Abstract
XOR-based visual cryptography scheme (XVCS) was proposed to solve the poor visual quality problem without darkening the background in the reconstructed secret image. However, investigations on XVCS are not sufficient. In this paper, we focus on the traditional model of VCS for general access structures and exploit some extended capabilities for XVCS. Our main contributions are: (1) we put forward constructions of perfect contrast XVCS using the linear algebraic technique without any assumptions such as participants may carry multiple shares or prior information about the shares are to be submitted during the secret reconstruction phase; (2) for some restricted access structures, we achieve perfect contrast and perfect pixel expansion, namely both 1, which is impossible for any OR-based visual cryptography scheme (OVCS); (3) for general access structures, we achieve perfect contrast with smaller pixel expansion compared with many of the results in the literature; (4) Theoretical analysis on the proposed constructions are provided, as well as extensive experimental results and comparisons for demonstrating the effectiveness and advantages of our constructions.




Similar content being viewed by others
References
Adhikari A.: Linear algebraic techniques to construct monochrome visual cryptographic schemes for general access structure and its applications to color images. Des. Codes Cryptogr. 73(3), 865–895 (2014).
Arumugam S., Lakshmanan R., Nagar A.K.: On (k, n)*-visual cryptography scheme. Des. Codes Cryptogr. 71(1), 153–162 (2014).
Ateniese G., Blundo C., De Santis A., Stinson D.R.: Visual cryptography for general access structures. Inf. Comput. 129(2), 86–106 (1996).
Blundo C., De Santis A., Stinson D.R.: On the contrast in visual cryptography schemes. J. Cryptol. 12(4), 261–289 (1999).
Blundo C., De Santis A., Naor M.: Visual cryptography for grey level images. Inf. Process. Lett. 78(6), 255–259 (2000).
Cimato S., De Prisco R., De Santis A.: Optimal colored threshold cisual cryptography schemes. Des. Codes Cryptogr. 35, 311–335 (2005).
DArco P., De Prisco R., De Santis A.: Measure-independent characterization of contrast optimal visual cryptography schemes. J. Syst. Softw. 95, 89–99 (2014).
Eisen P.A., Stinson D.R.: Threshold visual cryptography schemes with specified whiteness levels of reconstructed pixels. Des. Codes Cryptogr. 25(1), 15–61 (2002).
Fu Z.X., Yu B.: Optimal pixel expansion of deterministic visual cryptography scheme. Multimed. Tools Appl. 73(3), 1177–1193 (2014).
Guo T., Liu F., Wu C.K.: Visual cryptography for natural images and visual voting. In: Information Security and Cryptology (Inscrypt 2012). Lecture Notes in Computer Science, vol. 7763, pp. 90–101. Springer, Berlin (2013).
Guo T., Liu F., Wu C.K., Ren Y.W., Wang W.: On (k, n)-visual cryptography scheme with t essential parties. In: 7th International Conference on Information Theoretic Security (ICITS 2013). Lecture Notes in Computer Science, vol. 8317, pp. 56–68. Springer, Berlin (2014).
Hou Y.C.: Visual cryptography for color images. Pattern Recognit. 36(7), 1619–1629 (2003).
Hu C.M., Tzeng W.G.: Cheating prevention in visual cryptography. IEEE Trans. Image Process. 16(1), 36–45 (2007).
Lee S.S., Na J.C., Sohn S.W., Park C., Seo D.H., Kim S.J.: Visual cryptography based on an interferometric encryption technique. ETRI J. 24(5), 373–380 (2002).
Liu F., Guo T.: Privacy protection display implementation method based on visual passwords. CN Patent App. CN 201410542752 (2015).
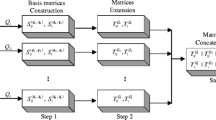
Liu F., Wu C.K., Lin X.: Step construction of visual cryptography schemes. IEEE Trans. Inf. Forensics Secur. 5(1), 27–38 (2010).
Liu F., Wua C., Lin X.: new definition of the contrast of visual cryptography scheme. Inf. Process. Lett. 110(7), 241–246 (2010).
Naor M., Shamir A.: Visual cryptography. In: Advances in Cryptology (EUROCRYPT’94). Lecture Notes in Computer Science, vol. 950, pp. 1–12. Springer, Berlin (1995).
Naor M., Pinkas B.: Visual authentication and identification. In: Advances in Cryptology (CRYPTO’97). Lecture Notes in Computer Science, vol. 1294, pp. 322–336. Springer, Berlin (1997).
Shyu S.J., Chen M.C.: Optimum pixel expansions for threshold visual secret sharing schemes. IEEE Trans. Inf. Forensics Secur. 6(3), 960–969 (2011).
Shyu S.J., Chen M.C.: Minimizing pixel expansion in visual cryptographyic scheme for general access structures. IEEE Trans. Circuits Syst. Video Technol. 25(9), 1557–1561 (2015).
Shyu S.J., Jiang H.W.: General constructions for threshold multiple-secret visual cryptographic shcemes. IEEE Trans. Inf. Forensics Secur. 8(5), 733–743 (2013).
Tuyls P., Kevenaar T., Schrijen G.J., Staring A.A.M., Van Dijk M.: Visual crypto displays enabling secure communications. In: Security in Pervasive Computing. Lecture Notes in Computer Science, vol. 2802, pp. 271–284. Springer, Berlin (2003).
Tuyls P., Hollmann H., Lint J., Tolhuizen L.: Xor-based visual cryptography schemes. Des. Codes Cryptogr. 37(1), 169–186 (2005).
Verheul E.R., van Tilborg H.C.A.: Constructions and properties of k out of n visual secret sharing schemes. Des. Codes Cryptogr. 11(2), 179–196 (1997).
Viet D.Q., Kurosawa K.: Almost ideal contrast visual cryptography with reversing. In: Topics in Cryptology-CT-RSA. Lecture Notes in Computer Science, vol. 2964, pp. 353–365. Springer, Berlin (2004).
Wang D.S., Yi F., Li X.: On general construction for extended visual cryptography schemes. Pattern Recognit. 42(11), 3071–3082 (2009).
Weir J., Yan W.Q.: A comprehensive study of visual cryptography. Trans. Data Hiding Multimed. Secur. 6010, 70–105 (2010).
Wu X., Sun W.: Extended capabilities for xor-based visual cryptography. IEEE Trans. Inf. Forensics Secur. 9(10), 1592–1605 (2014).
Yan W. Q., Jin D., Kankanhalli M. S.: Visual cryptography for print and scan applications. In: IEEE International Symposium on Circuits and Systems, pp. 572–575. IEEE Press, Toronto (2004).
Yan X.H., Shen W., Niu X.M., Yang C.N.: Halftone visual cryptography with minimum auxiliary black pixels and uniform image quality. Digit. Signal Process. 38, 53–65 (2015).
Yang C.N., Wang D.S.: Property analysis of XOR-based visual cryptography. IEEE Trans. Circuits Syst. Video Technol. 24(2), 189–197 (2014).
Yang C., Chen T., Ching M.: Embed additional private information into two-dimensional bar codes by the visual secret sharing scheme. Integr. Comput. Aided Eng. 13, 189–199 (2006).
Yu B., Shen G.: Multi-secret visual cryptography with deterministic contrast. Multimed. Tools Appl. 72(2), 1867–1886 (2014).
Acknowledgments
We would like to thank the anonymous reviewers for their important and helpful comments. This work was supported by the National Natural Science Foundation of China with Nos. 61602513 and 61671448, the Strategic Priority Research Program of the Chinese Academy of Sciences with No. XDA06010701, and the National Key R&D Program of China with No. 2016YFB0800100.
Author information
Authors and Affiliations
Corresponding author
Additional information
Communicated by C. Mitchell.
Rights and permissions
About this article
Cite this article
Shen, G., Liu, F., Fu, Z. et al. Perfect contrast XOR-based visual cryptography schemes via linear algebra. Des. Codes Cryptogr. 85, 15–37 (2017). https://doi.org/10.1007/s10623-016-0285-5
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10623-016-0285-5