Abstract
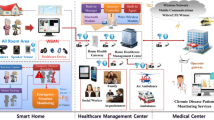
Industrial Internet of Things (I-IoT) has become an emerging driver to operate industrial systems and a primary empowerer to future industries. With the advanced technologies such as artificial intelligence (AI) and machine learning widely used in IoT, the Industrial IoT is also witnessing changes driven by new technologies. Generally, AI technologies require centralized data collection and processing to learn from the data to obtain viable models for application. In industrial IoT, data security and privacy problems associated with reliable and interconnected end devices are being faced and reliable solutions are urgently needed. A trusted execution environment in IoT devices is gradually becoming a feasible approach, and a distributed solution is a natural choice for artificial intelligence technologies in I-IoT. Moreover, Federated Learning as a distributed machine learning paradigm with privacy-preserving properties can be used in I-IoT. This paper introduces a feasible secure data circulation and sharing scheme for I-IoT devices in a trusted implementation platform by employing federated learning. The suggested framework has proved to be efficient, reliable, and accurate.






Similar content being viewed by others
Data availability
The data implemented in the research can be presented when requested.
References
Yunlong Lu, Huang X, Zhang Ke, Maharjan S, Zhang Y (2020) Communication-efficient federated learning for digital twin edge networks in industrial IoT. IEEE Trans Industr Inf 17(8):5709–5718
Sadeghi AR, Wachsmann C, Waidner M (2015) Security and privacy challenges in the industrial internet of things. In: 2015 52nd ACM/EDAC/IEEE Design Automation Conference (DAC). pp 1–6
Sabt M, Achemlal M, Bouabdallah AM (2015) Trusted execution environment: what it is, and what it is not. In: 2015 IEEE Trustcom/BigDataSE/ISPA. 1: 57–64
Ayoade G, Karande V, Khan L, Hamlen K (2018) Decentralized IoT data management using blockchain and trusted execution environment. In: 2018 IEEE international conference on information reuse and integration (IRI). pp 15–22
McMahan B, Moore E, Ramage D, Hampson S, y Arcas BA (2017) Communication-efficient learning of deep networks from decentralized data. In: Artificial intelligence and statistics. pp 1273–1282
Nguyen DC, Ding M, Pathirana PN et al (2021) Federated learning for the industrial internet of things in future industries. arXiv preprint arXiv:2105.14659
Yang Q, Liu Y, Chen T, Tong Y (2019) Federated machine learning: concept and applications. ACM Trans Intell Syst Technol 10(2):1–19
Mothukuri V, Parizi RM, Pouriyeh S et al (2021) A survey on security and privacy of federated learning. Future Gener Comput Syst 115:619–640
Li T, Sahu AK, Talwalkar A, Smith V (2020) Federated learning: challenges, methods, and future directions. IEEE Signal Process Mag 37(3):50–60
Yang T, Andrew G, Eichner H, et al (2018) Applied federated learning: improving google keyboard query suggestions. arXiv preprint arXiv:1812.02903
Jie Xu, Glicksberg BS, Chang Su et al (2021) Federated learning for healthcare informatics. J Healthc Inform Res 5(1):1–19
Jiang JC, Kantarci B, Oktug S, Soyata T (2020) Federated learning in smart city sensing: challenges and opportunities. Sensors 20(21):6230
Sheller MJ, Brandon Edwards G, Reina A et al (2020) Federated learning in medicine: facilitating multi-institutional collaborations without sharing patient data. Sci rep 10(1):1–12
Niknam S, Dhillon HS, Reed JH (2020) Federated learning for wireless communications: motivation, opportunities, and challenges. IEEE Commun Mag 58(6):46–51
Pham Q-V, Fang Fang Vu, Ha N et al (2020) A survey of multi-access edge computing in 5g and beyond: fundamentals, technology integration, and state-of-the-art. IEEE Access 8:116974–117017
Yunlong Lu, Huang X, Dai Y, Maharjan S, Zhang Y (2019) Blockchain and federated learning for privacy-preserved data sharing in industrial IoT. IEEE Trans Ind Inf 16(6):4177–4186
Zhang W, Qinghua Lu, Qiuyu Yu et al (2020) Blockchain-based federated learning for device failure detection in industrial IoT. IEEE Internet Things J 8(7):5926–5937
Liu Yi, Garg S, Nie J et al (2020) Deep anomaly detection for time-series data in industrial IoT: a communication-efficient on-device federated learning approach. IEEE Internet Things J 8(8):6348–6358
Pham QV, Dev K, Reddy PK, Maddikunta, et al (2021) Fusion of federated learning and industrial internet of things: a survey. arXiv preprint arXiv:2101.00798
Anciaux N, Bonnet P, Bouganim L, et al (2013) Trusted cells: a sea change for personnal data services. In: Proceedings of the 6th biennal conference on innovative database research (CIDR 2013). Pp 4
Kinney SL (2006) Trusted platform module basics: using TPM in embedded systems. Elsevier
Asokan N, Ekberg JE, Kostiainen K et al (2014) Mobile trusted computing. Proc IEEE 102(8):1189–1206
Arfaoui G, Gharout S, Traoré J (2014) Trusted execution environments: a look under the hood. In: 2014 2nd IEEE international conference on mobile cloud computing, services, and Engineering. pp 259–266
Anati I, Gueron S, Johnson S, Scarlata V (2013) Innovative technology for CPU-based attestation and sealing. In: Proceedings of the 2nd international workshop on hardware and architectural support for security and privacy. 13: 7
Ruan X (2014) Platform embedded security technology revealed. Springer Nature
Part Guide (2011) Intel® 64 and ia-32 architectures software developer’s manual. Volume 3B: system programming guide, Part. 2(11)
Kaplan D, Powell J, Woller T (2016) AMD memory encryption. White paper
Lai R (2013) Amd security and server innovation. UEFI PlugFest-March 2013:18–22
Architecture Arm (2009) Security technology-building a secure system using trust-zone technology. ARM technical white paper
Wilensky U, Rand W (2015) An introduction to agent-based modeling: modeling natural, social, and engineered complex systems with NetLogo. MIT Press
Liang U, Zhang M, Leung VCM (2020) A reliable trust computing mechanism based on multisource feedback and fog computing in social sensor cloud. IEEE Internet Things J 7(6):5481–5490
Demertzis K, Iliadis L, Pimenidis E et al (2022) Variational restricted Boltzmann machines to automated anomaly detection. Neural Comput Appl 34:15207–15220. https://doi.org/10.1007/s00521-022-07060-4
Mo F, Haddadi H, Katevas K et al (2021) PPFL: privacy-preserving federated learning with trusted execution environments. In: Proceedings of the 19th annual international conference on mobile systems, applications, and services. pp 94–108
Acknowledgements
This research was patronized by the General Program of Science and Technology Development Project of the Beijing Municipal Education Commission of China (Nos. KM202110037002).
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that they have no conflict of interest.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Zheng, W., Cao, Y. & Tan, H. Secure sharing of industrial IoT data based on distributed trust management and trusted execution environments: a federated learning approach. Neural Comput & Applic 35, 21499–21509 (2023). https://doi.org/10.1007/s00521-023-08375-6
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00521-023-08375-6