Abstract
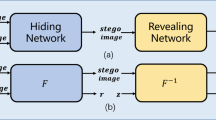
Multi-image hiding is the technique of hiding multiple secret images within one cover image. In most existing methods, it is possible for one receiver to reveal other receivers’ secret images. To improve the privacy and secrecy among different receivers, one possible solution is to introduce the key mechanism, wherein only the receiver with private key has the permission to reveal the corresponding secret image. In this paper, a multiple image hiding method called DEMIHAK (Deep Multiple Image Hiding with Random Key) is proposed, which utilizes deep neural networks to implement a secure key verification. From the side of the sender, each secret image is assigned with a random key, according to which can sample a key map. Then, BindNet is utilized to incorporate a secret image and its key map into a processed secret image, and HideNet is adopted to conceal multiple processed secret images within cover image and generate a stego image. From the side of the receiver, according to a transmitted private key, RevealNet can be applied to reveal the corresponding secret image from the stego image. Experimental results show that DEMIHAK outperforms existing method from the perspective of visual quality, security, and secrecy.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Pevný, T., Filler, T., Bas, P.: Using high-dimensional image models to perform highly undetectable steganography. In: Proceedings of the 12th Information Hiding Workshop, pp. 161–177 (2010)
Li, B., Wang, M., Huang, J., Li, X.: A new cost function for spatial image steganography. In: Proceedings of the IEEE International Conference on Image Processing, pp. 4026–4210 (2014)
Sedighi, V., Cogranne, R., Fridrich, J.: Content-adaptive steganography by minimizing statistical detectability. IEEE Trans. Inf. Forensics Secur. 11(2), 221–234 (2016)
Guo, L., Ni, J., Su, W., Tang, C., Shi, Y.Q.: Using statistical image model for jpeg steganography: uniform embedding revisited. IEEE Trans. Inf. Forensics Secur. 10(12), 2669–2680 (2015)
Yang, J., Ruan, D., Huang, J., Kang, X., Shi, Y.Q.: An embedding cost learning framework using GAN. IEEE Trans. Inf. Forensics Secur. 15, 839–851 (2019)
Tang, W., Li, B., Li, W., Wang, Y., Huang, J.: Reinforcement learning of non-additive joint steganographic embedding costs with attention mechanism. Sci. China Inf. Sci. 66(3), 132305:1-132305:14 (2023)
Zhu, J., Kaplan, R., Johnson, J., Fei-Fei, L.: HiDDeN: hiding data with deep networks. In: Ferrari, V., Hebert, M., Sminchisescu, C., Weiss, Y. (eds.) ECCV 2018. LNCS, vol. 11219, pp. 682–697. Springer, Cham (2018). https://doi.org/10.1007/978-3-030-01267-0_40
Zhang, K.A., Cuesta-Infante, A., Veeramachaneni, K.: Steganogan: High capacity image steganography with GANs. arXiv preprint arXiv:1901.03892 (2019)
Baluja, S.: Hiding images in plain sight: deep steganography. In: Proceedings of the 31th International Conference on Neural Information Processing Systems, pp. 2069–2079 (2017)
ur Rehman, A., Rahim, R., Nadeem, S., ul Hussain, S.: End-to-end trained CNN encoder-decoder networks for image steganography. In: Leal-Taixé, L., Roth, S. (eds.) ECCV 2018. LNCS, vol. 11132, pp. 723–729. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-11018-5_64
Yu, C.: Attention based data hiding with generative adversarial networks. In: Proceedings the AAAI Conference on Artificial Intelligence, pp. 1120–1128 (2020)
Zhang, C., Benz, P., Karjauv, A., Sun, G., Kweon, I.S.: UDH: Universal deep hiding for steganography, watermarking, and light field messaging. In: Proceedings of the 33th Conference on Neural Information Processing Systems, pp. 10223–10234 (2020)
Guan, Z., et al.: Deepmih: deep invertible network for multiple image hiding. IEEE Trans. Pattern Anal. Mach. Intell. 45(1), 372–390 (2023)
Lu, S.P., Wang, R., Zhong, T., Rosin, P.L.: Large-capacity image steganography based on invertible neural networks. In: Proceedings of the IEEE Conference on Computer Vision and Pattern Recognition, pp. 10816–10825 (2021)
Wang, Z., Feng, G., Ren, Y., Zhang, X.: Multichannel steganography in digital images for multiple receivers. IEEE Multimedia 28(1), 65–73 (2021)
Kweon, H., Park, J., Woo, S., Cho, D.: Deep multi-image steganography with private keys. Electronics 10(16), 1906:1–1906:10 (2021)
Boehm, B.: Stegexpose-a tool for detecting LSB steganography. arXiv preprint arXiv:1410.6656 (2014)
Acknowledgements
This work was supported by NSFC (Grant 62002075), Guangdong Basic and Applied Basic Research Foundation (Grant 2023A1515011428), the Science and Technology Foundation of Guangzhou (Grant 2023A04J1723).
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2024 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Zhang, W., Tang, W., Rao, Y., Li, B., Huang, J. (2024). Deep Multi-image Hiding with Random Key. In: Vaidya, J., Gabbouj, M., Li, J. (eds) Artificial Intelligence Security and Privacy. AIS&P 2023. Lecture Notes in Computer Science, vol 14509. Springer, Singapore. https://doi.org/10.1007/978-981-99-9785-5_3
Download citation
DOI: https://doi.org/10.1007/978-981-99-9785-5_3
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-99-9784-8
Online ISBN: 978-981-99-9785-5
eBook Packages: Computer ScienceComputer Science (R0)