Abstract
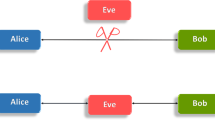
Quantum Cryptography or Quantum key distribution (QKD) is new method that allows the secure distribution of a bit string, used as key in cryptographic protocols. Extensive researches have been undertaken on Quantum Cryptography since it was noted that quantum computers could break public key cryptosystems based on number theory. Quantum Cryptography offers unconditionally secure communication based on laws of quantum physics. Actually, there is a strong need of research to use this technology in the existing communication networks. We explore in this paper, the possibility of exploiting QKD in the authentication process for local area networks (LANs). Precisely, we have elaborated a scheme to integrate the new technique of QKD in the CHAP protocol (Challenge Handshake Authentication Protocol) to enhance the security of the authentication service.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Gisin, N., et al.: Quantum cryptography. Rev. Mod. Phys. 74, 145–195 (2002)
Schneier, B.: Applied Cryptography: Protocols, Algorithms, and Source Code in C, 2nd edn. Wiley, Chichester (1995)
Bennett, C.H., et al.: Experimental quantum cryptography. J. Cryptol. 5, 3–28 (1992)
Nguyen, T.M.T., Sfaxi, M.A., Ghernaouti-Hélie, S.: 802.11 i Encryption Key Distribution Using Quantum Cryptography. JOURNAL OF NETWORKS 1(5), 9 (2006)
Elboukhari, M., Azizi, M., Azizi, A.: Integration of Quantum Key Distribution in the TLS Protocol. IJCSNS 9(12), 21–28 (2009), http://paper.ijcsns.org/07_book/200912/20091204.pdf (Cited June 07, 2010)
Bennett, C.H., Brassard, G.: Quantum cryptography: Public key distribution and coin tossing. In: Proc. IEEE Int. Conf. Computers, Systems and Signal Processing, New York, Bangalore, India, pp. 175–179 (1984)
Simpson, W.: PPP Challenge Handshake Authentication Protocol (CHAP), RFC 1994 (August 1996)
Simpson, W.: The Point-to-Point Protocol (PPP), RFC1661 (July 1994)
Rivest, R.: The MD5 message-Digest Algorithm, RFC 1321 (April 1992)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2010 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Elboukhari, M., Azizi, M., Azizi, A. (2010). Improving the Security of CHAP Protocol by Quantum Cryptography. In: Essaaidi, M., Malgeri, M., Badica, C. (eds) Intelligent Distributed Computing IV. Studies in Computational Intelligence, vol 315. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-15211-5_25
Download citation
DOI: https://doi.org/10.1007/978-3-642-15211-5_25
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-15210-8
Online ISBN: 978-3-642-15211-5
eBook Packages: EngineeringEngineering (R0)