Abstract
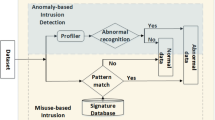
This paper presents a hierarchical self-organizing neural network for intrusion detection. The proposed neural model consists of a hierarchical architecture composed of independent growing self-organizing maps (SOMs). The SOMs have shown to be successful for the analysis of high-dimensional input data as in data mining applications such as network security. An intrusion detection system (IDS) monitors the IP packets flowing over the network to capture intrusions or anomalies. One of the techniques used for anomaly detection is building statistical models using metrics derived from observation of the user’s actions. The proposed growing hierarchical SOM (GHSOM) address the limitations of the SOM related to their static architecture. Experimental results are provided by applying the well-known KDD Cup 1999 benchmark data set, which contains a great variety of simulated networks attacks. Randomly selected subsets that contain both attacks and normal records from this benchmark are used for training the GHSOM. Before training, a transformation for qualitative features present in the benchmark data set is proposed in order to compute distance among qualitative values. Comparative results with other related works are also provided.
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Kohonen, T.: Self-organized formation of topologically correct feature maps. Biological cybernetics 43(1), 59–69 (1982)
Rauber, A., Merkl, D., Dittenbach, M.: The growing hierarchical self-organizing map: Exploratory analysis of high-dimensional data. IEEE Transactions on Neural Networks 13(6), 1331–1341 (2002)
Lei, J., Ghorbani, A.: Network intrusion detection using an improved competitive learning neural network. In: 2nd Annual Conference on Communication Networks and Services Research, pp. 190–197 (2004)
Sarasamma, S., Zhu, Q., Huff, J.: Hierarchical kohonenen net for anomaly detection in network security. IEEE Transactions on Systems Man and Cybernetics Part B-Cybernetics 35(2), 302–312 (2005)
Depren, O., Topallar, M., Anarim, E., Ciliz, M.: An intelligent intrusion detection system (ids) for anomaly and misuse detection in computer networks. Expert Systems with Applications 29(4), 713–722 (2005)
Denning, D.: An intrusion-detection model. IEEE Transactions on Software Engineering SE-13(2), 222–232 (1987)
Lee, W., Stolfo, S., Chan, P., Eskin, E., Fan, W., Miller, M., Hershkop, S., Zhang, J.: Real time data mining-based intrusion detection. In: DARPA Information Survivability Conference & Exposition II, vol. 1, pp. 89–100 (2001)
Maxion, R., Tan, K.: Anomaly detection in embedded systems. IEEE Transactions on Computers 51(2), 108–120 (2002)
Tan, K., Maxion, R.: Determining the operational limits of an anomaly-based intrusion detector. IEEE Journal on Selected Areas in Communications 21(1), 96–110 (2003)
Ying, H., Feng, T.J., Cao, J.K., Ding, X.Q., Zhou, Y.H.: Research on some problems in the kohonen som algorithm. In: International Conference on Machine Learning and Cybernetics, vol. 3, pp. 1279–1282 (2002)
Lee, W., Stolfo, S., Mok, K.: A data mining framework for building intrusion detection models. In: IEEE Symposium on Security and Privacy, pp. 120–132 (1999)
Stolfo, S., Fan, W., Lee, W., Prodromidis, A., Chan, P.: Cost-based modeling for fraud and intrusion detection: results from the jam project. In: Proceedings of DARPA Information Survivability Conference and Exposition, 2000. DISCEX 2000, vol. 2, pp. 130–144 (2000)
Alahakoon, D., Halgamuge, S., Srinivasan, B.: Dynamic self-organizing maps with controlled growth for knowledge discovery. IEEE Transactions on Neural Networks 11, 601–614 (2000)
Dittenbach, M., Rauber, A., Merkl, D.: Recent advances with the growing hierarchical self-organizing map. In: 3rd Workshop on Self-Organising Maps (WSOM), pp. 140–145 (2001)
DeLooze, L., AF DeLooze, L.: Attack characterization and intrusion detection using an ensemble of self-organizing maps. In: 7th Annual IEEE Information Assurance Workshop, pp. 108–115 (2006)
Mitrokotsa, A., Douligeris, C.: Detecting denial of service attacks using emergent self-organizing maps. In: 5th IEEE International Symposium on Signal Processing and Information Technology, pp. 375–380 (2005)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2009 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Palomo, E.J., Domínguez, E., Luque, R.M., Muñoz, J. (2009). Network Security Using Growing Hierarchical Self-Organizing Maps. In: Kolehmainen, M., Toivanen, P., Beliczynski, B. (eds) Adaptive and Natural Computing Algorithms. ICANNGA 2009. Lecture Notes in Computer Science, vol 5495. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-04921-7_14
Download citation
DOI: https://doi.org/10.1007/978-3-642-04921-7_14
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-04920-0
Online ISBN: 978-3-642-04921-7
eBook Packages: Computer ScienceComputer Science (R0)