Abstract
This paper introduces a six-dimensional discrete chaotic systems (SDDCS) with some simple sine functions and a chaotic pseudorandom number generator (CPRNG) that is designed based on the SDDCS. A encryption scheme with both key avalanche effect and plaintext avalanche effect (SESKPAE) is proposed by using the random sequence generated by the CPRNG. The algorithm has three advantages: First, the initial values of the chaotic system are calculated by using the SHA-256 hash value of the plain image and the given values, there are different initial values for different plain images. Thus, our algorithm can resist against the chosen-plaintext and known-plaintext attacks effectively. Second, the new algorithm adopts ciphertext feedback mechanism to further strengthen the safety. Third, our new algorithm has an “avalanche effect”, in other words, the decrypted ciphertext will become a “white” image with a few “black spots” rather than a random chaotic image as a result of the wrong key. The experimental results and security analysis show that the algorithm has the advantages of large key space, no obvious statistical characteristics of ciphertext, sensitive to plaintext and keys, and able to resist chosen-plaintext attack and active attacks.














Similar content being viewed by others
Explore related subjects
Discover the latest articles and news from researchers in related subjects, suggested using machine learning.References
Chen XF, Huang XY, Li J (2015) New algorithms for secure outsourcing of large-scale systems of linear equations. IEEE Trans Inf Forensics Secur 10(1):69–78
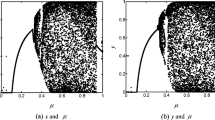
Chen E, Min LQ, Chen GR (2017) Discrete chaotic systems with one-line equilibria and their application to image encryption. Int J Bifurcation Chaos 27:1750046-1-17
Feistel H (1973) Cryptography and computer privacy. Sci Amer Mag 228:15–23
Hamza R (2017) A novel pseudo random sequence generator for image-cryptographic applications. J Inf Secur Appl 35:119–127
Huang XL, Ye GD (2014) An image encryption algorithm based on hyper-chaos and DNA sequence. Multimedia Tools Appl 72:57–70
Huang ZG, Liu SL, Mao XP (2017) Insight of the protection for data security under selective opening attacks. Inf Sci 412:223–241
Jain A, Rajpal N (2016) A robust image encryption algorithm resistant to attacks using DNA and chaotic logistic maps. Multimedia Tools Appl 75:5455–5472
Lai Q, Chen SM (2016) Research on a new 3D autonomous chaotic system with coexisting attractors. Optik 127:3000–3004
Lambi D (2017) Cryptanalyzing a novel pseudorandom number generator based on pseudorandomly enhanced logistic map. Nonlinear Dyn 89:2255–2257
Li J, Huang XY, Li JW, Chen XF, Xiang Y (2014) Securely outsourcing attribute-based encryption with checkability. IEEE Trans Parallel Distrib Syst 25(8):2201–2210
Li J, Li JW, Chen XF et al (2015) Identity-based encryption with outsourced revocation in cloud computing. IEEE Trans Comput 64(2):425–437
Li J, Li YK, Chen XF et al (2015) A hybrid cloud approach for secure authorized deduplication. IEEE Trans Parallel Distrib Syst 26(5):1206–1216
Li P, Li J, Huang ZG et al (2017) Multi-key privacy-preserving deep learning in cloud computing. Futur Gener Comput Syst 74:76–85
Liu HJ, Wang XY (2010) Color image encryption based on one-time keys and robust chaotic maps. Comput Math Appl 59:3320–3327
Liu HJ, Wang XY (2011) Color image encryption using spatial bit-level permutation and high-dimension chaotic system. Opt Commun 284:3895–3903
Liu L, Zhang Q, Wei XP (2012) A RGB image encryption algorithm based on DNA encoding and chaos map. Comput Electr Eng 38:1240–1248
Liu Y, Tang J, Xie T (2014) Cryptanalyzing a RGB image encryption algorithm based on DNA encoding and chaos map. Opt Lasers Eng 60:1–5
Liu Q, Wang GJ, Liu XH, Peng T, Wu J (2017) Achieving reliable and secure services in cloud computing environments. Comput Electr Eng 59:153–164
Min LQ, Chen GR (2013) A novel stream encryption scheme with avalanche effect. Eur Phys J B 86(11):459
Mohammad AA, Fatimah AA, Mahmoud AA (2018) Impact of digital fingerprint image quality on the fingerprint recognition accuracy. Multimed Tools Appl. https://doi.org/10.1007/s11042-017-5537-5
Murillo-Escobar MA, Cruz-Hernández C et al (2017) A novel pseudorandom number generator based on pseudorandomly enhanced logistic map. Nonlinear Dyn 87:407–425
Pang S, Liu Y (2011) A new hyperchaotic system from the Lü system and its control. J Comput Appl Math 235:2775–2789
Qi GY, Chen GR, van Wyk MA, van Wyk BJ, Zhang YH (2008) A four-wing chaotic attractor generated from a new 3D quadratic autonomous system. Chaos, Solitons Fractrals 38:705–721
Rukhin R, Soto J, Nechvatal J (2001) A statistical test suite for random and pseudorandom numbergenerator for cryptographic applications. NIST Special Publication
Shannon CE (1949) Communication theory of security systems. Bell Syst Tech J 28:656–715
Spillman RJ (2005) Classical and contemporary cryptology. Pearson Education INC, Upper Saddle River
Sprott JC (2003) Chaos and time-series analysis. Oxford University Press, Oxford
Sprott JC, Wang X, Chen GR (2013) Coexistence point, periodic and strange attractors. Int J Bifurcation Chaos 23:1350093
Sun KH, Liu X, Zhu CX, Sprott J (2012) Hyperchaos and hyperchaos control of the sinusoidally forced simplified Lorenz system. Nonlinear Dyn 69:1383–1391
Wang X, Teng Y, Qin X (2012) A novel colour image encryption algorithm based on chaos. Signal Process 92:1101–1108
Wu Y, Hua Z, Zhou Y (2015) N-dimensional discrete cat map generation using Laplace expansions. IEEE Trans Cybern 46:2622–2633
Wu X, Zhu B, Hu Y (2017) A novel colour image encryption scheme using rectangular transform-enhanced chaotic tent maps. IEEE Acces 5:6429–6436
Yang XP, Min LQ, Wang X (2015) A cubic map chaos criterion theorem with applications in generalized synchronization based pseudorandom number generator and image encryption. Chaos 25:053104
Yu S, Wang GJ, Zhou WL (2015) Modeling malicious activities in cyber space. IEEE Netw 29(6):83–87
Yu CY, Li JZ, Li X, Ren XC, Gupta BB (2018) Four-image encryption scheme based on quaternion Fresnel transform, chaos and computer generated hologram. Multimed Tools Appl 77:4585–4608
Zarei A (2015) Complex dynamics in a 5-D hyper-chaotic attractor with four-wing, one equilibrium and multiple chaotic attractors. Nonlinear Dyn 81:585–605
Zhang XP, Mao YB, Zhao ZM (2014) An efficient chaotic image encryption based on alternate circular Sboxes. Nonlinear Dyn 78:359–369
Zhang XP, Zhao ZM, Wang JY (2014) Chaotic image encryption based on circular substitution box and key stream buffer. Signal Process Image 29:902–913
Zhu CX (2012) A novel image encryption scheme based on improved hyperchaotic sequences. Opt Commun 285(1):29–37
Zhu CX, Sun KH (2012) Cryptanalysis and improvement of a class of hyperchaos based image encryption algorithms. Acta Phys Sin 61(12):120503
Zhu CX, Sun KH (2018) Cryptanalyzing and improving a novel color image encryption algorithm using RT-enhanced chaotic tent maps. IEEE Access 6:18759–18770
Acknowledgements
This work was supported by National Natural Science Foundation of China (No. 61472451), the Open Project of Guangxi Colleges and Universities Key Laboratory of Complex System Optimization and Big Data Processing (No. 2016CSOBDP0103), the Shan Dong Province Nature Science Foundation (Grant. ZR2017MEM019) and the Science Research Fund of Liaocheng University (No. 318011606).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Zhu, S., Zhu, C. Image encryption algorithm with an avalanche effect based on a six-dimensional discrete chaotic system. Multimed Tools Appl 77, 29119–29142 (2018). https://doi.org/10.1007/s11042-018-6078-2
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-018-6078-2