Abstract
Rabbit is a stream cipher using a 128-bit key. It outputs one keystream block of 128 bits each time, which consists of eight sub-blocks of 16 bits. It is among the finalists of ECRYPT Stream Cipher Project (eSTREAM). Rabbit has also been published as informational RFC 4503 with IETF. Prior to us, the research on Rabbit all focused on the bias analysis within one keystream sub-block and the best distinguishing attack has complexity O(2158).
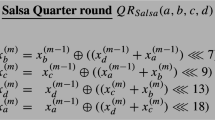
In this paper, we use the linear cryptanalysis method to study the bias of Rabbit involving multiple sub-blocks of one keystream block. To summarize, the largest bias we found out is estimated to be 2− 70.5. Assuming independence between the keystream blocks of Rabbit, we have a distinguishing attack on Rabbit requiring O(2141) keystream blocks. Compared with all previous results, it is the best distinguishing attack so far. Furthermore small-scale experiments suggest that our result might be a conservative estimate. Meanwhile, our attack can work by using keystream blocks generated by different keys, and so it is not limited by the cipher’s requirement that one key cannot be used to produce more than 264 keystream blocks.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Aumasson, J.P.: On a bias of Rabbit. In: SASC 2007 (2007), http://www.ecrypt.eu.org/stream/papersdir/2007/033.pdf
Boesgaard, M., Vesterager, M., Christensen, T., Zenner, E.: The stream cipher Rabbit. The ECRYPT stream cipher project, http://www.ecrypt.eu.org/stream/
Boesgaard, M., Vesterager, M., Zenner, E.: A description of the Rabbit stream cipher algorithm. RFC 4503 (May 2006), http://www.ietf.org/rfc/rfc4503.txt?number=4503
Cryptico A/S. Algebraic analysis of rabbit. White paper (2003)
Cryptico A/S. Hamming weights of the g-function. White paper (2003)
Lu, Y., Wang, H., Ling, S.: Cryptanalysis of Rabbit. In: Wu, T., Lei, C., Rijmen, V., Lee, D. (eds.) ISC 2008. LNCS, vol. 5222, pp. 204–214. Springer, Heidelberg (2008)
Matsui, M.: Linear cryptanalysis method for DES cipher. In: Helleseth, T. (ed.) EUROCRYPT 1993. LNCS, vol. 765, pp. 386–397. Springer, Heidelberg (1994)
Nyberg, K., Wallén, J.: Improved linear distinguishers for SNOW 2.0. In: Robshaw, M.J.B. (ed.) FSE 2006. LNCS, vol. 4047, pp. 144–162. Springer, Heidelberg (2006)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2011 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Lu, Y., Desmedt, Y. (2011). Improved Distinguishing Attack on Rabbit. In: Burmester, M., Tsudik, G., Magliveras, S., Ilić, I. (eds) Information Security. ISC 2010. Lecture Notes in Computer Science, vol 6531. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-18178-8_2
Download citation
DOI: https://doi.org/10.1007/978-3-642-18178-8_2
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-18177-1
Online ISBN: 978-3-642-18178-8
eBook Packages: Computer ScienceComputer Science (R0)