Abstract
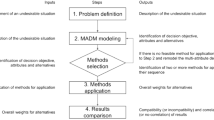
Based on the research of information security and business continuity management, a key business node identification model for the business process based on AE-VIKOR (Analytic hierarchy process and Entropy weighting VIKOR, AE-VIKOR) method is proposed. Firstly, the business nodes are obtained based on the business process, and the importance decision matrix of business nodes is constructed by quantifying the evaluation attributes of nodes. Secondly, the attribute weight is improved from subjective and objective dimensions to form the combination weight decision matrix, and the AE-VIKOR method is used to calculate the business importance coefficient to identify the key nodes. Finally, when an information security event occurs in the system, the impact of key business nodes on business continuity is analyzed, and the business continuity risk value is calculated to evaluate the business risk to prove the effectiveness of the model. The experimental results of civil aviation departure control system show that the AE-VIKOR method can effectively identify key business nodes, and the impact of key business nodes on business continuity is analyzed, which further proves the efficiency and accuracy of the model.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Moldagulova, A., Uskenbayeva, R.K., Satybaldiyeva, R.Z., Kamennova, M.S., Kalpeeva, Z.B., Bektemyssova, G.U.: On identification of hybrid business processes for effective implementation in the form of cloud services. In: 2019 19th International Conference on Control, Automation and Systems (ICCAS), pp. 51–54, IEEE, Jeju (2019)
Sherzod, G., Abdukhalil, G., Viktoriya, V.: Formalization of the business process security. In: 2019 International Conference on Information Science and Communications Technologies (ICISCT), pp. 1–3. IEEE, Tashkent (2019)
Ming, Q., Songtao, L.: Overview of system wide information management and security analysis. In: 2017 IEEE 13th International Symposium on Autonomous Decentralized System (ISADS), pp. 191–194, IEEE, Bangkok (2017)
Stergiopoulos, G., Dedousis, P., Gritzalis, D.: Automatic network restructuring and risk mitigation through business process asset dependency analysis. Comput. Secur. 96, 101869 (2020)
Matulevičius, R., Norta, A., Samarütel, S.: Security requirements elicitation from airline turnaround processes. Bus. Inf. Syst. Eng. 60, 3–20 (2018)
Torabi, S., Giahi, R., Sahebjamnia, N.: An enhanced risk assessment framework for business continuity management systems. Saf. Sci. 89, 201–218 (2016)
Belov, V.M., Pestunov, A.I., Pestunova, T.M.: On the issue of information security risks assessment of business processes. In: Proceedings of the 14th International Scientific-Technical Conference on Actual Problems of Electronics Instrument Engineering APEIE, pp. 136–139. IEEE, Piscataway (2018)
Hariyanti, E., Djunaidy, A., Siahaan, D.O.: A conceptual model for information security risk considering business process perspective. In: 2018 4th International Conference on Science and Technology (ICST), pp. 1–6. IEEE (2018)
Yang, J., Han, J., Zhang, X.: Information system security risk assessment based on IDAV multi-criteria decision model. In: 2018 12th IEEE International Conference on Anti-counterfeiting, Security, and Identification (ASID), pp. 121–127. IEEE, Xiamen (2018)
Shen, Y., Gu, C., Zhao, P.: Structural vulnerability assessment of multi-energy system using a pagerank algorithm. Energy Procedia 158, 6466–6471 (2019)
Piwowarski, M., Danuta, M., Małgorzata, Ł., Mariusz, B., Kesra, N.: TOPSIS and VIKOR methods in study of sustainable development in the EU countries. Procedia Comput. Sci. 126, 1683–1692 (2018)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Xie, L., Ni, H., Xu, G., Zhang, J. (2020). A Key Business Node Identification Model for Business Process Based on AE-VIKOR Method. In: Xu, G., Liang, K., Su, C. (eds) Frontiers in Cyber Security. FCS 2020. Communications in Computer and Information Science, vol 1286. Springer, Singapore. https://doi.org/10.1007/978-981-15-9739-8_47
Download citation
DOI: https://doi.org/10.1007/978-981-15-9739-8_47
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-15-9738-1
Online ISBN: 978-981-15-9739-8
eBook Packages: Computer ScienceComputer Science (R0)