Abstract
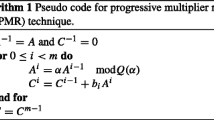
This paper presents bit-level cellular arrays implementing Blakley's algorithm for multiplication of twon-bit integers modulo anothern-bit integer. The semi-systolic version uses 3n(n+3) single-bit carry save adders and 2n copies of 3-bit carry look-ahead logic, and computes a pair of binary numbers (C, S) in 3n clock cycles such thatC+Sε[0, 2N). The carry look-ahead logic is used to estimate the sign of the partial product, which is needed during the reduction process. The final result in the correct range [0,N) can easily be obtained by computingC+S andC+S−N, and selecting the latter if it is positive; otherwise, the former is selected. We construct a localized process dependence graph of this algorithm, and introduce a systolic array containing 3nw simple adder cells. The latency of the systolic array is 6n+w−2, wherew=⌈n/2⌉. The systolic version does not require broadcast and can be used to efficiently compute several modular multiplications in a pipelined fashion, producing a result in every clock cycle.
Similar content being viewed by others
References
R.L. Rivest, A. Shamir, and L. Adleman, “A method for obtaining digital signatures and public-key cryptosystems,”Communications of the ACM, 21, 1978, pp. 120–126.
A.G. Konheim,Cryptography, A Primer. New York: John Wiley, 1981.
N. Koblitz., “A Course in Number Theory and Cryptography, New York: Springer-Verlag, 1987.
M.A. Soderstrand, W.K. Jenkins, G.A. Jullien, and F.J. Taylor, (ed.),Residue Arithmetic: Modern Applications in Digital Signal Processing, New York: IEEE Press, 1986.
K. Hwang,Computer Arithmetic, Principles, Architecture, and Design. New York: John Wiley, 1979.
E.E. Swartzlander, (ed.),Computer Arithmetic, vol. I and II. Los Alamitos: IEEE Computer Society Press, 1990.
D. Simmons and S.E. Tavares “An NMOS implementation of a large number modulo multiplier for data encryption systems.” InProceedings of the 1983 IEEE Custom Integrated Circuits Conference, Rochester, New York: IEEE Press, 1983, pp. 262–266.
G.R. Blakley, “A computer algorithm for the product AB modulo M,”IEEE Transactions on Computers, 32, 1983, pp. 497–500.
K.R. Sloan, Jr. “Comments on: ‘A computer algorithm for the product AB modulo M.’”IEEE Transactions on Computers, 34, 1985, pp. 290–292.
P.W. Baker, “Fast computation ofA*B moduloN,”Electronics Letters, 23, 1987, pp. 794–795.
Ç.K. Koç and C.Y. Hung, “Multi-operand modulo addition using carry save adders.”Electronics Letters, 26, 1990, pp. 361–363.
Ç.K. Koç and C.Y. Hung, “Carry save adders for computing the productAB moduloN.”Electronics Letters, 26, 1990, pp. 899–900.
S.Y. Kung, “VLSI Array Processors.” Englewood Cliffs, NJ: Prentice-Hall, 1988.
D.E. Knuth. “The Art of Computer Programming: Seminumerical Algorithms,” vol. 2. Reading, MA: Addison-Wesley, (2nd ed.), 1981.
E.F. Brickell, “A survey of hardware implementations of RSA.” In (G. Brassard, ed.)Advances in Cryptology-Crypto 89, Proceedings, Lecture Notes in Computer Science, No. 435, New York: Springer-Verlag, 1989, pp. 368–370.
C.N. Zhang, H.L. Martin, and D.Y.Y. Yun, “Parallel algorithms and systolic arrays designs for RSA cryptosystem.” In (K. Bromley, S.Y. Kung, and E. Swartzlander, ed.,Proceedings of the International Conference on Systolic Arrays, San Diego, California, Los Alamitos: IEEE Computer Society Press, 1988, pp. 341–350.
E.F. Brickell, “A fast modular multiplication algorithm with application to two key cryptography.” In (D. Chaum, R.L. Rivest, and A.T. Sherman, ed.)Advances in Cryptology, Proceedings of Crypto 82 New York: Plenum Press, 1982, pp. 51–60.
C.H.N. Forster, S.S. Dlay, and R.N. Gorgui-Naguib, “Carry delayed save adders for computing the productAB moduloN in log2 N steps.”Electronics Letters, 26, 1990, pp. 1544–1545.
Author information
Authors and Affiliations
Rights and permissions
About this article
Cite this article
Koç, Ç.K., Hung, C.Y. Bit-level systolic arrays for modular multiplication. J VLSI Sign Process Syst Sign Image Video Technol 3, 215–223 (1991). https://doi.org/10.1007/BF00925832
Received:
Revised:
Published:
Issue Date:
DOI: https://doi.org/10.1007/BF00925832