Abstract
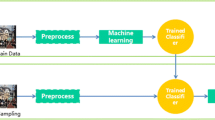
Recently, With the IT technique growth, there is getting formed to convert to ubiquitous environment that means it can access information everywhere and every-time using various devices, and the computer can decide to provide useful services to users. But, in this computing environment will be connected to wireless network and various devices. According to, recklessness approaches of information resource make trouble to system. So, access authority management is very important issue both information resource and adapt to system through founding security policy to need a system. So, this model has a problem that is not concerned about user’s context information as user’s profile. In this paper suppose to context-awareness RABC model that based on profile about which user’s information which provide efficiently access control to user through active classification, inference and judgment about user who access to system and resource.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Lyytinen, K., Yoo, Y.: Issues and challenges in ubiquitous computing. Communications of the ACM 45, 62–96 (2003)
Schilit, B.N., Adams, N., Want, R.: Context- aware computing applications. In: Proc. IEEE Workshop on Mobile Computing Systems and Applications, pp. 85–90 (1994)
Potonniée, O.: A decentralized privacy- enabling TV personalization framework. In: 2nd European Conference on Interactive Television: Enhancing the Experience, euroITV 2004 (2004)
Klyne, G., Reynolds, F., Woodrow, C., Ohto, H., Hjelm, J., Butler, M.H., Tran, L.: Composite Capability/Preference Profiles (CC/PP): Structure and vocabularies 1.0. W3C Recommendation, W3C (2004)
Ferraiolo, D.F., Cugini, J.A., Kuhn, D.R.: Role-Based Access Control(RBAC): Features and Motivations. In: 11th Annual Computer Security Application Conference (November 1995)
Sandhu, R.S., Coyne, E.J.: Role-Based Access Control Models. IEEE Computer 20(2), 38–47 (1996)
Sandhu, R.S., Ferraiolo, D., Kuhn, R.: The NIST Model for Role-Based Access Control:Towards a Unified Model Approach. In: 5th ACM Workshop on RBAC (August 2000)
Neumann, G., Strembeck, M.: An Approach to Engineer and Enforce Context Constraints in an RBAC Environment. In: 8th ACM Symposium on Access Control Models and Technologies (SACMAT 2003), pp. 65–79 (June 2003)
Covington, M.J., Moyer, M.J., Ahamad, M.: Generalized role-based access control for securing future application. In: NISSC, pp. 40–51 (October 2000)
Convington, M.J., Fogla, P., Zhan, Z., Ahamad, M.: Context-aware Security Architecture for Emerging Applications. In: Security Applications Conference (ACSAC) (2002)
Biegel, G., Vahill, V.: A Framework for Developing Mobile, Context-aware Applications. In: IEEE International Conference on Pervasive Computing and Communications (PerCom) (2004)
Gu, T., Pung, H.K., Zhang, D.Q.: A Middleware for Building Context-Aware Mobile Service. In: Proceedings of IEEE Vehicular Technology Conference (VTC) (2004)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2010 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Jang, B., Park, S., Chang, H., Ahn, H., Choi, E. (2010). A Study of Context-Awareness RBAC Model Using User Profile on Ubiquitous Computing. In: Kim, Th., Vasilakos, T., Sakurai, K., Xiao, Y., Zhao, G., Ślęzak, D. (eds) Communication and Networking. FGCN 2010. Communications in Computer and Information Science, vol 120. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-17604-3_23
Download citation
DOI: https://doi.org/10.1007/978-3-642-17604-3_23
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-17603-6
Online ISBN: 978-3-642-17604-3
eBook Packages: Computer ScienceComputer Science (R0)