion detector. IEEE Journal on Selected Areas in Communications 21(1), 96–110 (2003)
Wickramasinghe, L., Alahakoon, L.: Dynamic self organizing maps for discovery and sharing of knowledge in multi agent systems. Web Intelli. and Agent Sys. 3(1), 31–47 (2005)
Ying, H., Feng, T.-J., Cao, J.-K., Ding, X.-Q., Zhou, Y.-H.: Research on some problems in the kohonen som algorithm. In: International Conference on Machine Learning and Cybernetics, vol. 3, pp. 1279–1282 (2002)
Zhang, W.-R., Zhang, L.: A multiagent data warehousing (madwh) and multiagent data mining (madm) approach to brain modeling and neurofuzzy control. Inf. Sci. Inf. Comput. Sci. 167(1-4), 109–127 (2004)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2009 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Palomo, E.J., Domínguez, E., Luque, R.M., Muñoz, J. (2009). A Self-Organized Multiagent System for Intrusion Detection. In: Cao, L., Gorodetsky, V., Liu, J., Weiss, G., Yu, P.S. (eds) Agents and Data Mining Interaction. ADMI 2009. Lecture Notes in Computer Science(), vol 5680. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-03603-3_7
Download citation
DOI: https://doi.org/10.1007/978-3-642-03603-3_7
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-03602-6
Online ISBN: 978-3-642-03603-3
eBook Packages: Computer ScienceComputer Science (R0)