Abstract
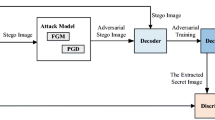
Image steganalysis is the art and science of detecting whether an image contains secrete messages or not, which can prevent malicious usage of steganography. However, steganalysis belongs to passive defense, in the sense that it can only be applied after the stego image is generated. Therefore, there still exists loophole that secrete messages communication could already been accomplished when the stego image is detected. To eliminate malicious steganography from the source, in this paper, an active defensive framework for deep image steganography called ADPI (Active Defense based on Perturbation Injection) is proposed, wherein a defender competes against a steganographer to learn the active defensive strategy. Specifically, on the side of the defender, a generator is adopted to take the original cover image as input, and learn the imperceptible perturbation map. Such perturbation map is added with the original cover image as the enhanced cover image. On the side of the steganographer, a steganographic network is applied to perform message embedding and extraction on the enhanced cover image. The key of ADPI is that the perturbation map is optimized with the goal of reducing the accuracy of the message recovery while maintaining its invisibility. By this means, the active defense can be launched in an effective and imperceptible manner. Experimental results show that the proposed ADPI can be applied to defend against various steganographic methods.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Holub, V., Fridrich, J.J.: Designing steganographic distortion using directional filters. In: Proceedings of the IEEE International Workshop on Information Forensics and Security, pp. 234–239 (2012)
Pevný, T., Filler, T., Bas, P.: Using high-dimensional image models to perform highly undetectable steganography. In: Proceedings of the 12th Information Hiding Workshop, pp. 161–177 (2010)
Li, B., Wang, M., Huang, J., Li, X.: A new cost function for spatial image steganography. In: Proceedings of the IEEE International Conference on Image Processing, pp. 4026–4210 (2014)
Holub, V., Fridrich, J.J.: Digital image steganography using universal distortion. In: Proceedings of the 1st ACM Information Hiding and Multimedia Security Workshop, pp. 59–68 (2013)
Hayes, J., Danezis, G.: Generating steganographic images via adversarial training. In: Proceedings of the 30th Conference on Neural Information Processing Systems, pp. 1954–1963 (2017)
Goodfellow, I.J., et al.: Generative adversarial nets. In: Advances in Neural Information Processing Systems, pp. 2672–2680 (2014)
Zhu, J., Kaplan, R., Johnson, J., Fei-Fei, L.: HiDDeN: hiding data with deep networks. In: Ferrari, V., Hebert, M., Sminchisescu, C., Weiss, Y. (eds.) ECCV 2018. LNCS, vol. 11219, pp. 682–697. Springer, Cham (2018). https://doi.org/10.1007/978-3-030-01267-0_40
Zhang, K.A., Cuesta-Infante, A., Xu, L., Veeramachaneni, K.: Steganogan: high capacity image steganography with GANs. arXiv preprint arXiv:1901.03892 (2019)
Tan, J., Liao, X., Liu, J., Cao, Y., Jiang, H.: Channel attention image steganography with generative adversarial networks. IEEE Trans. Network Sci. Eng. 9(2), 888–903 (2021)
Lu, S.P., Wang, R., Zhong, T., Rosin, P.L.: Large-capacity image steganography based on invertible neural networks. In: Proceedings of the IEEE Conference on Computer Vision and Pattern Recognition, pp. 10816–10825 (2021)
Kodovsky, J., Fridrich, J., Holub, V.: Ensemble classifiers for steganalysis of digital media. IEEE Trans. Inf. Forensics Secur. 7(2), 432–444 (2011)
Fridrich, J., Kodovsky, J.: Rich models for steganalysis of digital images. IEEE Trans. Inf. Forensics Secur. 7(3), 868–882 (2012)
Li, B., Li, Z., Zhou, S., Tan, S., Zhang, X.: New steganalytic features for spatial image steganography based on derivative filters and threshold LBP operator. IEEE Trans. Inf. Forensics Secur. 13(5), 1242–1257 (2017)
Song, X., Liu, F., Yang, C., Luo, X., Zhang, Y.: Steganalysis of adaptive jpeg steganography using 2D gabor filters. In: Proceedings of the 3rd ACM Workshop on Information Hiding and Multimedia Security, pp. 15–23 (2015)
Xu, G., Wu, H.Z., Shi, Y.Q.: Structural design of convolutional neural networks for steganalysis. IEEE Signal Process. Lett. 23(5), 708–712 (2016)
Zhang, R., Zhu, F., Liu, J., Liu, G.: Depth-wise separable convolutions and multi-level pooling for an efficient spatial CNN-based steganalysis. IEEE Trans. Inf. Forensics Secur. 15, 1138–1150 (2019)
You, W., Zhang, H., Zhao, X.: A SIAMESE CNN for image steganalysis. IEEE Trans. Inf. Forensics Secur. 16, 291–306 (2021)
Deng, X., Chen, B., Luo, W., Luo, D.: Fast and effective global covariance pooling network for image steganalysis. In: Proceedings of the ACM Workshop on Information Hiding and Multimedia Security, pp. 230–234 (2019)
Weng, S., Chen, M., Yu, L., Sun, S.: Lightweight and effective deep image steganalysis network. IEEE Signal Process. Lett. 29, 1888–1892 (2022)
Ronneberger, O., Fischer, P., Brox, T.: U-Net: convolutional networks for biomedical image segmentation. In: Navab, N., Hornegger, J., Wells, W.M., Frangi, A.F. (eds.) MICCAI 2015. LNCS, vol. 9351, pp. 234–241. Springer, Cham (2015). https://doi.org/10.1007/978-3-319-24574-4_28
Zhang, C., Benz, P., Karjauv, A., Sun, G., Kweon, I.S.: UDH: universal deep hiding for steganography, watermarking, and light field messaging. In: Proceedings of the 33rd Conference on Neural Information Processing Systems, pp. 10223–10234 (2020)
Almohammad, A., Ghinea, G.: Stego image quality and the reliability of PSNR. In: Proceedings of the 2nd International Conference on Image Processing Theory, Tools and Applications, pp. 215–220. IEEE (2010)
Wang, Z., Bovik, A.C., Sheikh, H.R., Simoncelli, E.P.: Image quality assessment: from error visibility to structural similarity. IEEE Trans. Image Process. 13(4), 600–612 (2004)
Acknowledgements
Weixuan Tang is the corresponding author. This work was supported by NSFC (Grant 62002075), Guangdong Basic and Applied Basic Research Foundation (Grant 2023A1515011428), the Science and Technology Foundation of Guangzhou (Grant 2023A04J1723).
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2024 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Tang, W., Liu, Y. (2024). Active Defense Against Image Steganography. In: Vaidya, J., Gabbouj, M., Li, J. (eds) Artificial Intelligence Security and Privacy. AIS&P 2023. Lecture Notes in Computer Science, vol 14509. Springer, Singapore. https://doi.org/10.1007/978-981-99-9785-5_10
Download citation
DOI: https://doi.org/10.1007/978-981-99-9785-5_10
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-99-9784-8
Online ISBN: 978-981-99-9785-5
eBook Packages: Computer ScienceComputer Science (R0)