Abstract
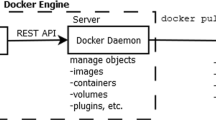
Containers are a popular technology that helps build portable and scalable applications. They use lightweight virtualization that wraps an application with all its dependencies, binaries and libraries. They are also isolated, and therefore, useful in systems that host multiple applications. The security of these containers is an important, yet widely overlooked, aspect of container deployment and maintenance. Since the use of containers is extensive and only growing, a weak security framework can lead to vulnerable containers and in some cases, vulnerable hosts as well. Though guidelines such as the CIS benchmark exist, they are too broad as they harden the entire container without accounting for the compatibility of the security measures with the functionality of the application. It is often observed that on hardening the container, the functionality is hindered and the container, though now secure, is unable to perform the task it was created for. Thus, selecting which parts of the benchmark to apply and which to skip is a crucial part of developing a hardening policy. This paper deals with hardening containers, specifically those provided by a company that we shall not name. This is done by analyzing the image statically (before it is deployed) and then dynamically (while it is running). The results are then used and analyzed to create a hardening policy for the containers.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Jagelid, M.: Container vulnerability scanners: an analysis [Internet] [Dissertation]. (KTH ) (TRITA-EECS-EX) (2020). http://urn.kb.se/resolve?urn=urn:nbn:se:kth:diva-279967
Sultan, S., Ahmad, I., Dimitriou, T.: Container security: issues, challenges, and the road ahead. IEEE Access 7, 52976–52996 (2019). https://doi.org/10.1109/ACCESS.2019.2911732
X. Wang, Q., Shen, W., Luo, P., Wu.: RSDS: Getting System Call Whitelist for Container Through Dynamic and Static Analysis. In: 2020 IEEE 13th International Conference on Cloud Computing (CLOUD), pp. 600–608, (2020) https://doi.org/10.1109/CLOUD49709.2020.00089
Gantikow, Holger, Reich, Christoph, Knahl, Martin, Clarke, Nathan. Rule-based Security Monitoring of Containerized Workloads. 543–550. (2019) https://doi.org/10.5220/0007770005430550
Loukidis-Andreou, F., Giannakopoulos, I., Doka K., Koziris, N.:Docker-Sec: A Fully Automated Container Security Enhancement Mechanism. In: 2018 IEEE 38th International Conference on Distributed Computing Systems (ICDCS), pp. 1561–1564, (2018) https://doi.org/10.1109/ICDCS.2018.00169.
Aqua Security: https://github.com/aquasecurity/trivy
Claire: https://www.redhat.com/en/topics/containers/what-is-clair
Ghavamnia, Seyedhamed, Palit, Tapti, Benameur, Azzedine, Polychronakis, Michalis. Confine: Automated system call policy generation for container attack surface reduction (2020)
Docker Bench Security: https://github.com/docker/docker-bench- security
CIS benchmarks: https://www.cisecurity.org/benchmark/docker/
https://opensource.com/article/18/8/tools-container-security
https://medium.com/karthi.net/8-best-docker-security-tools- de7f514aa94d
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Patil, S.R.K., John, N., Kunja, P.S., Dwivedi, A., Suganthi, S., Honnnavali, P.B. (2023). Hardening Containers with Static and Dynamic Analysis. In: Onwubiko, C., et al. Proceedings of the International Conference on Cybersecurity, Situational Awareness and Social Media. Springer Proceedings in Complexity. Springer, Singapore. https://doi.org/10.1007/978-981-19-6414-5_12
Download citation
DOI: https://doi.org/10.1007/978-981-19-6414-5_12
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-19-6413-8
Online ISBN: 978-981-19-6414-5
eBook Packages: Physics and AstronomyPhysics and Astronomy (R0)