Abstract
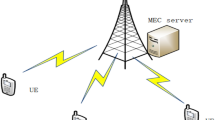
Maximizing the utility of large-scale Internet of Things (IoT) is an important issue in practice. In this paper, we attempt to improve the performance of IoT edge computing system (IoT ECS) from a perspective of task value, which decays with execution time. We consider such an IoT ECS which is composed of multiple mobile equipments (MEs) and edge nodes (ENs). Each ME holds a task with a certain task value decay curve (TVDC) that decides whether to execute locally or at the edge nodes. Further more, we use a system utility function to describe the overall performance of the network by trading-off task value, calculation cost, and network risk factor. We convert the IoT ECS utility maximization problem into a multi-knapsack and multi-dimensional knapsack problem and prove it’s NP-hard. Then, we adopt the piecewise linearization method to conquer the non-linear, even non-convex challenge of the objective function, and develop a distributed task offloading scheme based on Lagrange relaxation framework (TOS-LRPLM). Finally, numerical experiments prove the effectiveness of our proposed strategies and its superiority to others.















Similar content being viewed by others
Data availability
Data sharing is not applicable to this paper as no datasets were generated or analysed during the current study.
Code availability
The custom code required to reproduce these findings cannot be shared at this time as the code also forms part of an ongoing study.
References
Agiwal, M., Saxena, N., Roy, A.: Towards connected living: 5G enabled internet of things (IoT). IETE Tech. Rev. 36(2), 190–202 (2019)
Qiu, J., Tian, Z., Du, C., Zuo, Q., Su, S., Fang, B.: A survey on access control in the age of internet of things. IEEE Internet Things J. 7(6), 4682–4696 (2020). https://doi.org/10.1109/JIOT.2020.2969326
Yu, W., Liang, F., He, X., Hatcher, W.G., Lu, C., Lin, J., Yang, X.: A survey on the edge computing for the internet of things. IEEE Access 6, 6900–6919 (2018). https://doi.org/10.1109/ACCESS.2017.2778504
Khan, A., Othman, M., Madani, S.A., Khan, S.U.: A survey of mobile cloud computing application models. IEEE Commun. Surv. Tutor. 16(1), 393–413 (2014). https://doi.org/10.1109/SURV.2013.062613.00160
Lee, K., Chu, D., Cuervo, E., Kopf, J., Wolman, A., Degtyarev, Y., Grizan, S., Flinn, J.: Outatime: Using speculation to enable low-latency continuous interaction for mobile cloud gaming. Mobile Comput. Commun. Rev. 19(3), 14–17 (2015)
Li, C., Li, L.Y.: Cost and energy aware service provisioning for mobile client in cloud computing environment. J. Supercomput. 71(4), 1196–1223 (2015)
Wang, S., Zhang, X., Zhang, Y., Wang, L., Yang, J., Wang, W.: A survey on mobile edge networks: Convergence of computing, caching and communications. IEEE Access 5, 6757–6779 (2017). https://doi.org/10.1109/ACCESS.2017.2685434
Chen, X., Liu, Z., Chen, Y., Li, Z.: Mobile edge computing based task offloading and resource allocation in 5g ultra-dense networks. IEEE Access 7, 184172–184182 (2019). https://doi.org/10.1109/ACCESS.2019.2960547
Fan, Y., Zhai, L., Wang, H.: Cost-efficient dependent task offloading for multiusers. IEEE Access 7, 115843–115856 (2019). https://doi.org/10.1109/ACCESS.2019.2936208
Liu, F., Huang, Z., Wang, L.: Energy-efficient collaborative task computation offloading in cloud-assisted edge computing for IoT sensors. Sensors 19(5), 1 (2019)
Lin, Q., Wang, F., Xu, J.: Optimal task offloading scheduling for energy efficient D2D cooperative computing. IEEE Commun. Lett. 23(10), 1816–1820 (2019). https://doi.org/10.1109/LCOMM.2019.2931719
Hao, Y., Chen, M., Hu, L., Hossain, M.S., Ghoneim, A.: Energy efficient task caching and offloading for mobile edge computing. IEEE Access 6, 11365–11373 (2018). https://doi.org/10.1109/ACCESS.2018.2805798
Tajallifar, M., Ebrahimi, S., Javan, M.R., Mokari, N., Chiaraviglio, L.: Qos-aware joint power allocation and task offloading in a mec/nfv-enabled C-RAN network. CoRR (2019). arXiv:1912.00187
Hu, J., Li, K., Liu, C., Li, K.: Game-based task offloading of multiple mobile devices with QoS in mobile edge computing systems of limited computation capacity. ACM Trans. Embed. Comput. Syst. 19(4), 1–21 (2020). https://doi.org/10.1145/3398038
Paymard, P., Mokari, N., Orooji, M.: Task scheduling based on priority and resource allocation in multi-user multi-task mobile edge computing system. In: 2019 IEEE 30th Annual International Symposium on Personal, Indoor and Mobile Radio Communications (PIMRC), pp. 1–7 (2019). https://doi.org/10.1109/PIMRC.2019.8904174
Li, L., Zhang, H.: Delay optimization strategy for service cache and task offloading in three-tier architecture mobile edge computing system. IEEE Access 8, 170211–170224 (2020). https://doi.org/10.1109/ACCESS.2020.3023771
Wang, Y., Tao, X., Zhang, X., Zhang, P., Hou, Y.T.: Cooperative task offloading in three-tier mobile computing networks: An ADMM framework. IEEE Trans. Veh. Technol. 68(3), 2763–2776 (2019). https://doi.org/10.1109/TVT.2019.2892176
Qiao, G., Leng, S., Zhang, K., He, Y.: Collaborative task offloading in vehicular edge multi-access networks. IEEE Commun. Mag. 56(8), 48–54 (2018). https://doi.org/10.1109/MCOM.2018.1701130
Zhang, H., Yang, Y., Huang, X., Fang, C., Zhang, P.: Ultra-low latency multi-task offloading in mobile edge computing. IEEE Access 9, 32569–32581 (2021). https://doi.org/10.1109/ACCESS.2021.3061105
Howard, R.A.: Information value theory. IEEE Trans. Syst. Sci. Cybern. 2(1), 22–26 (1966)
Bisdikian, C., Kaplan, L.M., Srivastava, M.B.: On the quality and value of information in sensor networks. ACM Trans. Sens. Netw. 9(4), 4:81-48:26 (2013). https://doi.org/10.1145/2489253.2489265
Zhang, J., Li, Z., Tang, S.: Value of information aware opportunistic duty cycling in solar harvesting sensor networks. IEEE Trans. Ind. Inf. 12(1), 348–360 (2016). https://doi.org/10.1109/TII.2015.2508745
Patil, K., Turck, K.D., Fiems, D.: A two-queue model for optimising the value of information in energy-harvesting sensor networks. Perform. Eval. 119, 27–42 (2018). https://doi.org/10.1016/j.peva.2017.12.003
Gjanci, P., Petrioli, C., Basagni, S., Phillips, C.A., Bölöni, L., Turgut, D.: Path finding for maximum value of information in multi-modal underwater wireless sensor networks. IEEE Trans. Mob. Comput. 17(2), 404–418 (2018). https://doi.org/10.1109/TMC.2017.2706689
Tran, T.X., Hajisami, A., Pandey, P., Pompili, D.: Collaborative mobile edge computing in 5G networks: New paradigms, scenarios, and challenges. IEEE Commun. Mag. 55(4), 54–61 (2017). https://doi.org/10.1109/MCOM.2017.1600863
Liu, Q., Chen, Z., Wu, J., Deng, Y., Liu, K., Wang, L.: An efficient task scheduling strategy utilizing mobile edge computing in autonomous driving environment. Electronics 8(11), 1221 (2019). https://doi.org/10.3390/electronics8111221
Li, Z., Ge, J., Yang, H., Huang, L., Hu, H., Hu, H., Luo, B.: A security and cost aware scheduling algorithm for heterogeneous tasks of scientific workflow in clouds. Future Gener. Comput. Syst. 65, 140–152 (2016). https://doi.org/10.1016/j.future.2015.12.014
Wu, D., Shen, G., Huang, Z., Cao, Y., Du, T.: A trust-aware task offloading framework in mobile edge computing. IEEE Access 7, 150105–150119 (2019). https://doi.org/10.1109/ACCESS.2019.2947306
Li, M., Sun, Y., Lu, H., Maharjan, S., Tian, Z.: Deep reinforcement learning for partially observable data poisoning attack in crowdsensing systems. IEEE Internet Things J. 7(7), 6266–6278 (2020). https://doi.org/10.1109/JIOT.2019.2962914
Tian, Z., Luo, C., Qiu, J., Du, X., Guizani, M.: A distributed deep learning system for web attack detection on edge devices. IEEE Trans. Ind. Inf. 16(3), 1963–1971 (2020). https://doi.org/10.1109/TII.2019.2938778
Latifa, E., Kiram, M.A.E., Ghazouani, M.E.: New security risk value estimate method for android applications. Comput. J. 63(4), 593–603 (2020). https://doi.org/10.1093/comjnl/bxz109
Hussein, M., Mousa, M.: Efficient task offloading for IoT-based applications in fog computing using ant colony optimization. IEEE Access 8, 37191–37201 (2020). https://doi.org/10.1109/ACCESS.2020.2975741
Liu, L., Qin, X., Zhang, Z., Zhang, P.: Joint task offloading and resource allocation for obtaining fresh status updates in multi-device MEC systems. IEEE Access 8, 38248–38261 (2020). https://doi.org/10.1109/ACCESS.2020.2976048
Colbourn, C.J., Cui, M., Lloyd, E.L., Syrotiuk, V.R.: A carrier sense multiple access protocol with power backoff (CSMA/PB). Ad Hoc Netw. 5(8), 1233–1250 (2007). https://doi.org/10.1016/j.adhoc.2007.02.017
Kim, M., Chung, J.: Autonomous transmission power control for CSMA/CA-based wireless networks. In: International Conference on Information and Communication Technology Convergence, ICTC 2013, Jeju Island, South Korea, 4–16 October 2013, pp. 419–420. IEEE (2013). https://doi.org/10.1109/ICTC.2013.6675386
Correa-Posada, C.M., Sanchez-Martin, P.: Integrated power and natural gas model for energy adequacy in short-term operation. IEEE Trans. Power Syst. 30(6), 3347–3355 (2015). https://doi.org/10.1109/TPWRS.2014.2372013
Shao, C., Wang, X., Shahidehpour, M., Wang, X., Wang, B.: An milp-based optimal power flow in multicarrier energy systems. IEEE Trans. Sustain. Energy 8(1), 239–248 (2017). https://doi.org/10.1109/TSTE.2016.2595486
Boyd, S., Boyd, S.P., Vandenberghe, L.: Convex Optimization. Cambridge University Press, Cambridge (2004)
Kuhn, H.W.: The Hungarian Method for the Assignment Problem, pp. 29–47. Springer, Berlin (2010). https://doi.org/10.1007/978-3-540-68279-0_2
Wang, Y., Tao, X., Zhang, X., Mao, G.: Joint caching placement and user association for minimizing user download delay. IEEE Access 4, 8625–8633 (2016). https://doi.org/10.1109/ACCESS.2016.2633488
Diwekar, U.: Nonlinear Programming. Introduction to Applied Optimization (2008)
Karmarkar, N.: A new polynomial-time algorithm for linear programming. In: Proceedings of the sixteenth annual ACM symposium on Theory of computing, pp. 302–311 (1984)
Acknowledgements
This work is supported by the Natural Science Foundation of China (Grant No. 61872104).
Author information
Authors and Affiliations
Contributions
JS contributed to the conception of the study and performed the experiment, HW and GF contributed significantly to analysis, HL helped perform the analysis with constructive discussions, JL and ZG helped prepare the manuscript.
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that they have no conflict of interest.
Informed consent
The written informed consent for publication of this paper was obtained from the Harbin Engineering University and all authors.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Sun, J., Wang, H., Feng, G. et al. TOS-LRPLM: a task value-aware offloading scheme in IoT edge computing system. Cluster Comput 26, 319–335 (2023). https://doi.org/10.1007/s10586-021-03498-8
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10586-021-03498-8