Abstract
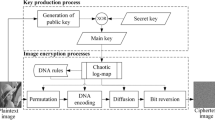
Image data has distinct regions of different importance. This property of image data has extensively been used to develop partial encryption techniques, but it is still unnoticed for total encryption. Providing similar security level to data of varied significance consumes more computational resources. This necessitates the development of an encryption framework that considers data significance while implementing total encryption. This article proposes a new framework of combinational domain encryption that encrypts significant data in spatial domain and insignificant data in wavelet domain. Experiments have been performed to analyze the effect of proposed framework as compared to encryption technique in a single domain. Significant reduction in computational time has been observed without compromising on the security. Medical applications or security applications requiring fast computation would be benefitted by implementation of the proposed technique.









Similar content being viewed by others
References
Behnia S, Akhsani A, Ahadpour S, Mahmodi H, Akhavan A (2007) A fast chaotic encryption scheme based on piecewise nonlinear chaotic maps. Phys Lett A 366(4–5):391–396
Bourbakis N, Alexopoulos C (1992) Picture data encryption using scan patterns. Pattern Recogn 25(10):567–581
Chen G, Mao YB, Chui CK (2004) A symmetric image encryption scheme based on 3D chaotic cat maps. Chaos, Solitons Fractals 12:749–761
Cheng H, Li X (2000) Partial encryption of compressed images and videos. IEEE Trans Signal Process 48(8):2439–2451
Chang HKC, Liu JL (1997) A linear quadtree compression scheme for image encryption. Signal Process, Image Commun 10(4):279–290
Chuang TJ, Lin JC (1999) A new multi-resolution approach to still image encryption. Pattern Recognit Image Anal 9(3):431–436
Dachselt F, Schwarz W (2001) Chaos and cryptography. IEEE Trans Circ Syst-I: Fundamental Theory and Applications 48(12):1498–1508
Engel D, Uhl A (2007) An attack against image-based selective bitplane encryption. In: Proc IEEE int conf image process. Texas, USA, pp 141–144
Haralick JL, Shapiro R, Boeing L (1987) Morphological edge detector. IEEE J Robot Autom 3(2):142–156
Kulkarni NS, Raman B, Gupta I (2009) Multimedia encryption: a brief overview. In: Grgic M, et al (eds) Recent Advances in multimedia signal processing and communications. Springer Verlag, pp 417–449
Lian S, Sun J, Wang Z (2005) A block cipher based on a suitable use of the chaotic standard map. Int J Chaos, Solitons Fractals, 26(1):117–129
Lian S, Sun J, Wang Z, Dai Y (2004) A fast video encryption scheme based-on chaos. In: 8th int conf control, automation, robotics and vision, vol 1, pp 126–131
Marion A (1991) An introduction to image processing. London Chapman and Hall
Norcen R, Uhl A (2004) Encryption of wavelet-coded imagery using random permutations. In: Proc IEEE int conf image process, Singapore, October 2004, pp 3431–3434
Pareek NK, Patidar V, Sud KK (2006) Image encryption using chaotic logistic map. Image Vis Comput 24(9):926–934
Peterson G (1997) Arnold’s cat map. Available online at http://online.redwoods.ca.ca.us/instruct/darnold/maw/catmap3.htm
Podesser M, Schmidt H-P, Uhl A (2002) Selective bitplane encryption for secure transmission of image data in mobile environments. In: Proceedings of 5th Nordic signal processing symposium
Seo Y-H, Kim D-W, Yoo J-S, Dey S, Agrawal A (2003) Wavelet domain image encryption by subband selection and data bit selection. World Wide Congress (3G Wireless), San Francisco
Schneier B (1996) Applied cryptography second edition: protocols, algorithms, and source code in C. New York: Wiley Publications
Subba Rao YV, Mitra A, Mahadeva Prasanna SR (2006) A partial image encryption method with pseudo random sequences. In: Bagchi A, Atluri V (eds) ICISS 2006. LNCS 4332, pp 315–325
Taneja N, Raman B, Gupta I (2009) Partial encryption on SPIHT compressed images. Lect Notes Comput Sci 5909:426–431
Uhl A, Pommer A (2005) Application scenarios for the encryption of still visual data. Image and video encryption from Digital Rights Management to secured personal communication, vol. 15, Advances in Information Security, Springer-Verlag, pp 31–43
Van Droogenbroeck M, Benedett R (2002) Techniques for a selective encryption of uncompressed and compressed images. In: Proceedings of advanced concepts for intelligent vision systems (ACIVS)
Yang H, Liao X, Wong K-w, Zhang W, Wei P (2007) A new cryptosystem based on chaotic map and operations algebraic. Chaos, Solitons Fractals 4(5):2520–2531
Yekkala A, Veni Madhavan CE (2007) Bit plane encoding and encryption. In: Ghosh A, De RK, Pal SK (eds) PReMI 2007. LNCS, 4815, pp 103–110
Zeng W, Lei S (2003) Efficient frequency domain selective scrambling of digital video. IEEE Trans Multimedia 5(1):118–129
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Taneja, N., Raman, B. & Gupta, I. Combinational domain encryption for still visual data. Multimed Tools Appl 59, 775–793 (2012). https://doi.org/10.1007/s11042-011-0775-4
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-011-0775-4