Abstract
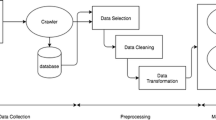
Even though there are many reliable online merchants these days, scammers can still prey on unsuspecting clients by using the Internet's anonymity. Using the most latest technologies, scammers produce fraudulent retailer apps that mimic genuine online retail sites. They might utilize complex patterns and designs. Numerous of these applications provide exceptionally inexpensive prices on premium goods including renowned jewelry, clothing, and technology companies. Sometimes you might receive what you paid for, but it might be a fake or you might not receive anything at all. Money orders, pre-loaded cards, and wire transfers are common payment methods requested by con artists, but it is doubtful that you will receive your order or see your money again if you send it this way. Con artists frequently ask for money orders, pre-loaded cards, and wire transfers as payment, but it is unlikely that you will receive your order or see your money again if you send it this way. Social networking sites are now being used to establish fake online storefronts in a more recent iteration of online retail scams. They briefly launch the company and frequently sell counterfeit trademark jewelry or clothing. Several sales later, the stores are gone. Because they also use social media to promote their fake app, we shouldn’t believe something just because we have seen it advertised or shared there. There is a need to mark these submissions. The experiment's fundamental pillars are three dimensions: feature extraction, selection, and malware prediction.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Market Share of Smartphones [Online]. [Fetched: April 30 2020]
Aggregate of Android applications on Google Play [Online]. [Fetched: 30 April 2020]
Li, J., Sun, L., Yan, Q., Li, Z., Srisa-an, W., Ye, H.: Machine-learning-based Android malware detection based on significant permission identification. IEEE Trans. Ind. Inform. 14(7), 3216–3225 (2018)
Sufatrio, Tan, D.J.J., Chua, T.W., Thing, V.L.L.: Securing android: a survey, problems, and taxonomy. ACM Comput. Surv. 47(4), 58(45pp) (2015)
Qing, S.H.: Android security research progress. Softw. J. 27(1), 45–71 (2016)
Lopes, J., Serrao, C., Nunes, L., Almeida, A., Oliveira, J.: An outline of machine learning algorithms for malware identification in android. In: 7th International Symposium on Digital Forensics and Security (ISDFS), Barcelos, Portugal, pp. 1–6 (2019)
Choudhary, M., Kishore, B.: HAAMD: hybrid analysis for android malware detection. In: Activities of the 2018 International Conference on Computer Communications and Informatics (ICCCI), Coimbatore, India, pp. 1–4 (2018)
Ahvanooey, M.T., Li, Q., Rabbani, M., Rajput, A.R.: An overview on cellphones security: software vulnerabilities, malware, and strikes. Int. J. Adv. Comput. Sci. Appl. 8(10), 30–45 (2017)
Souri, A., Hosseini, R.: A state-of-the-art study of the methods of malware detection utilizing the techniques of data mining. Human Cent. Comput. Inf. Sci. 8
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Manasa, N., Sita Kumari, K., Bhavya Sri, P., Sadhrusya, D. (2023). Artificial Neural Network-Based Malware Detection Model Among Shopping Apps to Increase the App Security. In: Bhateja, V., Yang, XS., Ferreira, M.C., Sengar, S.S., Travieso-Gonzalez, C.M. (eds) Evolution in Computational Intelligence. FICTA 2023. Smart Innovation, Systems and Technologies, vol 370. Springer, Singapore. https://doi.org/10.1007/978-981-99-6702-5_22
Download citation
DOI: https://doi.org/10.1007/978-981-99-6702-5_22
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-99-6701-8
Online ISBN: 978-981-99-6702-5
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)