Abstract
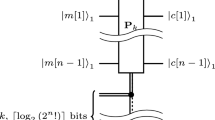
The use of cryptography for data protection has received a great deal of attention in recent years. This paper presents computationally efficient algorithms for the implementation of a one-time pad scheme. The algorithms to encipher and decipher text were implemented on aPDP-11 computer using the programming languageC. To study the behavior of the keys used to encipher and decipher text, we used the chi-square method, and the test results of two runs are presented with some statistical analysis.
Similar content being viewed by others
References
A. G. Akritas, An implementation of Vincent's theorem,Numerishche Mathematik 36:53–62 (1980).
A. G. Akritas, The fastest exact algorithms for the isolation of the real roots of a polynomial equation,Computing 24:299–313 (1980).
A. G. Akritas, Exact algorithm for the implementation of Cauchy's rule,Int. J. Comp. Math. 9:323–333 (1981).
A. G. Akritas, Application of Vincent's theorem in cryptography or one-time pads made practical,Cryptologia 6(4):312–318 (1982).
A. G. Akritas and S. D. Danielopoulos, On the complexity of algorithms for the translation of polynomials,Computing 24:51–60 (1980).
A. G. Akritas and S. D. Danielopoulos, An unknown theorem for the isolation of the roots of polynomials,Ganita Bharati 2(3/4):41–49 (1980).
W. F. Ehrsam, S. M. Matyas, C. H. Meyer, and W. L. Tuchman, A cryptographic key management scheme for implementing the data encryption standard,IBM Syst. J. 17(2):106–125 (1978).
W. Diffie and M. E. Hellman, A critique of the proposed date encryption standard,Comm. ACM (March 1976), pp. 164–165.
E. Gudes, The design of a cryptography based secure file system,IEEE Trans. Software Eng. SE-6(5):411–420 (September 1980).
E. Gudes, F. A. Stahl, and H. E. Koth, Applications of cryptographic transformations to data base security, inProceedings of National Computer Conference (1976).
B. W. Kernighan and D. M. Ritchie,The C Programming Language, Prentice-Hall, Englewood Cliffs, New Jersey (1978).
D. E. Knuth,The Art of Computer Programming, Addison Wesley, Reading, Mass., Vol. 2, pp. 1–70 (1969).
S. Lang and H. Trotter, Continued franctions for some algebraic numbers,J. Reine Angew. Math. 255:122–134 (1972).
R. C. Merkle, Secure communications over insecure channels,Comm. ACM 1978:194–299.
K. H. Ng, Polynomial real root approximation using continued fractions, M.S. Research Report, Department of Computer Science, University of Kansas, Lawrence, Kansas (1980).
S. M. Pizer,Numerical Computing and Mathematical Analysis, Science Research Associates, Chicago, pp. 187–217 (1975).
G. B. Purdy, A high security log-in procedure,CACM 17 (August 1974).
A. Rampuria, A secure method for cryptography, M.S. Research Report, Department of Computer Science, University of Kansas, Lawrence, Kansas (1982).
J. V. Uspensky,Theory of Equations, McGraw-Hill, New York (1948).
A. J. H. Vincent, Sur la résultion des équation numeriques,J. Math. Pures Appl. 1:341–372 (1836).
Author information
Authors and Affiliations
Additional information
This author was partially supported by the General Research Fund (No. 3230-20-0038) of the University of Kansas.
Rights and permissions
About this article
Cite this article
Akritas, A.G., Iyengar, S.S. & Rampuria, A.A. Computationally efficient algorithms for a one-time pad scheme. International Journal of Computer and Information Sciences 12, 285–316 (1983). https://doi.org/10.1007/BF00991623
Received:
Revised:
Issue Date:
DOI: https://doi.org/10.1007/BF00991623