Abstract
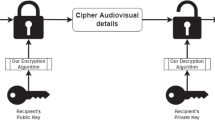
Nowadays, urban and vehicular surveillance systems are collecting large amounts of image data for feeding recognition systems, for example, toward proposing localization or navigation services. In many cases, these image data cannot directly be processed in situ by the acquisition systems in reason of their low computational capabilities. The acquired images are transferred to remote computing servers through various computer networks, and then analyzed in details toward object recognition. The objective of this paper is twofold (i) presenting image-based ciphering methods that can efficiently be applied for securing the image transfer against consequences of image interceptions (e.g., man-in-the-middle attacks) (ii) presenting generic image-based analysis techniques that can be exploited for object recognition. Experimental results show end-to-end image-based solutions for fostering developments of surveillance systems and services in urban and vehicular environments.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Abu Taha, M., El Assad, S., Jallouli, O., Queudet, A., Deforges, O.: Design of a pseudo-chaotic number generator as a random number generator. In: International Conference on Communications (COMM) (2016). https://doi.org/10.1109/ICComm.2016.7528291
Abu Taha, M., El Assad, S., Queudet, A., Deforges, O.: Design and efficient implementation of a chaos-based stream cipher. Int. J. Internet Technol. Secured Trans. 7(2) (2017). https://doi.org/10.1504/IJITST.2017.087131
Abu Taha, M.: Real-Time and Portable Chaos-based Crypto-Compression Systems for Efficient Embedded Architectures, Ph.D. Thesis, Université de Nantes (2017). https://www.theses.fr/2017NANT4010
Almeida, P., Oliveira, L.S., Silva, Jr., E., Britto, Jr., A., Koerich, A.: PKLot A robust dataset for parking lot classification. Expert Syst. Appl. 42(11), 4937–4949 (2015). https://doi.org/10.1016/j.eswa.2015.02.009
Conti, M., Dragoni, N., Lesyk, V.: A survey of man in the middle attacks. IEEE Commun. Surv. Tutorials 18(3) (2016). https://doi.org/10.1109/COMST.2016.2548426
Hammoudi, K., Benhabiles, H., Melkemi, M., Dornaika, F.: Detection systems for improving the citizen security and comfort from urban and vehicular surveillance technologies: an overview. In: International Conference on ICT Infrastructures and Services for Smart Cities. Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering, vol. 189. Springer, Berlin (2018). https://doi.org/10.1007/978-3-319-67636-4_5
Hammoudi, K., Cabani, A., Melkemi, M., Benhabiles, H., Windal, F.: Towards a model of car parking assistance system using camera networks: slot analysis and communication management. In: IEEE International Conference on Smart City 2018
Hammoudi, K., Melkemi, M., Dornaika, F., Benhabiles, H., Windal, F., Taoufik, O.: A comparative study of 2 resolution-level LBP descriptors and compact versions for visual analysis. In: FutureTech. Advanced Multimedia and Ubiquitous Engineering, LNEE. Springer, Berlin (2019). https://doi.org/10.1007/978-981-13-1328-8_28
Hammoudi, K., Melkemi, M., Dornaika, F., Phan, T.D.A., Taoufik O.: Computing multi-purpose image-based descriptors for object detection: powerfulness of LBP and its variants. In: International Congress on Information and Communication Technology. Advances in Intelligent Systems and Computing, vol. 797. Springer, Berlin (2018). https://doi.org/10.1007/978-981-13-1165-9_90
Huang, Y., Jin, L., Li, N., Zhong, Z., Xu, X.: Secret key generation based on private pilot under man-in-the-middle attack. In: Science China Information Sciences, Springer (2017). https://doi.org/10.1007/s11432-017-9195-3
Liu, L., Fieguth, P., Guo, Y., Wang, X., Pietikainen, M.: Local binary features for texture classification: taxonomy and experimental study. In: Pattern Recognition, vol. 62 (2017)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Hammoudi, K. et al. (2020). Image-Based Ciphering of Video Streams and Object Recognition for Urban and Vehicular Surveillance Services. In: Yang, XS., Sherratt, S., Dey, N., Joshi, A. (eds) Fourth International Congress on Information and Communication Technology. Advances in Intelligent Systems and Computing, vol 1027. Springer, Singapore. https://doi.org/10.1007/978-981-32-9343-4_42
Download citation
DOI: https://doi.org/10.1007/978-981-32-9343-4_42
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-32-9342-7
Online ISBN: 978-981-32-9343-4
eBook Packages: EngineeringEngineering (R0)