Abstract
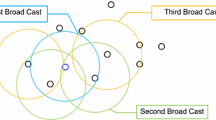
As the capabilities of mobile technology such as PDAs, smartphones and tablets increases, theoretical ideas are materializing. One of these ideas under active development is a infrastructure free network, based solely on mobile devices (a.k.a. MANET - mobile ad hoc network). These networks would have the ability of running communications without the use of pre-existing infrastructure, allowing for a reduction of cost to carriers, setting up communication networks where no infrastructure is available (like disaster zones), etc. In this paper we propose an algorithm, based on the famous Diffie-Hellman key exchange (KE) algorithm, that will provide for confidentiality of KE during conversation initiation, from which a cryptographically secure channel can later be derived. The algorithm utilizes the constant fluctuation of MANET network topology to flush-out eavesdroppers (if they exist), assuming no prior knowledge and without active user intervention.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Alljoyn (2012), https://developer.qualcomm.com/mobile-development/mobile-technologies/peer-peer-alljoyn.Qualcomm , https://developer.qualcomm.com/mobile-development/mobile-technologies/p%eer-peer-alljoyn
The serval project (2010), http://www.servalproject.org/ (access date: September 6, 2012)
Rescorla, E.: Diffie-Hellman Key Agreement Method. RFC 2631 (Proposed Standard), Internet Engineering Task Force (June 1999), http://www.ietf.org/rfc/rfc2631.txt (access date: September 6, 2012)
Clausen, T., Jacquet, P.: Optimized Link State Routing Protocol (OLSR). RFC 3626 (Experimental), Internet Engineering Task Force (October 2003), http://www.ietf.org/rfc/rfc3626.txt (access Date: September 6, 2012)
Postel, J.: Internet Protocol. RFC 791 (Standard), Internet Engineering Task Force, updated by RFC 1349 (September 1981), http://www.ietf.org/rfc/rfc791.txt (access Date: September 6, 2012)
Cooper, D., Santesson, S., Farrell, S., Boeyen, S., Housley, R., Polk, W.: Internet X.509 Public Key Infrastructure Certificate and Certificate Revocation List (CRL) Profile. RFC 5280 (Proposed Standard), Internet Engineering Task Force (May 2008), http://www.ietf.org/rfc/rfc5280.txt (access date: September 6, 2012)
Freier, A., Karlton, P.: The Secure Sockets Layer (SSL) Protocol Version 3.0. RFC 6101 (Proposed Standard), Internet Engineering Task Force (August 2011), http://www.ietf.org/rfc/rfc6101.txt (access date: September 6, 2012)
Dierks, T., Rescorla, E.: The Transport Layer Security (TLS) Protocol Version 1.2. RFC 5246 (Proposed Standard), Internet Engineering Task Force, updated by RFCs 5746, 5878. (August 2008), http://www.ietf.org/rfc/rfc5246.txt (access date: September 6, 2012)
Ylonen, T., Lonvick, C.: The Secure Shell (SSH) Protocol Architecture. RFC 4251 (Proposed Standard), Internet Engineering Task Force (January 2006), http://www.ietf.org/rfc/rfc4251.txt (access date: September 6, 2012)
Kent, S., Seo, K.: Security Architecture for the Internet Protocol. RFC 4301 (Proposed Standard), Internet Engineering Task Force (December 2005), http://www.ietf.org/rfc/rfc4301.txt (access date: September 6, 2012)
Diffie, W., Hellman, M.E.: New directions in cryptography. IEEE Transactions on Information Theory 22(6), 644–654 (1976)
Hellman, M., Diffie, W., Merkle, R.: Cryptographic apparatus and method. USA Patent 4 200 770 (April 29, 1980)
Rivest, R.L., Shamir, A.: How to expose an eavesdropper. Commun. ACM 27(4), 393–394 (1984), http://doi.acm.org/10.1145/358027.358053 (access date: September 6, 2012)
O’Higgins, B., Diffie, W., Strawczynski, L., de Hoog, R.: Encryption and isdn - a natural fit. In: Proc. ISS 1987, Pheonix, March 15-20, pp. 863–869 (1987)
Zimmermann, P., Johnston, A., Callas, J.: ZRTP: Media Path Key Agreement for Unicast Secure RTP. RFC 6189 (Proposed Standard), Internet Engineering Task Force (April 2011), http://www.ietf.org/rfc/rfc6189.txt (access date: September 6, 2012)
Diffie, W., Van Oorschot, P.C., Wiener, M.J.: Authentication and authenticated key exchanges. Des. Codes Cryptography 2(2), 107–125 (1992), http://dx.doi.org/10.1007/BF00124891 (access date: September 6, 2012)
ser. Cryptologic Quarterly, vol. 26(4), United States’ National Security Agency, NSA (2007)
Cusack, F., Forssen, M.: Generic Message Exchange Authentication for the Secure Shell Protocol (SSH). RFC 4256 (Proposed Standard), Internet Engineering Task Force (January 2006), http://www.ietf.org/rfc/rfc4256.txt (access date: September 6, 2012)
ERK. On the security of short authentication strings (March 2007), http://www.imc.org/ietf-rtpsec/mail-archive/msg00608.html (access date: September 6, 2012)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Stulman, A., Lahav, J., Shmueli, A. (2013). Spraying Diffie-Hellman for Secure Key Exchange in MANETs. In: Christianson, B., Malcolm, J., Stajano, F., Anderson, J., Bonneau, J. (eds) Security Protocols XXI. Security Protocols 2013. Lecture Notes in Computer Science, vol 8263. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-41717-7_24
Download citation
DOI: https://doi.org/10.1007/978-3-642-41717-7_24
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-41716-0
Online ISBN: 978-3-642-41717-7
eBook Packages: Computer ScienceComputer Science (R0)