Abstract
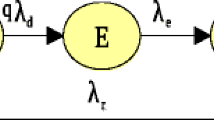
Active Peer-to-Peer worms are great threat to the network security since they can propagate in automated ways and flood the Internet within a very short duration. Modeling a propagation process can help us to devise effective strategies against a worm’s spread. This paper presents a study on modeling a worm’s propagation probability in a P2P overlay network and proposes an optimized patch strategy for defenders. Firstly, we present a probability matrix model to construct the propagation of P2P worms. Our model involves three indispensible aspects for propagation: infected state, vulnerability distribution and patch strategy. Based on a fully connected graph, our comprehensive model is highly suited for real world cases like Code Red II. Finally, by inspecting the propagation procedure, we propose four basic tactics for defense of P2P botnets. The rationale is exposed by our simulated experiments and the results show these tactics are of effective and have considerable worth in being applied in real-world networks
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Arce, I., Levy, E.: An analysis of the slapper worm. IEEE Security & Privacy Magazine 1, 82–87 (2003)
Holz, T., Steiner, M., Dahl, F., Biersack, E., Freiling, F.: Measurement and mitigation of peer-to-peer-based botnets: a case study on storm worm. In: The 1st Usenix Workshop on Large-Scale Exploits and Emergent Threats, San Francisco, USA, pp. 1–9 (April 2008)
Fan, X., Xiang, Y.: Modeling the propagation of Peer-to-Peer worms. Future Gener. Comp. Sy. 26, 1433 (2010)
Yu, W.: Analyze the worm-based attack in large scale P2P networks. In: 8th IEEE International Symposium on High Assurance Systems Engineering, pp. 308–309. IEEE Press, Tampa (2004)
Zou, C.C., Gong, W., Towsley, D.: Code Red worm propagation modeling and analysis. In: 9th ACM Conference on Computer and Communications Security, Washington, pp. 138–147 (2002)
CAIDA Analysis of Code-Red, http://www.caida.org/research/security/code-red/
Bailey, N.T.: The Mathematical Theory of Infectious Diseases and its Applications. Hafner Press, New York (1975)
Frauenthal, J.C.: Mathematical Modeling in Epidemiology. Springer, New York (1980)
Staniford, S., Paxson, V., Weaver, N.: How to own the internet in your spare time. In: The 11th USENIX Security Symposium, San Francisco, pp. 149–167. ACM, CA (2002)
Andersson, H., Britton, T.: Stochastic Epidemic Models and their Statistical Analysis. Springer, New York (2000)
Chen, Z., Gao, L., Kwiat, K.: Modeling the spread of active worms. In: IEEE INFOCOM, pp. 1890–1900 (2003)
Wang, Y., Wang, C.: Modeling the effects of timing parameters on virus propagation. In: WORM 2003, Washington, DC, USA, pp. 61–66 (2003)
Rohloff, K., Basar, T.: Stochastic behavior of random constant scanning worms. In: The 14th ICCCN, San Diego, CA, USA, pp. 339–344 (2005)
Daley, D.J., Gani, J.: Epidemic Modelling: An Introduction. Cambridge University Press, Cambridge (1999)
Andersson, H., Britton, T.: Stochastic Epidemic Models and their Statistical Analysis. Springer, New York (2000)
Sellke, S., Shroff, N.B., Bagchi, S.: Modeling and automated containment of worms. In: DSN 2005, pp. 528–537 (2005)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2011 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Wang, Y., Wen, S., Zhou, W., Zhou, W., Xiang, Y. (2011). The Probability Model of Peer-to-Peer Botnet Propagation. In: Xiang, Y., Cuzzocrea, A., Hobbs, M., Zhou, W. (eds) Algorithms and Architectures for Parallel Processing. ICA3PP 2011. Lecture Notes in Computer Science, vol 7016. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-24650-0_41
Download citation
DOI: https://doi.org/10.1007/978-3-642-24650-0_41
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-24649-4
Online ISBN: 978-3-642-24650-0
eBook Packages: Computer ScienceComputer Science (R0)