Abstract
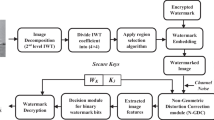
MP3 is a promising carrier format for covert communication, and how to secure its fidelity and integrity is a significant problem. In this paper, we propose a semi-fragile MP3 watermarking method for tamper detection by exploiting the rule of window switching during encoding. The method carries out embedding by establishing a mapping relationship between the type of window and the MD5 of authentication information. Moreover, we design a tamper detection method by analysing the watermark bits sequence. The experimental results show the effectiveness of the proposed method in terms of accuracy for tamper detection, time efficiency, imperceptibility and advisable robustness with compressed MP3 audio.













Similar content being viewed by others
References
Brandenburg K, Sporer T (1992) -NMR-and-Masking Flag-: Evaluation of Quality Using Perceptual Criteria, Audio engineering society conference: 11th international conference: test & measurement
Chen F, He HJ, Wang HX (2008) A fragile watermarking scheme for audio detection and recovery, 2008. CISP08. Congress on Image and Signal Processing, IEEE, 5, 135–138
Cvejic N, Seppanen T (2004) A novel scheme for merging digital audio watermarking and authentication, The IEEE 6th Workshop on Multimedia Signal Processing, IEEE, 151–154
Di Martino et al (2012) Fragile watermarking tamper detection with images compressed by fuzzy transform. Inf Sci 195:62–90
Erfani Y, Pichevar R, Rouat J (2013) Audio tampering localization using modified iss watermarking in sparse-domain, 2013 IEEE Global Conference on Signal and Information Processing (GlobalSIP). IEEE, pp 249–252
Fan MQ, Liu PP, Wang HX et al (2013) A semi-fragile watermarking scheme for authenticating audio signal based on dual-tree complex wavelet transform and discrete cosine transform. Int J Comput Math 90(12):2588–2602
Ghobadi A, Boroujerdizadeh A, Yaribakht AH et al (2013) Blind audio watermarking for tamper detection based on LSB, The 2013 15th International Conference on Advanced Communication Technology (ICACT). IEEE, pp 1077–1082
Ghosal SK, Mandal JK (2014) Binomial transform based fragile watermarking for image authentication. J Inf Secur Appl 19(4):272–281
Hu HT, Hsu LY, Chou HH (2014) Variable-dimensional vector modulation for perceptual-based DWT blind audio watermarking with adjustable payload capacity. Digit Signal Process 31:115–123
ISO/IEC, Information technology C coding of moving pictures and associated audio for digital storage media at up to about 1.5 M bit/s C part3: audio IS 11172-3(1993)
International Telecommunication Union, Method for objective measurements of perceived audio quality (PEAQ), ITU-RBS, 1387-1(1998-2001)
Katzenbeisser S, Petitcolas FAP (2000) Information hiding techniques for steganography and digital watermarking, Artech House
Lei BY, Soon Y, Li Z (2011) Blind and robust audio watermarking scheme based on SVDCDCT. Signal Process 91(8):1973–1984
Li J, Wang R, Yan D et al (2014) A multipurpose audio aggregation watermarking based on multistage vector quantization. Multimed Tools Appl 68 (3):571–593
Liu F, Xie T (2012) How to break EAP-MD5, Information Security Theory and Practice. Security, Privacy and Trust in Computing Systems and Ambient Intelligent Ecosystems. Springer Berlin Heidelberg, pp 49–57
Megias D, Herrera J, Minguillon J (2003) A robust audio watermarking scheme based on MPEG 1 layer 3 compression, Communications and Multimedia Security. Advanced Techniques for Network and Data Protection
Petitcolas FAP (2004) Stirmark benchmark 4.0. Available from http://www.petitcolas.net/fabien/watermarking/stirmark/ http://www.petitcolas.net/fabien/watermarking/stirmark/
Preda RO (2013) Semi-fragile watermarking for image authentication with sensitive tamper localization in the wavelet domain. Measurement 46(1):367–373
Quan X, Zhang H (2004) Perceptual criterion based fragile audio watermarking using adaptive wavelet packets, Proceedings of the 17th International Conference on Pattern Recognition, ICPR 2004. IEEE, 2, 867–870
Rivest R (2004) The MD5 message-digest algorithm, 1992, RFC1321, Internet Activities Board, Internet Engineering Task Force
Su PC, Wu CS et al (2011) A practical design of digital video watermarking in H. 264/AVC for content authentication. Signal Process Image Commun 26(8):413–426
Tong X et al (2013) A novel chaos-based fragile watermarking for image tampering detection and self-recovery. Signal Process Image Commun 28(3):301–308
Unoki M, Miyauchi R (2012) Detection of tampering in speech signals with inaudible watermarking technique, The 2012 Eighth International Conference on Intelligent Information Hiding and Multimedia Signal Processing (IIH-MSP), IEEE, 118–121
Wang X, Yu H (2005) How to break MD5 and other hash functions, Advances in CryptologyCEUROCRYPT 2005. Springer Berlin Heidelberg, pp 19–35
Wang HX, Fan MQ (2010) Centroid-based semi-fragile audio watermarking in hybrid domain. Sci China Inf Sci 53(3):619–633
Wang CC, Lin YC (2010) An automated system for monitoring the visual quality and authenticity of satellite video streams using a fragile watermarking approach. Digit Signal Process 20(3):780–792
Wang J, Healy R, Timoney J (2011) A robust audio watermarking scheme based on reduced singular value decomposition and distortion removal. Signal Process 91 (8):1693–1708
Wang X, Niu P, Lu M (2011) A robust digital audio watermarking scheme using wavelet moment invariance. J Syst Softw 84(8):1408–1421
Xijin W, Linxiu F (2012) The application research of MD5 encryption algorithm in DCT digital Watermarking. Phys Proced 25:1264–1269
Xu D, Wang R, Wang J (2011) A novel watermarking scheme for H. 264/AVC video authentication. Signal Process Image Commun 26(6):267–279
Yan D, Wang D (2011) Huffman table swapping-based steganography for MP3 audio. Multimed Tools Appl 52(2&3):291–305
Yan D, Wang R, Yu X et al (2012) Steganography for MP3 audio by exploiting the rule of window switching. Comput Secur 31(5):704–716
Yu D, Sattar F, Barkat B (2006) Multiresolution fragile watermarking using complex chirp signals for content authentication. Pattern Recogn 39(5):935–952
You J, Reiter U, Hannuksela MM et al (2010) Perceptual-based quality assessment for audioCvisual services: A survey. Signal Process Image Commun 25 (7):482–501
Zhao H, Shen D (2010) An audio watermarking algorithm for audio authentication, The 2010 IEEE International Conference on Information Theory and Information Security (ICITIS), IEEE, 807–80
Zhang J, Han B (2011) Fragile audio watermarking scheme based on sample mean sequence, 2011 International Conference on Multimedia Technology (ICMT). IEEE, 333–336
Acknowledgments
This work was partially supported by the National Natural Science Foundation of China under Grants 61573125 and 61371155, and the Anhui Provincial Natural Science Foundation under Grants 1608085MF131, 1508085MF132, and 1508085QF129. The authors would like to thank the Editors and anonymous referees for their comments and suggestions. They would also like to thank Dr. X. Liu for his help in academic writing.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Su, Z., Chang, L., Zhang, G. et al. Window switching strategy based semi-fragile watermarking for MP3 tamper detection. Multimed Tools Appl 76, 9363–9386 (2017). https://doi.org/10.1007/s11042-016-3539-3
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-016-3539-3