Abstract
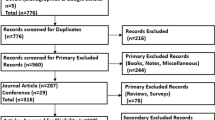
With the recent increase in internet usage, the number of important, sensitive, confidential individual and corporate data passing through internet has increasingly grown. With gaps in the security systems, attackers have attempted to intrude the network, thereby gaining access to essential and confidential information, which may cause harm to the operation of the systems, and also affect the confidentiality of the data. To counter these possible attacks, intrusion detection systems (IDSs), which is an essential branch of cybersecurity, were employed to monitor and analyze network traffic thereby detects and reports malicious activities. A large number of review papers have covered different approaches for intrusion detection in networks, most of which follow a non-systematic approach, merely made a comparison of the existing techniques without reflecting an in-depth analytical synthesis of the methodologies and performances of the approaches to give a complete understanding of the state of IDS. Nonetheless, many of these reviews investigated more about the anomaly-based IDS with more emphasis on deep-learning models, while signature, hybrid-based (signature + anomaly-based) have received minimal focus. Hence, by adhering to the principles of Preferred Reporting Items for Systematic Reviews and Meta-Analyses (PRISMA), this work reviewed existing contributions on anomaly-, signature-, and hybrid-based approaches to provide a comprehensive overview of network IDS's state of the art. The articles were retrieved from seven databases (ScienceDirect, SpringerNature, IEEE, MDPI, Hindawi, PeerJ, and Taylor & Francis) which cut across various reputable journals and conference Proceedings. Among the 776 pieces of the literature identified, 71 were selected for analysis and synthesis to answer the research questions. Based on the research findings, we identified unexplored study areas and unresolved research challenges. In order to create a better IDS model, we conclude by presenting promising, high-impact future research areas.




Similar content being viewed by others
Data availability
Not Applicable.
References
Patel, A., Alhussian, H., Pedersen, J.M., Bounabat, B., Júnior, J.C., Katsikas, S.: A nifty collaborative intrusion detection and prevention architecture for smart grid ecosystems. Comput. Secur. 64, 92–109 (2017). https://doi.org/10.1016/j.cose.2016.07.002
Bridges, R.A., Glass-Vanderlan, T.R., Iannacone, M.D., Vincent, M.S., Chen, Q.: A survey of intrusion detection systems leveraging host data. ACM Comput. Surv. 52(6), 1–35 (2020). https://doi.org/10.1145/3344382
Aldweesh, A., Derhab, A., Emam, A.Z.: Deep learning approaches for anomaly-based intrusion detection systems: a survey, taxonomy, and open issues. Knowl. Based Syst. 189, 105124 (2020). https://doi.org/10.1016/j.knosys.2019.105124
Masdari, M., Khezri, H.: A survey and taxonomy of the fuzzy signature-based intrusion detection systems. Appl. Soft Comput. 92, 106301 (2020). https://doi.org/10.1016/j.asoc.2020.106301
Masdari, M., Khezri, H.: Towards fuzzy anomaly detection-based security: a comprehensive review. Fuzzy Optim. Decis. Mak. 20(1), 1–49 (2021). https://doi.org/10.1007/s10700-020-09332-x
Ashfaq, R.A.R., Wang, X.-Z., Huang, J.Z., Abbas, H., He, Y.-L.: Fuzziness based semi-supervised learning approach for intrusion detection system. Inf. Sci. 378, 484–497 (2017). https://doi.org/10.1016/j.ins.2016.04.019
Gu, J., Wang, L., Wang, H., Wang, S.: A novel approach to intrusion detection using SVM ensemble with feature augmentation. Comput. Secur. 86, 53–62 (2019). https://doi.org/10.1016/j.cose.2019.05.022
Nazir, A., Khan, R.A.: A novel combinatorial optimization based feature selection method for network intrusion detection. Comput. Secur. 102, 102164 (2021). https://doi.org/10.1016/j.cose.2020.102164
Sohi, S.M., Seifert, J.-P., Ganji, F.: RNNIDS: enhancing network intrusion detection systems through deep learning. Comput. Secur. 102, 102151 (2021). https://doi.org/10.1016/j.cose.2020.102151
Zhang, J., Ling, Y., Fu, X., Yang, X., Xiong, G., Zhang, R.: Model of the intrusion detection system based on the integration of spatial-temporal features. Comput. Secur. 89, 101681 (2020). https://doi.org/10.1016/j.cose.2019.101681
Liu, J., Gao, Y., Hu, F.: A fast network intrusion detection system using adaptive synthetic oversampling and LightGBM. Comput. Secur. 106, 102289 (2021). https://doi.org/10.1016/j.cose.2021.102289
Mebawondu, J.O., Alowolodu, O.D., Mebawondu, J.O., Adetunmbi, A.O.: Network intrusion detection system using supervised learning paradigm. Sci. Afr. 9, e00497 (2020). https://doi.org/10.1016/j.sciaf.2020.e00497
Wang, Z., Liu, Y., He, D., Chan, S.: Intrusion detection methods based on integrated deep learning model. Comput. Secur. 103, 102177 (2021). https://doi.org/10.1016/j.cose.2021.102177
Selvakumar, B., Muneeswaran, K.: Firefly algorithm based feature selection for network intrusion detection. Comput. Secur. 81, 148–155 (2019). https://doi.org/10.1016/j.cose.2018.11.005
Ashiku, L., Dagli, C.: Network intrusion detection system using deep learning. Procedia Comput. Sci. 185, 239–247 (2021). https://doi.org/10.1016/j.procs.2021.05.025
Gu, J., Lu, S.: An effective intrusion detection approach using SVM with naïve Bayes feature embedding. Comput. Secur. 103, 102158 (2021). https://doi.org/10.1016/j.cose.2020.102158
Bhati, B.S., Rai, C.S., Balamurugan, B., Al-Turjman, F.: An intrusion detection scheme based on the ensemble of discriminant classifiers. Comput. Electr. Eng. 86, 106742 (2020). https://doi.org/10.1016/j.compeleceng.2020.106742
Ozkan-Okay, M., Samet, R., Aslan, Ö., Gupta, D.: A comprehensive systematic literature review on intrusion detection systems. IEEE Access 9, 157727–157760 (2021). https://doi.org/10.1109/ACCESS.2021.3129336
Maseno, E.M., Wang, Z., Xing, H.: A systematic review on hybrid intrusion detection system. Secur. Commun. Netw. 2022, 9663052 (2022). https://doi.org/10.1155/2022/9663052
Luo, G., Chen, Z., Mohammed, B.O.: A systematic literature review of intrusion detection systems in the cloud-based IoT environments. Concurr. Comput. Pract. Exp. 34(10), e6822 (2022). https://doi.org/10.1002/cpe.6822
Ayyagari, M.R., Kesswani, N., Kumar, M., Kumar, K.: Intrusion detection techniques in network environment: a systematic review. Wirel. Netw. 27(2), 1269–1285 (2021). https://doi.org/10.1007/s11276-020-02529-3
Alsoufi, M.A., et al.: Anomaly-based intrusion detection systems in IoT Using deep learning: a systematic literature review. Appl. Sci. (2021). https://doi.org/10.3390/app11188383
Yang, Z., et al.: A systematic literature review of methods and datasets for anomaly-based network intrusion detection. Comput. Secur. 116, 102675 (2022). https://doi.org/10.1016/j.cose.2022.102675
Liberati, A., et al.: The PRISMA statement for reporting systematic reviews and meta-analyses of studies that evaluate healthcare interventions: explanation and elaboration. BMJ 339, b2700 (2009). https://doi.org/10.1136/bmj.b2700
Kitchenham, B., Brereton, P.: A systematic review of systematic review process research in software engineering. Inf. Softw. Technol. 55(12), 2049–2075 (2013). https://doi.org/10.1016/j.infsof.2013.07.010
Kitchenham B.A., Stuart C.: Guidelines for performing systematic literature reviews in software engineering. In: EBSE Technical Report, Keele University and Durham University Joint Report, Report EBSE 2007-001 (2007). https://www.elsevier.com/__data/promis_misc/525444systematicreviewsguide.pdf
Gupta, N., Jindal, V., Bedi, P.: LIO-IDS: Handling class imbalance using LSTM and improved one-vs-one technique in intrusion detection system. Comput. Netw. 192, 108076 (2021). https://doi.org/10.1016/j.comnet.2021.108076
Nguyen, M.T., Kim, K.: Genetic convolutional neural network for intrusion detection systems. Future Gener. Comput. Syst. 113, 418–427 (2020). https://doi.org/10.1016/j.future.2020.07.042
Wu, Z., Wang, J., Hu, L., Zhang, Z., Wu, H.: A network intrusion detection method based on semantic re-encoding and deep learning. J. Netw. Comput. Appl. 164, 102688 (2020). https://doi.org/10.1016/j.jnca.2020.102688
Kim, J., Kim, J., Kim, H., Shim, M., Choi, E.: CNN-based network intrusion detection against denial-of-service attacks. Electronics (2020). https://doi.org/10.3390/electronics9060916
Kanimozhi, V., Jacob, T.P.: Artificial intelligence based network intrusion detection with hyper-parameter optimization tuning on the realistic cyber dataset CSE-CIC-IDS2018 using cloud computing. ICT Express 5(3), 211–214 (2019). https://doi.org/10.1016/j.icte.2019.03.003
Swarna Priya, R.M., et al.: An effective feature engineering for DNN using hybrid PCA-GWO for intrusion detection in IoMT architecture. Comput. Commun. 160, 139–149 (2020). https://doi.org/10.1016/j.comcom.2020.05.048
Jia, H., Liu, J., Zhang, M., He, X., Sun, W.: Network intrusion detection based on IE-DBN model. Comput. Commun. 178, 131–140 (2021). https://doi.org/10.1016/j.comcom.2021.07.016
Onah, J.O., Abdulhamid, Si.M., Abdullahi, M., Hassan, I.H., Al-Ghusham, A.: Genetic algorithm based feature selection and Naïve Bayes for anomaly detection in fog computing environment. Mach. Learn. Appl. 6, 100156 (2021). https://doi.org/10.1016/j.mlwa.2021.100156
Hajisalem, V., Babaie, S.: A hybrid intrusion detection system based on ABC-AFS algorithm for misuse and anomaly detection. Comput. Netw. 136, 37–50 (2018). https://doi.org/10.1016/j.comnet.2018.02.028
Elmasry, W., Akbulut, A., Zaim, A.H.: Evolving deep learning architectures for network intrusion detection using a double PSO metaheuristic. Comput. Netw. 168, 107042 (2020). https://doi.org/10.1016/j.comnet.2019.107042
Vijayanand, R., Devaraj, D., Kannapiran, B.: Intrusion detection system for wireless mesh network using multiple support vector machine classifiers with genetic-algorithm-based feature selection. Comput. Secur. 77, 304–314 (2018). https://doi.org/10.1016/j.cose.2018.04.010
Li, X., Chen, W., Zhang, Q., Wu, L.: Building Auto-Encoder Intrusion Detection System based on random forest feature selection. Comput. Secur. 95, 101851 (2020). https://doi.org/10.1016/j.cose.2020.101851
Shahraki, A., Abbasi, M., Haugen, Ø.: Boosting algorithms for network intrusion detection: a comparative evaluation of real AdaBoost, gentle AdaBoost and modest AdaBoost. Eng. Appl. Artif. Intell. 94, 103770 (2020). https://doi.org/10.1016/j.engappai.2020.103770
Alazzam, H., Sharieh, A., Sabri, K.E.: A feature selection algorithm for intrusion detection system based on pigeon inspired optimizer. Expert Syst. Appl. 148, 113249 (2020). https://doi.org/10.1016/j.eswa.2020.113249
Zhou, Y., Mazzuchi, T.A., Sarkani, S.: M-AdaBoost-A based ensemble system for network intrusion detection. Expert Syst. Appl. 162, 113864 (2020). https://doi.org/10.1016/j.eswa.2020.113864
Thilagam, T., Aruna, R.: Intrusion detection for network based cloud computing by custom RC-NN and optimization. ICT Express 7(4), 512–520 (2021). https://doi.org/10.1016/j.icte.2021.04.006
Zhao, H., Li, M., Zhao, H.: Artificial intelligence based ensemble approach for intrusion detection systems. J. Vis. Commun. Image Represent. 71, 102736 (2020). https://doi.org/10.1016/j.jvcir.2019.102736
Rajesh Kanna, P., Santhi, P.: Unified deep learning approach for efficient intrusion detection system using integrated spatial-temporal features. Knowl. Based Syst. 226, 107132 (2021). https://doi.org/10.1016/j.knosys.2021.107132
Sona, A.S., Sasirekha, N.: Kulczynski indexed dragonfly feature optimization based Polytomous Adaptive Base classifier for anomaly intrusion detection. Mater. Today Proc. (2021). https://doi.org/10.1016/j.matpr.2021.01.765
Alazzam, H., Sharieh, A., Sabri, K.E.: A lightweight intelligent network intrusion detection system using OCSVM and pigeon inspired optimizer. Appl. Intell. 52(4), 3527–3544 (2022). https://doi.org/10.1007/s10489-021-02621-x
Disha, R.A., Waheed, S.: Performance analysis of machine learning models for intrusion detection system using Gini impurity-based weighted random forest (GIWRF) feature selection technique. Cybersecurity 5(1), 1 (2022). https://doi.org/10.1186/s42400-021-00103-8
Yerriswamy, T., Murtugudde, G.: An efficient algorithm for anomaly intrusion detection in a network. Glob. Trans. Proc. 2(2), 255–260 (2021). https://doi.org/10.1016/j.gltp.2021.08.066
Narayana Rao, K., Venkata Rao, K., Prasad Reddy, P.V.G.D.: A hybrid intrusion detection system based on sparse autoencoder and deep neural network. Comput. Commun. 180, 77–88 (2021). https://doi.org/10.1016/j.comcom.2021.08.026
Sharma, N.V., Yadav, N.S.: An optimal intrusion detection system using recursive feature elimination and ensemble of classifiers. Microprocess. Microsyst 85, 104293 (2021). https://doi.org/10.1016/j.micpro.2021.104293
Halim, Z., et al.: An effective genetic algorithm-based feature selection method for intrusion detection systems. Comput. Secur. 110, 102448 (2021). https://doi.org/10.1016/j.cose.2021.102448
Mazini, M., Shirazi, B., Mahdavi, I.: Anomaly network-based intrusion detection system using a reliable hybrid artificial bee colony and AdaBoost algorithms. J. King Saud Univ. Comput. Inf. Sci. 31(4), 541–553 (2019). https://doi.org/10.1016/j.jksuci.2018.03.011
Souhail, M., et al.: Network based intrusion detection using the UNSW-NB15 dataset. Int. J. Comput. Digit. Syst. 8, 477 (2019)
Hafiza Anisa, A., Anum, H., Narmeen Zakaria, B.: Network intrusion detection using oversampling technique and machine learning algorithms. PeerJ Comput. Sci. (2022). https://doi.org/10.7717/peerj-cs.820
Aljawarneh, S., Aldwairi, M., Yassein, M.B.: Anomaly-based intrusion detection system through feature selection analysis and building hybrid efficient model. J. Comput. Sci. 25, 152–160 (2018). https://doi.org/10.1016/j.jocs.2017.03.006
Tama, B.A., Comuzzi, M., Rhee, K.: TSE-IDS: a two-stage classifier ensemble for intelligent anomaly-based intrusion detection system. IEEE Access 7, 94497–94507 (2019). https://doi.org/10.1109/ACCESS.2019.2928048
Dwivedi, S., Vardhan, M., Tripathi, S., Shukla, A.K.: Implementation of adaptive scheme in evolutionary technique for anomaly-based intrusion detection. Evol. Intell. 13(1), 103–117 (2020). https://doi.org/10.1007/s12065-019-00293-8
Devan, P., Khare, N.: An efficient XGBoost–DNN-based classification model for network intrusion detection system. Neural Comput. Appl. 32(16), 12499–12514 (2020). https://doi.org/10.1007/s00521-020-04708-x
Yang, Y., Zheng, K., Wu, C., Yang, Y.: Improving the classification effectiveness of intrusion detection by using improved conditional variational autoencoder and deep neural network. Sensors (2019). https://doi.org/10.3390/s19112528
Krishnaveni, S., Vigneshwar, P., Kishore, S., Jothi, B., Sivamohan, S.: Anomaly-based intrusion detection system using support vector machine. In: Dash, S.S., Lakshmi, C., Das, S., Panigrahi, B.K. (eds.) Artificial Intelligence and Evolutionary Computations in Engineering Systems, pp. 723–731. Springer Singapore, Singapore (2020)
Ahmad, I., Ul Haq, Q.E., Imran, M., Alassafi, M.O., AlGhamdi, R.A.: An efficient network intrusion detection and classification system. Mathematics (2022). https://doi.org/10.3390/math10030530
Qureshi A.U.H., Larijani H., Ahmad J., Mtetwa N.: A novel random neural network based approach for intrusion detection systems. In 2018 10th Computer Science and Electronic Engineering (CEEC), 19–21 Sept 2018, pp. 50–55. (2018). https://doi.org/10.1109/CEEC.2018.8674228
Gao, X., Shan, C., Hu, C., Niu, Z., Liu, Z.: An adaptive ensemble machine learning model for intrusion detection. IEEE Access 7, 82512–82521 (2019). https://doi.org/10.1109/ACCESS.2019.2923640
Xiao, Y., Xing, C., Zhang, T., Zhao, Z.: An intrusion detection model based on feature reduction and convolutional neural networks. IEEE Access 7, 42210–42219 (2019). https://doi.org/10.1109/ACCESS.2019.2904620
Zhou, Y., Cheng, G., Jiang, S., Dai, M.: Building an efficient intrusion detection system based on feature selection and ensemble classifier. Comput. Netw. 174, 107247 (2020). https://doi.org/10.1016/j.comnet.2020.107247
Li, X., Yi, P., Wei, W., Jiang, Y., Tian, L.: LNNLS-KH: a feature selection method for network intrusion detection. Secur. Commun. Netw. 2021, 8830431 (2021). https://doi.org/10.1155/2021/8830431
Chiche, A., Meshesha, M.: Towards a Scalable and Adaptive Learning Approach for Network Intrusion Detection. J. Comput. Netw. Commun. 2021, 8845540 (2021). https://doi.org/10.1155/2021/8845540
Lv, L., Wang, W., Zhang, Z., Liu, X.: A novel intrusion detection system based on an optimal hybrid kernel extreme learning machine. Knowl. Based Syst. 195, 105648 (2020). https://doi.org/10.1016/j.knosys.2020.105648
Jiang, K., Wang, W., Wang, A., Wu, H.: Network intrusion detection combined hybrid sampling with deep hierarchical network. IEEE Access 8, 32464–32476 (2020). https://doi.org/10.1109/ACCESS.2020.2973730
Kumar, V., Sinha, D., Das, A.K., Pandey, S.C., Goswami, R.T.: An integrated rule based intrusion detection system: analysis on UNSW-NB15 data set and the real time online dataset. Clust. Comput. 23(2), 1397–1418 (2020). https://doi.org/10.1007/s10586-019-03008-x
Kanimozhi, V., Jacob, T.P.: Artificial intelligence outflanks all other machine learning classifiers in network intrusion detection system on the realistic cyber dataset CSE-CIC-IDS2018 using cloud computing. ICT Express 7(3), 366–370 (2021). https://doi.org/10.1016/j.icte.2020.12.004
Hadem, P., Saikia, D.K., Moulik, S.: An SDN-based intrusion detection system using SVM with selective logging for IP traceback. Comput. Netw. 191, 108015 (2021). https://doi.org/10.1016/j.comnet.2021.108015
Abbasi, J.S., Bashir, F., Qureshi, K.N., Najam ul Islam, M., Jeon, G.: Deep learning-based feature extraction and optimizing pattern matching for intrusion detection using finite state machine. Comput. Electr. Eng. 92, 107094 (2021). https://doi.org/10.1016/j.compeleceng.2021.107094
Kayode Saheed, Y., Idris Abiodun, A., Misra, S., Kristiansen Holone, M., Colomo-Palacios, R.: A machine learning-based intrusion detection for detecting internet of things network attacks. Alex. Eng. J. 61(12), 9395–9409 (2022). https://doi.org/10.1016/j.aej.2022.02.063
D’Agostini, G.: A multidimensional unfolding method based on Bayes’ theorem. Nucl. Instrum. Methods Phys. Res. Sect. A Accel. Spectrom. Detect. Assoc. Equip. 362(2), 487–498 (1995). https://doi.org/10.1016/0168-9002(95)00274-X
Box, G.E.P., Tiao, G.C.: Bayesian inference in statistical analysis. Int. Stat. Rev. 43, 242 (1973)
Ng A., Jordan M.I.: On discriminative versus generative classifiers: a comparison of logistic regression and naive Bayes. In: NIPS. (2001)
Soucy P., Mineau G. W.: A simple KNN algorithm for text categorization. In: Proceedings 2001 IEEE International Conference on Data Mining, 29 Nov-2 Dec 2001, pp. 647–648. (2001). https://doi.org/10.1109/ICDM.2001.989592.
Li, W.-C., Yi, P., Wu, Y., Pan, L., Li, J.: A new intrusion detection system based on knn classification algorithm in wireless sensor network. J. Electr. Comput. Eng. 2014, 240217 (2014)
Kotsiantis S.B.: Supervised machine learning: a review of classification techniques. In: Presented at the Proceedings of the 2007 Conference on Emerging Artificial Intelligence Applications in Computer Engineering: Real Word AI Systems with Applications in eHealth, HCI, Information Retrieval and Pervasive Technologies. (2007)
Du W., Zhan Z.: Building decision tree classifier on private data. In: Presented at the Proceedings of the IEEE International Conference on Privacy, Security and Data Mining, vol. 14, Maebashi City, Japan. (2002)
Quinlan, J.R.: Induction of decision trees. Mach. Learn. 1(1), 81–106 (1986). https://doi.org/10.1007/BF00116251
Kotsiantis, S.B.: Decision trees: a recent overview. Artif. Intell. Rev. 39(4), 261–283 (2013). https://doi.org/10.1007/s10462-011-9272-4
Loh, W.-Y.: Classification and regression trees. WIREs Data Min. Knowl. Discovery 1(1), 14–23 (2011). https://doi.org/10.1002/widm.8
Kim, G., Lee, S., Kim, S.: A novel hybrid intrusion detection method integrating anomaly detection with misuse detection. Expert Syst. Appl. 41(4), 1690–1700 (2014). https://doi.org/10.1016/j.eswa.2013.08.066
Goeschel, K.: Reducing false positives in intrusion detection systems using data-mining techniques utilizing support vector machines, decision trees, and naive Bayes for off-line analysis. SoutheastCon 2016, 1–6 (2016)
Deng, H., Runger, G., Tuv, E.: Bias of importance measures for multi-valued attributes and solutions. In: Honkela, T., Duch, W., Girolami, M., Kaski, S. (eds.) Artificial Neural Networks and Machine Learning—ICANN 2011, pp. 293–300. Springer Berlin Heidelberg, Berlin, Heidelberg (2011)
Tong, S., Koller, D.: Support vector machine active learning with applications to text classification. J. Mach. Learn. Res. 2, 45–66 (2001)
Miranda, C., Kaddoum, G., Bou-Harb, E., Garg, S., Kaur, K.: A collaborative security framework for software-defined wireless sensor networks. IEEE Trans. Inf. Forensics Secur. 15, 2602–2615 (2020). https://doi.org/10.1109/TIFS.2020.2973875
Liu, Y., Pi, D.: A novel kernel SVM algorithm with game theory for network intrusion detection. KSII Trans. Internet Inf. Syst. 11, 4043–4060 (2017)
Hu W., Liao Y., Vemuri V.R.: Robust support vector machines for anomaly detection in computer security. In: ICMLA. (2003)
Cutler, D.R., et al.: Random forests for classification in ecology. Ecology 88(11), 2783–2792 (2007). https://doi.org/10.1890/07-0539.1
Buczak, A.L., Guven, E.: A survey of data mining and machine learning methods for cyber security intrusion detection. IEEE Commun. Surv. Tutor 18, 1153–1176 (2016)
R. Doshi, N. Apthorpe, and N. Feamster, “Machine Learning DDoS Detection for Consumer Internet of Things Devices,” in 2018 IEEE Security and Privacy Workshops (SPW), 24–24 May 2018 2018, pp. 29–35, https://doi.org/10.1109/SPW.2018.00013
Pal, N.R., Pal, K., Keller, J.M., Bezdek, J.C.: A possibilistic fuzzy c-means clustering algorithm. IEEE Trans. Fuzzy Syst. 13, 517–530 (2005)
Moustafa N., Ahmed M., Ahmed S.: Data analytics-enabled intrusion detection: evaluations of ToN_IoT Linux datasets. In: 2020 IEEE 19th International Conference on Trust, Security and Privacy in Computing and Communications (TrustCom), 29 Dec–1 Jan 2021, pp. 727–735. (2020). https://doi.org/10.1109/TrustCom50675.2020.00100.
Abdi, H., Williams, L.J.: Principal component analysis. WIREs Comput. Stat. 2(4), 433–459 (2010). https://doi.org/10.1002/wics.101
Huang, G.-B., Zhu, Q.-Y., Siew, C.-K.: Extreme learning machine: theory and applications. Neurocomputing 70(1), 489–501 (2006). https://doi.org/10.1016/j.neucom.2005.12.126
LeCun, Y., Bengio, Y., Hinton, G.: Deep learning. Nature 521(7553), 436–444 (2015). https://doi.org/10.1038/nature14539
Chen, X.W., Lin, X.: Big data deep learning: challenges and perspectives. IEEE Access 2, 514–525 (2014). https://doi.org/10.1109/ACCESS.2014.2325029
Ciresan D.C., Meier U., Masci J., Gambardella L.M., Schmidhuber J.: Flexible, high performance convolutional neural networks for image classification. In: International Joint Conference on Artificial Intelligence. (2011)
Chen Y., Zhang Y., Maharjan S.: Deep learning for secure mobile edge computing. arXiv:1709.08025 (2017)
Hermans M., Schrauwen B.: Training and analyzing deep recurrent neural networks. In: NIPS 2013. (2013)
Pascanu R., Gülçehre Ç., Cho K., Bengio Y.: How to construct deep recurrent neural networks. In: CoRR. arXiv:1312.6026 (2014)
Nweke, H.F., Teh, Y.W., Al-garadi, M.A., Alo, U.R.: Deep learning algorithms for human activity recognition using mobile and wearable sensor networks: state of the art and research challenges. Expert Syst. Appl. 105, 233–261 (2018). https://doi.org/10.1016/j.eswa.2018.03.056
Tang T.A., Mhamdi L., McLernon D., Zaidi S.A.R., Ghogho M.: Deep recurrent neural network for intrusion detection in sdn-based networks. In: 2018 4th IEEE Conference on Network Softwarization and Workshops (NetSoft), 25–29 June 2018, pp. 202–206. https://doi.org/10.1109/NETSOFT.2018.8460090
Yu, Y., Si, X., Hu, C., Zhang, J.: A review of recurrent neural networks: LSTM cells and network architectures. Neural Comput. 31(7), 1235–1270 (2019). https://doi.org/10.1162/neco_a_01199
Gers F.A., Schmidhuber J., Cummins F.: Learning to forget: continual prediction with LSTM. In: 1999 Ninth International Conference on Artificial Neural Networks ICANN 99. (Conf. Publ. No. 470), 7–10 Sept. 1999, vol. 2, pp. 850–855.https://doi.org/10.1049/cp:19991218.
Bai S., Kolter J.Z., Koltun V.: An empirical evaluation of generic convolutional and recurrent networks for sequence modeling. arXiv:1803.01271 (2018)
Tschannen M., Bachem O., Lucic M.: Recent advances in autoencoder-based representation learning. arXiv:1812.05069 (2018)
Hinton, G.E.: A practical guide to training restricted Boltzmann machines. In: Montavon, G., Orr, G.B., Müller, K.-R. (eds.) Neural Networks: Tricks of the Trade, 2nd edn., pp. 599–619. Springer Berlin Heidelberg, Berlin, Heidelberg (2012)
Mayuranathan, M., Murugan, M., Dhanakoti, V.: Best features based intrusion detection system by RBM model for detecting DDoS in cloud environment. J. Ambient Intell. Humaniz. Comput. 12, 3609–3619 (2021)
Fiore, U., Palmieri, F., Castiglione, A., Santis, A.D.: Network anomaly detection with the restricted Boltzmann machine. Neurocomput. 122, 13–23 (2013). https://doi.org/10.1016/j.neucom.2012.11.050
Keyvanrad M.A., Homayounpour M.M.: A brief survey on deep belief networks and introducing a new object oriented MATLAB toolbox (DeeBNet). arXiv:1408.3264 (2014)
Dietterich, T.G.: Ensemble methods in machine learning. In: Goos, G., Hartmanis, J., van Leeuwen, J. (eds.) Multiple Classifier Systems, pp. 1–15. Springer Berlin Heidelberg, Berlin, Heidelberg (2000)
Woniak, M., Graña, M., Corchado, E.: A survey of multiple classifier systems as hybrid systems. Inf. Fusion 16, 3–17 (2014). https://doi.org/10.1016/j.inffus.2013.04.006
Illy P., Kaddoum G., Moreira C.M., Kaur K., Garg S.: securing fog-to-things environment using intrusion detection system based on ensemble learning. In: 2019 IEEE Wireless Communications and Networking Conference (WCNC), pp. 1–7. (2019)
Domingos, P.M.: A few useful things to know about machine learning. Commun. ACM 55, 78–87 (2012)
Breiman, L.: Bagging predictors. Mach. Learn. 24(2), 123–140 (1996). https://doi.org/10.1007/BF00058655
Baba, N.M., Makhtar, M., Fadzli, S.A., Awang, M.K.: Current issues in ensemble methods and its applicaTIONS. J. Theor. Appl. Inf. Technol. 8, 1 (2015)
Santana L.E.A., Silva L., Canuto A.M.P., Pintro F., Vale K.M.O.: A comparative analysis of genetic algorithm and ant colony optimization to select attributes for an heterogeneous ensemble of classifiers. In: IEEE Congress on Evolutionary Computation, pp. 1–8. (2010)
Bosman, H.H.W.J., Iacca, G., Tejada, A., Wörtche, H.J., Liotta, A.: Ensembles of incremental learners to detect anomalies in ad hoc sensor networks. Ad Hoc Netw. 35, 14–36 (2015)
Chen T., Guestrin C.: XGBoost: a scalable tree boosting system. In: Proceedings of the 22nd ACM SIGKDD International Conference on Knowledge Discovery and Data Mining. (2016)
Kumar, P., Gupta, G.P., Tripathi, R.: A distributed ensemble design based intrusion detection system using fog computing to protect the internet of things networks. J. Ambient Intell. Humaniz. Comput. 12(10), 9555–9572 (2021). https://doi.org/10.1007/s12652-020-02696-3
Ke G., et al.: LightGBM: a highly efficient gradient boosting decision tree. In: NIPS. (2017)
Aldwairi M., Alshboul M. A., Seyam A.: Characterizing realistic signature-based intrusion detection benchmarks. In: Presented at the Proceedings of the 6th International Conference on Information Technology: IoT and Smart City, Hong Kong. (2018). Available at https://doi.org/10.1145/3301551.3301591
ManoharNaik, S., Geethanjali, N.: A multi-fusion pattern matching algorithm for signature-based network intrusion detection system. Preprints 2016, 1–8 (2016). https://doi.org/10.20944/preprints201608.0197.v1
Folorunso, O., Ayo, F.E., Babalola, Y.E.: Ca-NIDS: a network intrusion detection system using combinatorial algorithm approach. J. Inf. Priv. Secur. 12(4), 181–196 (2016). https://doi.org/10.1080/15536548.2016.1257680
Rao, C.S., Raju, K.B.: MapReduce accelerated signature-based intrusion detection mechanism (IDM) with pattern matching mechanism. In: Nayak, J., Abraham, A., Krishna, B.M., Chandra Sekhar, G.T., Das, A.K. (eds.) Soft Computing in Data Analytics, pp. 157–164. Springer Singapore, Singapore (2019)
Aho, A.V., Corasick, M.J.: Efficient string matching. Commun. ACM 18, 333–340 (1975)
Alicherry, M., Muthuprasanna, M., Kumar, V.P.: High speed pattern matching for network IDS/IPS. In: Proceedings of the 2006 IEEE International Conference on Network Protocols, pp. 187–196. (2006)
Knuth, D.E., Morris, J.H., Pratt, V.R.: Fast pattern matching in strings. SIAM J. Comput. 6, 323–350 (1977)
Wu, S., Manber, U.: A fast algorithm for multi-pattern searching. (1999)
Boyer, R.S., Moore, J.S.: A fast string searching algorithm. Commun. ACM 20(10), 762–772 (1977). https://doi.org/10.1145/359842.359859
Kaur, S., Singh, M.: Hybrid intrusion detection and signature generation using deep recurrent neural networks. Neural Comput. Appl. 32(12), 7859–7877 (2020). https://doi.org/10.1007/s00521-019-04187-9
Liu, J., et al.: Adaptive intrusion detection via GA-GOGMM-based pattern learning with fuzzy rough set-based attribute selection. Expert Syst. Appl. 139, 112845 (2020). https://doi.org/10.1016/j.eswa.2019.112845
Kalavadekar, P.N., Sane, S.S.: Building an effective intrusion detection system using combined signature and anomaly detection techniques. Int. J. Innov. Technol. Explor. Eng. 8(10), 429 (2019)
Ugtakhbayar, N., Usukhbayar, B., Baigaltugs, S.: A Hybrid model for anomaly-based intrusion detection system. In: Pan, J.-S., Li, J., Tsai, P.-W., Jain, L.C. (eds.) Advances in Intelligent Information Hiding and Multimedia Signal Processing, pp. 419–431. Springer Singapore, Singapore (2020)
Asharf, J., Moustafa, N., Khurshid, H., Debie, E., Haider, W., Wahab, A.: A review of intrusion detection systems using machine and deep learning in internet of things: challenges, solutions and future directions. Electronics 9(7), 1177 (2020). https://doi.org/10.3390/electronics9071177
Bhati, N.S., Khari, M., García-Díaz, V., Verdú, E.: A Review on Intrusion Detection Systems and Techniques. Int. J. Uncertain. Fuzziness Knowl. Based Syst. 28(Supp 02), 65–91 (2020). https://doi.org/10.1142/s0218488520400140
Patel, A., Taghavi, M., Bakhtiyari, K., Celestino Júnior, J.: An intrusion detection and prevention system in cloud computing: a systematic review. J. Netw. Comput. Appl. 36(1), 25–41 (2013). https://doi.org/10.1016/j.jnca.2012.08.007
Hwang, R.H., Peng, M.C., Huang, C.W., Lin, P.C., Nguyen, V.L.: An unsupervised deep learning model for early network traffic anomaly detection. IEEE Access 8, 30387–30399 (2020). https://doi.org/10.1109/ACCESS.2020.2973023
Nagaraju, S., Shanmugham, B., Baskaran, K.: High throughput token driven FSM based regex pattern matching for network intrusion detection system. Mater. Today Proc. 47, 139–143 (2021). https://doi.org/10.1016/j.matpr.2021.04.028. Accessed 1 Jan 2021
AlYousef, M.Y., Abdelmajeed, N.T.: Dynamically detecting security threats and updating a signature-based intrusion detection system’s database. Procedia Comput. Sci. 159, 1507–1516 (2019). https://doi.org/10.1016/j.procs.2019.09.321
Almutairi A.H., Abdelmajeed N.T.: Innovative signature based intrusion detection system: parallel processing and minimized database. In: 2017 International Conference on the Frontiers and Advances in Data Science (FADS), 23–25 Oct 2017, pp. 114–119. (2017). https://doi.org/10.1109/FADS.2017.8253208.
Funding
The author did not receive any support from any organization for the submitted work.
Author information
Authors and Affiliations
Contributions
OHA came up with the idea for the article, he also performed the literature search and the drafting, while the data analysis and synthesis were carried out by OHA, TA-T, and SYK. TA-T critically revised the work and make inputs where necessary.
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that there is no conflict of interest in this paper.
Ethical approval
This article does not contain any studies with human participants or animals performed by any of the authors.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Abdulganiyu, O.H., Ait Tchakoucht, T. & Saheed, Y.K. A systematic literature review for network intrusion detection system (IDS). Int. J. Inf. Secur. 22, 1125–1162 (2023). https://doi.org/10.1007/s10207-023-00682-2
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10207-023-00682-2