Abstract
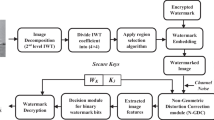
In the present paper, an advanced encryption technique commonly known as Elliptic Curve Cryptography (ECC) is used to embed a binary image as a watermark in five grayscale host images in a semi-blind manner. The ECC algorithm is a fast encryption technique which successfully encrypts the subject with significantly less number of bits as compared to other popular encryption algorithms such as Rivest-Shamir-Adleman (RSA) and Direct Selling Association (DSA). In the proposed watermarking scheme, embedding in the grayscale host images is carried out in DWT-SVD domain. First, entropy based Human Visual System (HVS) parameters are computed block wise to identify the most appropriate blocks in spatial domain. First level DWT is computed for these selected blocks and watermark embedding is carried out by using the calculated Singular Value Decomposition (SVD) parameters. Preliminary results of this work show that proposed scheme outperforms the other similar schemes carried out in DCT-SVD domain without using any encryption method. It is concluded that the use of DWT-SVD hybrid architecture along with the fast encryption technique ECC is responsible for better performance in present case. In the second part of this simulation, an established HVS model working in DCT domain is implemented and compared with the entropy based HVS model implemented in transform domain to embed the ECC encrypted binary watermark in images. In this case also, proposed scheme performs better both in terms of visual imperceptibility and robustness as compared to other scheme. It is concluded that HVS parameters – Luminance, Contrast and Edge Sensitivity are better placed in comparison to entropy parameters to examine image features and characteristics for watermarking purpose.













Similar content being viewed by others
References
Agarwal C, Mishra A (2010) A Novel Image Watermarking Technique using Fuzzy-BP Network. Proc Sixth Int Conf Intell Inform Hiding Multimed Sign Process, 102–105
Agarwal C, Mishra A, Sharma A (2011) Digital image watermarking in DCT domain using fuzzy inference system. In Twenty fourth IEEE Canadian conference on electrical and computer engineering (CCECE 2011); 822–825
Agarwal C, Mishra A, Sharma A (2013) Gray-Scale image watermarking using GA-BPN Hybrid Network. J Visual Commun Image Represent, Elsevier 24:1135–1146
Agarwal C, Mishra A, Mishra A (2015) A novel gray-scale image watermarking using hybrid Fuzzy-BPN Architecture. Egypt Inform J, Elsevier 16:83–102
Ashino R, Morimoto A Michihiro Nagase and Remi Vaillancourt “Image Compression with Multiresolution Singular Value Decomposition and Other Methods”, http://www.crm.umontreal.ca/pub/Rapports/2900-2999/2939.pdf, pp. 1–17
Bakhtiari S, Ibrahim S, Salleh M, Bakhtiari M (2014) “JPEG Image Encryption with Elliptic Curve Cryptography” International Symposium on Biometrics and Security Technologies (ISBAST), Malaysia, 144–149
Cao L “Singular Value Decomposition Applied to Digital Image Processing” https://www.math.cuhk.edu.hk/~lmlui/CaoSVDintro.pdf, pp. 1–15
Chandra Mohan B, Srinivas Kumar S (2008) A Robust Image Watermarking Scheme Using Singular Value Decomposition. J Multimed 3(1):7–15
Cox IJ, Kilian J, Thomson Leighton F, Shamoon T (1997) Secure Spread Spectrum Watermarking for Multimedia. IEEE Trans Image Process 6(12):1673–1687
Cui J, Liu Y, Xu Y, Zhao H, Zha H (2013) Tracking generic human motion via fusion of low- and high-dimensional approaches. IEEE Trans Syst, Man, Cybernet: Syst 43(4)
Dey N, Samanta S, Chakraborty S, Das A, Chaudhuri S, Suri J (2014) Firefly Algorithm for Optimization of Scaling Factors during Embedding of Manifold Medical Information: An Application in Ophthalmology Imaging. J Med Imag Health Inform (4), 384–394
Głowacz A, Grega M, Gwiazda P, Janowski L, Leszczuk M, Romaniak P, Romano SP (2009) Automated Qualitative Assessment of Multi-Modal Distortions in Digital Images Based on GLZ. Ann Telecommun - Annales des Télécommunications 65(1):3–17
Gonzalez RC, Woods RE, Eddins SL (2005) Digital Image Processing Using MATLAB. Pearson Education, 406
Gupta R, Jain S, Mishra A (2015) Watermarking System for Encrypted Images at Cloud to check reliability of Images in IEEE Conference in NGCT-2015, 4-5 September. UPES, Dehradun
Kankanahalli M (1998), “Content Based Watermarking for Images”, Proc. 6th ACM International Multimedia Conference, ACM-MM 98, Bristol, UK, 61–70
Lai C-C (2011) An improved SVD based watermarking scheme using human visual characteristics. Optics Commun (Elsevier) 284:938–944
Liu Y, Yu Z, Liang Y, Liu S, Rosenblum DS (2016) Urban Water Quality Prediction Based on Multi-task Multi-view Learning. Proc Twenty-Fifth Int Joint Conf Artif Intell (IJCAI-16)
Liu L, Cheng L, Liu Y, Jia Y, Rosenblum DS (2016) Recognizing Complex Activities by a Probabilistic Interval-Based Model", Proceedings of the Thirtieth AAAI Conference on Artificial Intelligence (AAAI-16) February 12-17, Phoenix Arizona, USA
Ye Liu, Liqiang Nie, Li Liu, David S.Rosenblum,” From action to activity: Sensor-based activity recognition”, in Neurocomputing, Elsevier,Volume 181, 12 March 2016, Pages 108–115
Liu Y, Zhang L, Nie L, Yan Y, Rosenblum DS Fortune Teller: Predicting Your Career Path", Proceedings of the Thirtieth AAAI Conference on Artificial Intelligence (AAAI-16)
Liuy Y, Niey L, Hanx L, Zhangy L, Rosenblum DS (2015) Action2Activity: Recognizing Complex Activities from Sensor Data. Proc Twenty-Fourth Int Joint Conf Artif Intell (IJCAI)
Lou D-C, Hu M-C, Liu J-L (2008) Healthcare image watermarking scheme based on human visual model and back-propagation network. J C.C.I.T 37(1):151–162
Maity SP, Kundu MK (2002) Information theoretic approach in spatial image watermarking. ICCVG 2002(25–29):1–6
Maity SP, Kundu MK, Nandi PK (2003) “Robust and Low Cost Watermarking Using Image Characteristics”, In the Proceedings of ICAPR, Kolkata, India , pp. 351-354
Mehta R, Rajpal N (2013) A Hybrid Semi-Blind Gray Scale Image Watermarking Algorithm Based on DWT-SVD using Human Visual System Model", in Contemporary Computing (IC3), 2013 Sixth International IEEE Conference
Mehta R, Mishra A, Singh R, Rajpal N (2010) Digital Image Watermarking in DCT Domain Using Finite Newton Support Vector Regression. Sixth IEEE Int Conf Intell Inform Hiding Multimed Sign Process (IIH-MSP 2010), 123–126
Mishra A, Goel A, Singh R, Chetty G and Singh L (2012) “A Novel Image Watermarking Scheme Using Extreme Learning Machine”, In Proceedings of IEEE World Congress on Computational Intelligence (WCCI 2012), Brisbane, Australia, June 10-15, 1–6
Mohanty SP, Ramakrishnan KR, Kankanhalli M (1999) A Dual Watermarking Technique for Images. ACM Multimedia, Part 2, pp. 49–51
Motwani MC, Harris FC Jr, (2009) Fuzzy Perceptual Watermarking for Ownership Verification. Proceedings of the 2009 International Conference on Image Processing, Computer Vision, and Pattern Recognition (IPCV'09), Las Vegas, Nevada, July 13–16
Pal NR, Pal SK (1989) Object-background segmentation using new definitions of entropy. IEE Proceedings 139(4):284–295
Piao C-R, Beack S, Woo D-M, Han S-S (2006) A Blind Watermarking Algorithm Based on HVS and RBF Neural Network for Digital Image. ICNC 2006, Part I, LNCS 4221:493–496
Rowayda A. Sadek “SVD Based Image Processing Applications: State of The Art, Contributions and Research Challenges”. Int J Adv Comput Sci Appl, Vol. 3, No. 7 (2012), pp. 26–34
Singh R, Dabas N, Chaudhry V and Mishra A (2014) “On Extreme Learning Machine for Watermarking of Images in Discrete Wavelet Transform Domain”, In Proceedings of IEEE 10th International Conference on Intelligent Information Hiding and Multimedia Signal Processing (IIH-MSP 2014), 27–29 August, , Kitakyushu, Japan
Tsai H-H, Jhuang Y-J, Lai Y-S (2012) An SVD-based image watermarking in wavelet domain using SVR and PSO. Appl Soft Comput 12(8):2442–2453
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Gupta, R., Mishra, A. & Jain, S. A semi-blind HVS based image watermarking scheme using elliptic curve cryptography. Multimed Tools Appl 77, 19235–19260 (2018). https://doi.org/10.1007/s11042-017-5351-0
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-017-5351-0