Abstract
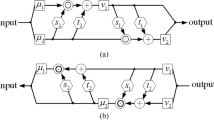
Deep hiding involves embedding a secret image within a cover image so that the secret becomes imperceptible to ensure the security of steganography. However, in practical applications, accuracy loss is due to data conversion during encoding and decoding. The encoder generates the tensor matrix during training, while the practical application corresponds to the image preservation extraction process; the error caused by the rounding operation in this process will affect the accuracy of the secret information extraction during decoding. Aiming at the currently existing methods ignoring the rounding error problem, this paper proposes a novel anti-rounding image steganography method for improved UNet++. We design an anti-rounding function (ARF) to simulate the real steganographic environment, training the model to overcome the non-differentiable rounding distortion problem. When rounding error is considered, the accuracy of the extracted image decreases. To ensure the image quality in real application scenarios, in this paper, we use the improved UNet++ to ensure the quality of steganographic images by cascading convolution and ECA attention mechanisms and propose the Multiscale Mixing Module (MSMM) for feature fusion. In the extraction stage, the corresponding cover image is selected through a shared cover image library, followed by processing the stego image to obtain a different image before feeding it to the extraction network to guarantee the steganography process’s safety. The experiment results indicate the method’s capability to enhance the imperceptibility of steganography significantly, and the steganography process has better security.
Supported by Key Scientific Research Projects of Universities in Henan Province (No.23A520006); Science and Technology Project of Henan Province (No.222102210199).
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Johnson, N.F., Jajodia, S.: Exploring steganography: seeing the unseen. Computer 31(2), 26–34 (1998)
Katzenbeisser, S., Petitcolas, F.A.: Defining security in steganographic systems. In: Security and Watermarking of Multimedia Contents IV, vol. 4675, pp. 50–56. SPIE (2002)
Baluja, S.: Hiding images in plain sight: deep steganography. Adv. Neural Inf. Process. Syst. 30 (2017)
Baluja, S.: Hiding images within images. IEEE Trans. Pattern Anal. Mach. Intell. 42(7), 1685–1697 (2019)
Duan, X., Wang, W., Liu, N., Yue, D., Xie, Z., Qin, C.: Stegopnet: image steganography with generalization ability based on pyramid pooling module. IEEE Access 8, 195253–195262 (2020)
Zhang, C., Benz, P., Karjauv, A., Sun, G., Kweon, I.S.: Udh: Universal deep hiding for steganography, watermarking, and light field messaging. Adv. Neural. Inf. Process. Syst. 33, 10223–10234 (2020)
Jing, J., Deng, X., Xu, M., Wang, J., Guan, Z.: Hinet: deep image hiding by invertible network. In: Proceedings of the IEEE/CVF International Conference on Computer Vision, pp. 4733–4742 (2021)
Yin, X., Wu, S., Wang, K., Lu, W., Zhou, Y., Huang, J.: Anti-rounding image steganography with separable fine-tuned network. IEEE Trans. Circuits Syst. Video Technol. (2023)
Fridrich, J., Goljan, M., Du, R.: Reliable detection of LSB steganography in color and grayscale images. In: Proceedings of the 2001 Workshop on Multimedia and Security: New Challenges, pp. 27–30 (2001)
Chefranov, A.G., Öz, G.: Adaptive to pixel value and pixel value difference irreversible spatial data hiding method using modified LSB for grayscale images. J. Inf. Secur. Appl. 70, 103314 (2022)
Holub, V., Fridrich, J., Denemark, T.: Universal distortion function for steganography in an arbitrary domain. EURASIP J. Inf. Secur. 2014, 1–13 (2014)
Zhang, W., Zhang, Z., Zhang, L., Li, H., Yu, N.: Decomposing joint distortion for adaptive steganography. IEEE Trans. Circuits Syst. Video Technol. 27(10), 2274–2280 (2016)
Su, W., Ni, J., Li, X., Shi, Y.Q.: A new distortion function design for jpeg steganography using the generalized uniform embedding strategy. IEEE Trans. Circuits Syst. Video Technol. 28(12), 3545–3549 (2018)
Po-Yueh, P.Y., Lin, H.J., et al.: A dwt based approach for image steganography. Int. J. Appl. Sci. Eng. 4(3), 275–290 (2006)
Walia, E., Jain, P., Navdeep, N.: An analysis of LSB & DCT based steganography. Global J. Comp. Sci. Technol. 10(1), 4–8 (2010)
Wang, Y., Moulin, P.: Statistical modeling and steganalysis of DFT-based image steganography. In: Security, Steganography, and Watermarking of Multimedia Contents VIII, vol. 6072, pp. 14–24. SPIE (2006)
Liu, L., Meng, L., Wang, X., Peng, Y.: An image steganography scheme based on resnet. Multimed. Tools Appl. 81(27), 39803–39820 (2022)
Zhu, X., Lai, Z., Liang, Y., Xiong, J., Wu, J.: Generative high-capacity image hiding based on residual CNN in wavelet domain. Appl. Soft Comput. 115, 108170 (2022)
Goodfellow, I., Pouget-Abadie, J., Mirza, M., Xu, B., Warde-Farley, D., Ozair, S., Courville, A., Bengio, Y.: Generative adversarial networks. Commun. ACM 63(11), 139–144 (2020)
Hayes, J., Danezis, G.: Generating steganographic images via adversarial training. Adv. Neural Inf. Process. Syst. 30 (2017)
Tan, J., Liao, X., Liu, J., Cao, Y., Jiang, H.: Channel attention image steganography with generative adversarial networks. IEEE Trans. Netw. Sci. Eng. 9(2), 888–903 (2021)
Deng, J., Dong, W., Socher, R., Li, L.J., Li, K., Fei-Fei, L.: Imagenet: a large-scale hierarchical image database. In: 2009 IEEE Conference on Computer Vision and Pattern Recognition, pp. 248–255. Ieee (2009)
Liu, Z., Luo, P., Wang, X., Tang, X.: Large-scale celebfaces attributes (celeba) dataset. Retrieved August 15(2018) (Nov 2018)
Lin, T.Y., et al.: Microsoft COCO: common objects in context. In: Fleet, D., Pajdla, T., Schiele, B., Tuytelaars, T. (eds.) Computer Vision – ECCV 2014. ECCV 2014. Lecture Notes in Computer Science, vol. 8693. Springer, Cham (2014). https://doi.org/10.1007/978-3-319-10602-1_48
Nilsback, M.E., Zisserman, A.: Automated flower classification over a large number of classes. In: 2008 Sixth Indian Conference on Computer Vision, Graphics & Image Processing, pp. 722–729. IEEE (2008)
Hore, A., Ziou, D.: Image quality metrics: PSNR vs. SSIM. In: 2010 20th International Conference on Pattern Recognition, pp. 2366–2369. IEEE (2010)
Johnson, J., Alahi, A., Fei-Fei, L.: Perceptual losses for real-time style transfer and super-resolution. In: Leibe, B., Matas, J., Sebe, N., Welling, M. (eds.) Computer Vision – ECCV 2016. ECCV 2016. Lecture Notes in Computer Science, vol. 9906. Springer, Cham (2016). https://doi.org/10.1007/978-3-319-46475-6_43
Boroumand, M., Chen, M., Fridrich, J.: Deep residual network for steganalysis of digital images. IEEE Trans. Inf. Forensics Secur. 14(5), 1181–1193 (2018)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2025 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Duan, X. et al. (2025). A Novel Anti-rounding Image Steganography Method for Improved UNet++. In: Lin, Z., et al. Pattern Recognition and Computer Vision. PRCV 2024. Lecture Notes in Computer Science, vol 15039. Springer, Singapore. https://doi.org/10.1007/978-981-97-8692-3_23
Download citation
DOI: https://doi.org/10.1007/978-981-97-8692-3_23
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-97-8691-6
Online ISBN: 978-981-97-8692-3
eBook Packages: Computer ScienceComputer Science (R0)