Abstract
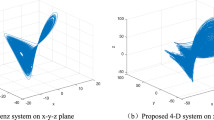
An image cryptosystem using chaotic compressive sensing is designed to achieve simultaneous compression - encryption. Compressive sensing requires a measurement matrix to compressively sample a sparse signal and to guarantee its recovery at the receiver. In this paper, a new one-dimensional chaotic map is proposed which is used to construct the chaotic measurement matrix. Performance analysis demonstrates that the proposed chaotic map is highly chaotic, ergodic, highly sensitive to the initial conditions and suitable for chaotic compressive sensing. The parameters of the chaotic system are used as the secret key in the construction of measurement matrix and also the masking matrix. The sparse representation of the image is obtained using discrete wavelet transform. The sparse coefficients are then compressively sampled and encrypted using the chaotic measurement matrix and masking matrix. A parallel compressive sensing framework is employed which greatly improves the efficiency of the proposed chaotic compressive sensing scheme. Simulation results shows that the proposed scheme has good security performance against various attacks and better reconstruction performance, when compared with the commonly used random measurement matrix.












Similar content being viewed by others
References
Badve O, Gupta BB, Gupta S (2016) Reviewing the security features in contemporary security policies and models for multiple platforms. In Handbook of Research on Modern Cryptographic Solutions for Computer and Cyber Security. 479–504
Bandeira AS, Dobriban E, Mixon DG, Sawin WF (2013) Certifying the restricted isometry property is hard. IEEE Trans Inf Theory 59:3448–3450
Belazi A, Abd El-Latif AA, Belghith S (2016) A novel image encryption scheme based on substitution-permutation network and chaos. Signal Process 128:155–170
Cambareri V, Mangia M, Pareschi F, Rovatti R, Setti G (2015) On known-plaintext attacks to a compressed sensing-based encryption: a quantitative analysis. IEEE Trans Inf Forensics Secur 10:2182–2195
Candes EJ (2008) The restricted isometry property and its implications for compressed sensing. Comptes Rendus Math 346:589–592
Candes EJ, Wakin MB (2008) An introduction to compressive sampling. IEEE Signal Process Mag 25:21–30
Chen X, Huang X, Li J, Ma J, Lou W, Wong DS (2015) New algorithms for secure outsourcing of large-scale systems of linear equations. IEEE Trans Inf Forensics Secur 10:69–78
Deepak M, Ashwin V, Amutha R (2014) A new Multistage multiple image encryption using a combination of Chaotic Block Cipher and Iterative Fractional Fourier Transform. In First International Conference on Networks & Soft Computing (ICNSC 2014): 360–364
Deng J, Zhao S, Wang Y, Wang L, Wang H, Sha H (2017) Image compression-encryption scheme combining 2D compressive sensing with discrete fractional random transform. Multimed Tools Appl 76:10097–10117
Donoho DL (2006) Compressed sensing. IEEE Trans Inf Theory 52:1289–1306
Fay R (2016) Introducing the counter mode of operation to compressed sensing based encryption. Inf Process Lett 116:279–283
Fay R, Ruland C (2016) Compressive Sensing encryption modes and their security. In 11th International Conference for Internet Technology and Secured Transactions (ICITST 2016):119–126
Hanis S, Amutha R (2017) Double image compression and encryption scheme using logistic mapped convolution and cellular automata. Multimed Tools Appl 1–16
Hu G, Xiao D, Wang Y, Xiang T (2017) An image coding scheme using parallel compressive sensing for simultaneous compression-encryption applications. J Vis Commun Image Represent 44:116–127
Hu G, Xiao D, Wang Y, Xiang T, Zhou Q (2017) Securing image information using double random phase encoding and parallel compressive sensing with updated sampling processes. Opt Lasers Eng 98:123–133
Huang Z, Liu S, Mao X, Chen K, Li J (2017) Insight of the protection for data security under selective opening attacks. Inf Sci 412–413:223–241
Li J, Huang X, Li J, Chen X, Xiang Y (2014) Securely outsourcing attribute-based encryption with checkability. IEEE Trans Parallel Distrib Syst 25:2201–2210
Li J, Li J, Chen X, Jia C, Lou W (2015) Identity-based encryption with outsourced revocation in cloud computing. IEEE Trans Comput 64:425–437
Li J, Li YK, Chen X, Lee PP, Lou W (2015) A hybrid cloud approach for secure authorized deduplication. IEEE Trans Parallel Distrib Syst 26(5):1206–1216
Li P, Li J, Huang Z, Tong G, Chong Z, Yiu SM, Chen K (2017) Multi-key privacy-preserving deep learning in cloud computing. Futur Gener Comput 74:76–85
Mahesh M, Srinivasan D, Kankanala M, Amutha R (2015) Image cryptography using Discrete Haar Wavelet transform and Arnold Cat Map. In International Conference on Communication and Signal Processing (ICCSP 2015):1849–1855
Mohimani H, Babaie-Zadeh M, Jutten C (2009) A fast approach for Overcomplete sparse decomposition based on smoothed L0 norm. IEEE Trans Signal Process 57:289–301
Peng H, Tian Y, Kurths J, Li L, Yang Y, Wang D (2017) Secure and energy-efficient data transmission system based on chaotic compressive sensing in body-to-body networks. IEEE Trans Biomed Circuits Syst 11:558–573
Phamila AVY, Amutha R (2013) Low complexity energy efficient very low bit-rate image compression scheme for wireless sensor network. Inf Process Lett 113:672–676
Phamila AVY, Amutha R (2015) Energy-efficient low bit rate image compression in wavelet domain for wireless image sensor networks. Electron Lett 51:824–826
Ponnaian D, Chandranbabu K (2017) Crypt analysis of an image compression--encryption algorithm and a modified scheme using compressive sensing. Opt J Light Electron Opt 147:263–276
Ponuma R, Amutha R (2017) Compressive sensing-based image compression-encryption using novel 1D-chaotic map. Multimed Tools Appl:1–26
Ponuma R, Aarthi V, Amutha R (2016) Cosine Number Transform based hybrid image compression-encryption. In IEEE International Conference on Wireless Communications, Signal Processing and Networking (WiSPNET 2016):172–176
Pudi V, Chattopadhyay A, Lam K-Y (2017) Secure and lightweight compressive sensing using stream cipher. IEEE Trans Circuits Syst II: Express Briefs:371–375
Wu Y, Zhou Y, Saveriades G et al (2013) Local Shannon entropy measure with statistical tests for image randomness. Inf Sci 222:323–342
Yang Z, Yan W, Xiang Y (2015) On the security of compressed sensing-based signal cryptosystem. IEEE Trans Emerg Top Comput 3:363–371
Yaseen Q, Aldwairi M, Jararweh Y, Al-Ayyoub M, Gupta B (2018) Collusion attacks mitigation in internet of things: a fog based model. Multimed Tools Appl 77:18249–18268
Yu L, Barbot JP, Zheng G, Sun H (2010) Compressive sensing with chaotic sequence. IEEE Signal Process Lett 17:731–734
Yu C, Li J, Li X, Ren X, Gupta BB (2018) Four-image encryption scheme based on quaternion Fresnel transform, chaos and computer generated hologram. Multimed Tools Appl 77:4585–4608
Zhang LY, Wong K-W, Zhang Y, Zhou J (2016) Bi-level protected compressive sampling. IEEE Trans Multimed 18:1720–1732
Zhang Y, Zhang LEOYU, Zhou J, Liu L, Chen FEI, He X (2016) A review of compressive sensing in information security field. 2507–2519
Zhou N, Zhang A, Wu J, Pei D, Yang Y (2014) Optik novel hybrid image compression – encryption algorithm based on compressive sensing. Opt - Int J Light Electron Opt 125:5075–5080
Zhou Y, Hua Z, Pun C-M, Chen CLP (2015) Cascade chaotic system with applications. IEEE Trans Cybern 45:2001–2012
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Ponuma, R., Amutha, R. Encryption of image data using compressive sensing and chaotic system. Multimed Tools Appl 78, 11857–11881 (2019). https://doi.org/10.1007/s11042-018-6745-3
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-018-6745-3