Abstract
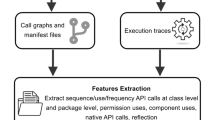
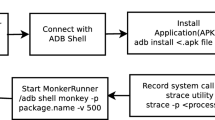
Android, the most popular operating system in the mobile market, is the main target of hackers. The dynamic analysis in malware analysis is not affected by obfuscation and dynamic loading attacks. Therefore, this study uses a dynamic detection approach and uses system calls as a feature to represent the behaviour of an application. The TF-IDF feature processing method can assign different weights to the system call features according to the number of occurrences and the overall relationship, but this method uses one system call as a unit and therefore does not calculate the pre- and post- sequence relationships, which are important in system call sequences. This study uses the concept of n-grams to form system call groups combined with local TF-IDF to allow sequence-based data to be characterised by the pre-post relationship and importance of the sequences, and to analyse Android applications on a deep learning model that has shown excellent classification results in the field of malware detection. In this study, it is shown that this method improves the accuracy of multiple classification of apps by more than 3% and 11% for the unknown 2019 dataset.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Kaspersky: IT threat evolution Q3 2021. Mobile statistics (2021). https://securelist.com/it-threat-evolution-in-q3-2021-mobile-statistics/105020/
StatCounter: Mobile Operating System Market Share Worldwide (2022). https://gs.statcounter.com/os-market-share/mobile/worlwide/#monthly-202101-202203-bar
Saracino, A., Sgandurra, D., Dini, G., Martinelli, F.: MADAM: Effective and Efficient Behavior-based Android Malware Detection and Prevention (2016)
Feng, P., Ma, J., Sun, C., Xu, X., Ma, Y.: A novel dynamic android malware detection system with ensemble learning. IEEE Trans. Depend. Secur. Comput. 20, 1–10 (2018)
Liu, Y.-C.: A call sequence compression method for local weighting system using mobile malware detection. Master's thesis, Institute of Information Management, National Central University (2021)
Martín, A., Lara-Cabrera, R., Camacho, D.: Android malware detection through hybrid features fusion and ensemble classifiers: the AndroPyTool framework and the OmniDroid dataset. Inf. Fusion 52, 128–142 (2019). https://doi.org/10.1016/j.inffus.2018.12.006
pjlantz. Github-pjlantz/Droidbox: Dynamic analysis of Android apps. https://github.com/pjlantz/droidbox
Yan, J., Qi, Y., Rao, Q.: LSTM-based hierarchical denoising network for android malware detection. Secur. Commun. Netw. 2018, 1–18 (2018). https://doi.org/10.1155/2018/5249190
Mas’ud, M.Z.: A comparative study on feature selection method for N-gram mobile malware detection. Int. J. Netw. Secur. 19(5), 727–733 (2017)
Jahromi, A.N., Hashemi, S., Dehghantanha, A., Parizi, R.M., Choo, K.-K.R.: An enhanced stacked LSTM method with no random initialization for malware threat hunting in safety and time-critical systems. IEEE Trans. Emerg. Topics Comput. Intell. 4(5), 630–640 (2020)
Chen, Y.M., Hsu, C.H., Chung, K.C.K.: A novel preprocessing method for solving long sequence problem in android malware detection. In: 2019 Twelfth International Conference on Ubi-Media Computing (Ubi- Media), pp. 12–17. IEEE, August 2019
Xie, W., Xu, S., Zou, S., Xi, J.: A system-call behavior language system for malware detection using a sensitivity-based LSTM model. In: Proceedings of the 2020 3rd International Conference on Computer Science and Software Engineering, pp. 112–118 (2020)
Vaswani, A., et al.: Attention is all you need. In: Advances in Neural Information Processing Systems, pp. 5998–6008 (2017)
Graves, A.: Supervised sequence labelling with recurrent neural networks, pp. 37–45 (2012)
Yong, Y., Si, X., Hu, C., Zhang, J.: A review of recurrent neural networks: LSTM cells and network architectures. Neural Comput. 31(7), 1235–1270 (2019). https://doi.org/10.1162/neco_a_01199
Xiao, X., Zhang, S., Mercaldo, F., Hu, G., Sangaiah, A.K.: Android malware detection based on system call sequences and LSTM. Multimed. Tools App. 78(4), 3979–3999 (2017). https://doi.org/10.1007/s11042-017-5104-0
Chen, Y.M., He, A.C., Chen, G.C., Liu, Y.C.: Android malware detection system integrating block feature extraction and multi- head attention mechanism, pp. 408–413. IEEE (2020)
Mahdavifar, S., Kadir, A.F.A., Fatemi, R., Alhadidi, D., Ghorbani, A.A.: dynamic android malware category classification using semi-supervised deep learning. In: 2020 IEEE International Conference on Dependable, Autonomic and Secure Computing, International Conference on Pervasive Intelligence and Computing, International Conference on Cloud and Big Data Computing, International Conference on Cyber Science and Technology Congress (DASC/PiCom/CBDCom/CyberSciTech), pp. 515–522. IEEE (2020)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Hung, CH., Chen, Ym., Wu, CC. (2022). Detecting Android Malware by Combining System Call Sequence Relationships with Local Feature Calculation. In: Hsieh, SY., Hung, LJ., Klasing, R., Lee, CW., Peng, SL. (eds) New Trends in Computer Technologies and Applications. ICS 2022. Communications in Computer and Information Science, vol 1723. Springer, Singapore. https://doi.org/10.1007/978-981-19-9582-8_32
Download citation
DOI: https://doi.org/10.1007/978-981-19-9582-8_32
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-19-9581-1
Online ISBN: 978-981-19-9582-8
eBook Packages: Computer ScienceComputer Science (R0)