Summary
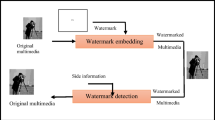
Lossy compression attacks in digital watermarking are one of the major issues in digital watermarking. Cheddad et al. proposed a robust secured self-embedding method which is resistant to a certain amount of JPEG compression. Our experimental results show that the self-embedding method is resistant to JPEG compression attacks and not resistant to other lossy compression attacks such as Block Truncation Coding (BTC) and Singular Value Decomposition (SVD). Therefore we improved Cheddad et al’s. method to give better protection against BTC and SVD compression attacks.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Voyatzis, G., Pitas, I.: Protecting digital-image copyrights: a framework. IEEE Computer Graphics and Applications 19, 18–24 (1999)
Bender, W., Gruhl, D., Morimoto, N., Lu, A.: Techniques for data hiding. IBM Systems Journal 35(3&4), 313–336 (1996)
Cox, I.J., Killian, J., Leighton, T., Shammon, T.: Secure spread spectrum for multimedia. IEEE Transactions on Image Processing 6(12), 1673–1687 (1997)
Vetterli, M., Kovacevic, J.: Wavelet and Subband Coding. Prentice-Hall, Englewood Cliffs (1995)
Wolfgang, R.B., Podichuk, C.I., Delp, E.J.: Perceptual watermarks for digital images and video. Proceedings of the IEEE 87(7), 1108–1126 (1999)
Cheddad, A., Condell, J., Curran, K., McKevitt, P.: A secure and improved self-embedding algorithm to combat digital document forgery. Signal Processing 89(12), 2324–2332 (2009)
Daren, H., Jiufen, L., Jiwu, H., Hongmei, L.: A DWT-based image watermarking algorithm. In: IEEE Int. Conf. Multimedia and Expo., pp. 429–432 (2001)
Joo, S., Suh, Y., Shin, J., Kitkuchi, H.: A New Robust Watermark Embedding into Wavelet DC Components. ETRI Journal 24(5), 401–404 (2002)
Floyd, R.W., Steinberg, L.: An adaptive algorithm for spatial grayscale. In: Proc. Soc. Inf. Disp., vol. 12, pp. 55–77 (1976)
Neelamani, R., Nowak, R., Baraniuk, R.G.: WInHD: wavelet-based inverse halftoning via deconvolution. submitted to IEEE Trans. Image Process. for publication (2002)
Chanda, B., Dutta Majumder, D.: Digital Image Processing and Analysis. Prentice-Hall, Englewood Cliffs (2000)
Richards, D., Abrahamsen, A.: Image compression using singular value decomposition. linear algebra applications (2001)
Prasantha, H.S., Shashidhara, H.L., Balasubramanya Murthy, K.N.: Image Compression using SVD. In: Proc. of International Conference on Computational Intelligence and Multimedia Applications, pp. 143–145 (2007)
Cheddad, A., Condell, J., Curran, K., McKevitt, P.: A Hash-based Image Encryption Algorithm. Opt. Comm. Elsevier Science. 283(6), 879–893 (2010)
Wang, Y., Liao, X., Xiao, D., Wong, K.: One-way hash function construction based on 2D coupled map lattices. Inf. Sci. 178(5), 1391–1406 (2008)
US Secure Hash Algorithm 1 (2001), http://www.faqs.org/rfcs/rfc3174
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2010 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Yogarajah, P., Condell, J., Curran, K., Cheddad, A., McKevit, P. (2010). An Improved Self-embedding Algorithm: Digital Content Protection against Compression Attacks in Digital Watermarking. In: Choraś, R.S. (eds) Image Processing and Communications Challenges 2. Advances in Intelligent and Soft Computing, vol 84. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-16295-4_6
Download citation
DOI: https://doi.org/10.1007/978-3-642-16295-4_6
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-16294-7
Online ISBN: 978-3-642-16295-4
eBook Packages: EngineeringEngineering (R0)