Abstract
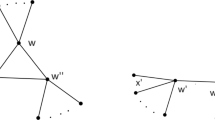
An addition chain for a natural number n is a sequence \({1=a_0 < a_1 < \cdots < a_r=n}\) of numbers such that for each 0 < i ≤ r, a i = a j + a k for some 0 ≤ k ≤ j < i. The minimal length of an addition chain for n is denoted by ℓ(n). If j = i − 1, then step i is called a star step. We show that there is a minimal length addition chain for n such that the last four steps are stars. Then we conjecture that there is a minimal length addition chain for n such that the last \({\lfloor\frac{\ell(n)}{2}\rfloor}\)-steps are stars. We verify that the conjecture is true for all numbers up to 218. An application of the result and the conjecture to generate a minimal length addition chain reduce the average CPU time by 23–29% and 38–58% respectively, and memory storage by 16–18% and 26–45% respectively for m-bit numbers with 14 ≤ m ≤ 22.
Similar content being viewed by others
References
Bahig HM (2006) Improved generation of minimal addition chains. Computing 78: 161–172
Bahig HM, Nakamula K (2002) Some properties of nonstar steps in addition chains and new cases where the Scholz conjecture is true. J Algorithms 42: 304–316
Bleichenbacher D, Flammenkamp A An efficient algorithm for computing shortest addition chains. http://www.homes.uni-bielefeld.de/achim/addition_chain.html (unpublished)
Bos J, Coster M (1989) Addition chain heuristics. In: Brassard G (ed) Advances in cryptology—CRYPTO ’89. Lecture notes in computer science, vol 435, pp 400–407
Brickell EF, Gordon DM, McCurley KS, Wilson D (1993) Fast exponentiation with precomputation. In: Rueppel RA (ed) Advances in cryptology—EUROCRYPT ’92. Lecture notes in computer science, vol 658, pp 200–207
Chin YH, Tsai YH (1985) Algorithms for finding the shortest addition chain. In: Proceedings of national computer symposium, Kaoshiung, Taiwan, December 20–22, 1985, pp 1398–1414
Diffie W, Hellman ME (1976) New directions in cryptography. IEEE Trans Inf Theory 22: 644–654
Downey P, Leong B, Sethi R (1981) Computing sequences with addition chains. SIAM J Comput 10(3): 638–646
ElGamal T (1985) A public-key cryptosystem and a signature scheme based on discrete logarithms. IEEE Trans Inf Theory 31: 469–472
Gordon DM (1998) A survey of fast exponentiation methods. J Algorithms 122: 129–146
Knuth DE (1997) The art of computer programming: seminumerical algorithms, vol 2, 3rd edn. Addison-Wesley, Reading, pp 461–485
Lim CH, Lee PJ (1994) More flexible exponentiation with precomputation. In: Desmedt YG (ed) Advances in cryptology—CRYPTO ’94. Lecture notes in computer science, vol 839, pp 95–107
National Institute of Standards and Technology (2000) Digital signature standard (DSS). Federal Information Processing Standards Publication, FIPS PUB 186-2, Jan 27, 2000
Rivest R, Shamir A, Adleman L (1978) A method for obtaining digital signatures and public-key cryptosystems. Commun ACM 21: 120–126
de Rooij P (1995) Efficient exponentiation using precomputation and vector addition chains. In: Helleseth T (ed) Advances in cryptology—EUROCRYPT ’94. Lecture notes in computer science, vol 950, pp 389–399
Schönhage A (1975) A lower bound for the length of addition chains. Theor Comput Sci 1: 1–12
Subbarao M (1989) Addition chains—some results and problems. In: Mollin RA (ed) Number theory and applications. Kluwer, Dordrecht, pp 555–574
Thurber EG (1973) The Scholz-Brauer problem on addition chains. Pac J Math 49: 229–242
Thurber EG (1993) Addition chains—an erratic sequence. Discrete Math 122: 287–305
Thurber EG (1999) Efficient generation of minimal length addition chains. SIAM J Comput 28: 1247–1263
Author information
Authors and Affiliations
Corresponding author
Additional information
Communicated by C.H. Cap.
Rights and permissions
About this article
Cite this article
Bahig, H.M. Star reduction among minimal length addition chains. Computing 91, 335–352 (2011). https://doi.org/10.1007/s00607-010-0122-z
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00607-010-0122-z