Abstract
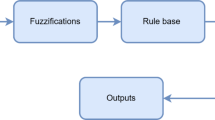
This paper proposes to use the novel fuzzy logic controller (FLC), which is a dynamic buffer size tuning technique, to support more dependable location-aware information retrieval in a pervasive environment. Within a smart space of a mobile/pervasive environment a user may request service from the dedicated surrogate via a portable small-form-factor (SFF) device (e.g. PDA). In effect, the SFF is the client and the surrogate is the server, which may serve many clients at the same time. The one-surrogate-to-many-SFF relationship or asymmetric rendezvous easily makes the surrogate buffer overflow in the peak demand seasons. The request traffic to the surrogate is tied in with the transient traveler mass traffic through the smart space, for example, in an airport. The transit travelers may switch on their mobile SFF at will to demand service from the local surrogate. If the surrogate buffer overflows, the users do not benefit from the cyber foraging provided by the pervasive computing infrastructure in the background. The FLC adaptively tunes the surrogate buffer size so that it always covers the queue length by the given Δ safety margin. As a result the SFF-surrogate asymmetric rendezvous becomes dependable because the chance of buffer overflow is eliminated. The dependability leads to shorter information retrieval roundtrip time (RTT) and happier users.















Similar content being viewed by others
References
Garlan D, Siewiorek DP, Smailagic A, Steenkiste P (2002) Project aura: toward distraction-free pervasive computing. IEEE Pervasive Comput 1(2):22–31
Weiser M (1991) The computer for the twenty-first century, Scientific American, pp 94–104
Hightower J, Borriello G (2001) Location systems for ubiquitous computing. IEEE Comput 34(8):57–66
Cool C, Spink A (2002) Issues of context in information retrieval (IR): an introduction to the special issue. Inf Process Manage 38(5):605–611
Brown PJ, Jones GJF (2001) Context-aware retrieval: exploring a new environment for information retrieval and information filtering. Pers Ubiquit Comput 5(4):253–263
Brown PJ, Jones GJF (2002) Information access and retrieval: exploiting contextual change in context-aware retrieval. In: Proceedings of the 2002 ACM symposium on applied computing, Madrid, pp 650 – 656
Satyanarayanan M (2001) Pervasive computing: vision and challenges. IEEE Pers Commun 8(4):10–17
Patterson CA, Muntz RR, Pancake CM (2003) Challenges in location-aware computing. IEEE Pervasive Comput 2(2):80 – 89
Lewis T (1996) The next 10,0002 years: part 1. IEEE Comput 29(4):64–70
Malla A, El-Kadi M, Olariu S, Todorova P (2003) A fair resource allocation protocol for multimedia wireless networks. IEEE Trans Parallel Distrib Syst 14(1):63–71
Jamjoom H, Pillai P, Shin KG (2004) Resynchronization and controllability of bursty service requests. IEEE/ACM Trans Netw 14(4):582–594
Medina A, Matta I, Byers J (2000) On the origin of power laws in internet topologies. ACM SIGCOMM 30(2):18–28
Molnar S, Dang TD, Vidacs A (1999) Heavy-tailedness, long-range dependence and self-similarity in data traffic. In: Proceedings of 7th international conference on telecommunication systems, Modelling and analysis, Nashville, pp 18–21
Lin WWK, Wong AKY (2002) A fuzzy controller for adaptive buffer control leading to better channel reliability and system performance for object-based internet applications. In: Proceedings of the PDPTA2002, Las Vegas, pp 345–350
Wong AKY, Dillon TS, Lin WWK, Ip MTW (2001) M 2 RT: a tool developed for predicting the mean message response time for internet channels. J Comput Netw 36:557–577
Wong AKY, Wong JHC (2001) A convergence algorithm for enhancing the performance of distributed applications running on sizeable networks, the international journal of computer systems. Sci Eng 16(4):229–236
Wong AKY, Ip MTW, Dillon TS (2002) M3RT: An internet end-to-end performance measurement approach for real-time applications with mobile agents. In: Proceedings of the ISPAN’2002, pp 119–124
Avizienis A, Laprie JC, Randell B, Landwehr C (2004) Basic concepts and taxonomy of dependable and secure computing. IEEE Trans Depend Secure Comput 1(1):11–33
[VTune] Intel’s VTune performance analyzer, http://www.intel.com/support/performancetools/vtune/v5
Karagiannis T, Faloutsos M, Molle M (2003) A user-friendly self-similarity analysis tool. ACM SIGCOMM Comput Commun Rev 33(3):81–93 (http://www.cs.ucr.edu/∼tkarag/Selfis/Selfis.html)
The wireless LAN traces, Department of Computing, Hong Kong Polytechnic University, http://www4.comp.polyu.edu.hk/∼cswklin/research/traces/wireless/
Tang D, Baker M Analysis of a local-area wireless network. In: Proceedings of the 6th annual international conference on mobile computing and networking, Boston, pp 1–10 http://mosquitonet.stanford.edu/software.html
Acknowledgments
The authors thank the Hong Kong Polytechnic University for the grants, A-PF75 and H-ZJ91.
Author information
Authors and Affiliations
Corresponding author
Appendix: The essence of the convergence algorithm
Appendix: The essence of the convergence algorithm
The convergence algorithm (CA) is an internet end-to-end performance measurement (IEPM) technique. It estimates the mean service roundtrip time (RTT) of a logical channel quickly and accurately. The Java-based CA prototype, M 2 RT, was verified and validated as a macro tool. In its macro form the tool must be installed at the two nodes that represent the ends of the logical channel. Micro IEPM tools differ by operating as a logical entity to be invoked anytime and anywhere for service by message passing. The positive mean message response time (M 2 RT) experience led to the development of the Java-based micro CA (MCA) prototype: micro mean message response time (M 3RT) [17]. The CA treats a traffic pattern simply as a waveform, and its speed and accuracy are independent of the traffic pattern because it is based on the Central Limit Theorem. The CA operation is summarized by (2) and (3), where M i is the estimated mean of the distribution for the time window in which the F (flush limit) number of data samples is collected; F = 14 yields the fastest estimation convergence. The other parameters are: (a) M i − 1 is the feedback of the last estimated mean to the current estimation cycle, (b) m i j is the jth sample in the jth M i estimation cycle, j = 1,2,3,(F − 1), and (c) M 0 is the first data sample when the CA has started. Figure 16 is an example in which M i always settles to the average channel RTT of 480 ms in the steady state.
Rights and permissions
About this article
Cite this article
Lin, W.W.K., Dillon, T.S. & Wong, A.K.Y. Applying FLC-based dynamic buffer size tuning to shorten the information retrieval round trip time in mobile location-aware environments. Pers Ubiquit Comput 12, 45–55 (2008). https://doi.org/10.1007/s00779-006-0125-0
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00779-006-0125-0