Abstract
Recent research has shown that using public-key cryptography in order to meet privacy requirements for RFID tags is not only necessary, but also now practically feasible. This has led to the development of new protocols like the Randomized Schnorr [6] identification protocol. This protocol ensures that the identity of a tag only becomes known to authorised readers.
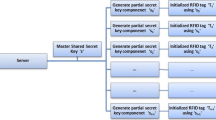
In this paper we generalize this protocol by introducing an attribute-based identification scheme. The proposed scheme preserves the designation of verification (i.e., only an authorised reader is able to learn the identity of a tag) while it allows tags to prove any subset of their attributes to authorised readers. The proposed scheme is proven to be secure and narrow-strong private.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Batina, L., Lee, Y.K., Seys, S., Singelée, D., Verbauwhede, I.: Privacy-Preserving ECC-Based Grouping Proofs for RFID. In: Burmester, M., Tsudik, G., Magliveras, S., Ilić, I. (eds.) ISC 2010. LNCS, vol. 6531, pp. 159–165. Springer, Heidelberg (2011)
Batina, L., Lee, Y.K., Seys, S., Singelée, D., Verbauwhede, I.: Extending ECC-based RFID authentication protocols to privacy-preserving multi-party grouping proofs. Personal and Ubiquitous Computing 16(3), 323–335 (2012)
Batina, L., Seys, S., Singelée, D., Verbauwhede, I.: Hierarchical ECC-Based RFID Authentication Protocol. In: Juels, A., Paar, C. (eds.) RFIDSec 2011. LNCS, vol. 7055, pp. 183–201. Springer, Heidelberg (2012)
Brands, S.A.: Rethinking Public Key Infrastructures and Digital Certificates: Building in Privacy. MIT Press, Cambridge (2000)
Braun, M., Hess, E., Meyer, B.: Using Elliptic Curves on RFID Tags. IJCSNS International Journal of Computer Science and Network Security 8(2), 1–9 (2008)
Bringer, J., Chabanne, H., Icart, T.: Cryptanalysis of EC-RAC, a RFID Identification Protocol. In: Franklin, M.K., Hui, L.C.K., Wong, D.S. (eds.) CANS 2008. LNCS, vol. 5339, pp. 149–161. Springer, Heidelberg (2008)
Camenisch, J., Krontiris, I., Lehmann, A., Neven, G., Paquin, C., Rannenberg, K., Harald, Z.: D2.1 Architecture for Attribute-based Credential Technologies. Deliverable, ABC4Trust EU Project (December 2011)
Chaum, D.: Zero-Knowledge Undeniable Signatures (extended abstract). In: Damgård, I.B. (ed.) EUROCRYPT 1990. LNCS, vol. 473, pp. 458–464. Springer, Heidelberg (1991)
Chaum, D., van Antwerpen, H.: Undeniable Signatures. In: Brassard, G. (ed.) CRYPTO 1989. LNCS, vol. 435, pp. 212–216. Springer, Heidelberg (1990)
Fan, J., Knezevic, M., Karaklajic, D., Maes, R., Rozic, V., Batina, L., Verbauwhede, I.: FPGA-based testing strategy for cryptographic chips: A case study on Elliptic Curve Processor for RFID tags. In: 15th IEEE International On-Line Testing Symposium (IOLTS 2009), Sesimbra-Lisbon, Portugal, June 24-26, pp. 189–191. IEEE (2009)
Hein, D., Wolkerstorfer, J., Felber, N.: ECC Is Ready for RFID – A Proof in Silicon. In: Avanzi, R.M., Keliher, L., Sica, F. (eds.) SAC 2008. LNCS, vol. 5381, pp. 401–413. Springer, Heidelberg (2009)
Jakobsson, M., Sako, K., Impagliazzo, R.: Designated Verifier Proofs and Their Applications. In: Maurer, U.M. (ed.) EUROCRYPT 1996. LNCS, vol. 1070, pp. 143–154. Springer, Heidelberg (1996)
Juels, A.: “Yoking-Proofs” for RFID Tags. In: Proceedings of the Second IEEE Annual Conference on Pervasive Computing and Communications Workshops (PERCOMW 2004), pp. 138–143. IEEE Computer Society (2004)
Koblitz, N.: Elliptic curve cryptosystems. Mathematics of Computation 48, 203–209 (1987)
Lee, Y.K., Batina, L., Singelée, D., Verbauwhede, I.: Low-Cost Untraceable Authentication Protocols for RFID. In: Proceedings of the Third ACM Conference on Wireless Network Security, WiSec 2010, pp. 55–64. ACM, New York (2010)
Paquin, C.: U-Prove Cryptographic Specification V1.1. Technical report, Microsoft (2011)
Saeednia, S., Kremer, S., Markowitch, O.: An Efficient Strong Designated Verifier Signature Scheme. In: Lim, J.-I., Lee, D.-H. (eds.) ICISC 2003. LNCS, vol. 2971, pp. 40–54. Springer, Heidelberg (2004)
Schnorr, C.-P.: Efficient Identification and Signatures for Smart Cards. In: Brassard, G. (ed.) CRYPTO 1989. LNCS, vol. 435, pp. 239–252. Springer, Heidelberg (1990)
Vaudenay, S.: On Privacy Models for RFID. In: Kurosawa, K. (ed.) ASIACRYPT 2007. LNCS, vol. 4833, pp. 68–87. Springer, Heidelberg (2007)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Alpár, G., Batina, L., Lueks, W. (2013). Designated Attribute-Based Proofs for RFID Applications. In: Hoepman, JH., Verbauwhede, I. (eds) Radio Frequency Identification. Security and Privacy Issues. RFIDSec 2012. Lecture Notes in Computer Science, vol 7739. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-36140-1_5
Download citation
DOI: https://doi.org/10.1007/978-3-642-36140-1_5
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-36139-5
Online ISBN: 978-3-642-36140-1
eBook Packages: Computer ScienceComputer Science (R0)