Abstract
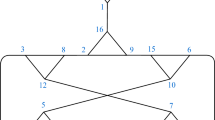
Substitution boxes with resilient cryptographic possessions are normally utilized in block ciphers to give the substantial property of nonlinearity. They are important to resist standard attacks such as linear and differential cryptanalysis. A cryptographically robust S-box must be sound with respect to cryptographic properties like nonlinearity, bit independent criteria, strict avalanche criteria, linear and differential approximation probability. In this paper, we have developed an innovative construction scheme of nonlinear component of block cipher based on the action of projective linear groups on the projective line, and the permutation triangle groups. This nonlinear component, namely S-box, is responsible for making the relation between plaintext and ciphertext intractable which is one of the most important requirements of any modern block ciphers. By widening the scope of the proposed S-boxes, we have applied these lightweight nonlinear components in watermarking scheme.



Similar content being viewed by others
References
Bahrami S, Naderi M (2012) Image encryption using a lightweight stream encryption algorithm. Advances in Multimedia 2012:1–8
Batool SI, Shah T, Khan M (2014) A color image watermarking scheme based on affine transformation and S4 permutation. Neural comput applic, Springer 25:2037–2045
Baumslag G, Fine B, Xu X (2006) Cryptosystems using linear groups. AAECC 17(3–4):205–217
Belazi A, Khan M, Abd El-Latif AA, Belghith S (2017) Efficient cryptosystem approaches: S-boxes and permutation substitution-based encryption. Nonlinear Dyn 87:337–361
Bogdanov A, Knudsen LR, Leander G, Paar C, Poschmann A, Robshaw MJB, Seurin Y, Vikkelsoe C (2007) PRESENT: an ultra-lightweight block cipher. In: Paillier P, Verbauwhede I (eds) The 9th international workshop on cryptographic hardware and embedded systems - CHES 2007, LNCS 4727. Springer, Berlin, pp 450–466
Chawla G, Kamaldeep RS, Yadav R (2012) Classification of watermarking based upon various parameters. Int J Comput Appl Inf Technol 1:16–19
Cid C, Murphy S, Robshaw MJB (2005) Small scale variants of the AES, Proceedings of FSE 2005, LNCS, 145–162. Springer
Conder M, Havas G, Newman MF. On one-relator quotients of the modular group, (preprint)
Conder M (1987) Three-relator quotients of the modular group. Q J Math 38 (4):427–447
El-Sheikh HM, El-Mohsen OA, Elgarf T, Zekry A (2012) A new approach for designing key-dependent S-Box defined over G F(24) in AES. Int J Comput Theory Eng 4(2):158–164
Everitt B (2000) Alternating quotients of Fuchsian groups. J Algebra 223:457–476
Gangadaril BR, Ahamed SR (2015) Analysis and algebraic construction of S-Box for AES algorithm using Irreducible Polynomials. In: 2015 8th international conference on contemporary computing (IC3). Noida0, pp 526–530
Higman G, Mushtaq Q (1983) Coset diagrams and relations for P S L(2,z). Arab Gulf J Scient Res 1:159–164
Isa H, Jamil N, Z’aba MR (2016) Construction of cryptographically strong S-Boxes inspired by bee waggle dance. New Generation Computing 34:221–238
Khan M (2015) A novel image encryption scheme based on multi-parameters chaotic S-boxes. Nonlinear Dyn 82:527–533
Khan M, Shah T (2015) An efficient construction of substitution box with fractional chaotic system. SIViP 9:1335–1338
Khan M, Shah T (2015) A copyright protection using watermarking scheme based on nonlinear permutation and its quality metrics. Neural Comput Applic 26:845–855
Khan M, Shah T, Batool SI (2016) A new implementations of chaotic S-boxes in CAPTCHA. SIViP 10:293–300
Khan M, Shah T (2016) Construction and applications of chaotic S-boxes in image encryption. Neural Comput Applic 27:677–685
Khan M., Asghar Z. (2018) A novel construction of substitution box for image encryption applications with Gingerbreadman chaotic map and S8 permutation. Neural Comput Applic 29:993–99
Matsui M (1994) Linear cryptanalysis method for DES cipher, LNCS 765, Eurocrypt’93, pp 386–397
Meier W, Staffelbach O (1990) Nonlinear criteria for cryptographic functions. In: Quisquater JJ, Vandewalle J (eds) Lecture Notes in Computer Science and Advances in Cryptology, EUROCRYPT 89, vol 434. Springer, Berlin, pp 549–562
Mihajloska H, Gligoroski D (2012) Construction of optimal 4-bit S-boxes by Quasigroups of order 4. In: The 6th international conference on emerging security information, systems and technologies, SECURWARE 2012, Rome, Italy
Mushtaq Q, Shaheen F (1987) Coset diagrams for a homomorphic image of △(2, 3, 6). Ars Combinatoria A 23:187–193
Mushtaq Q (1988) Modular group acting on real quadratic fields. Bull Austral Math Soc 37:303–309
Mushtaq Q (1990) Coset diagrams for Hurwitz groups. Comm Algebra 18 (11):3857–3888
Mushtaq Q (1992) Parametrisation of all homomorphisms from \(PGL(2,\mathbb {Z})\) into P G L(2,q). Comm Algebra 20(4):1023–1040
Nakahara J Jr, de Freitas DS (2009) Mini-ciphers: a reliable testbed for cryptanalysis?, “symmetric cryptography”, seminar 09031. In: Dagstuhl S (ed) Dagstuhl Seminar Proceedings. Leibniz-Zentrum fuer Informatik, Germany, pp 1862–4405
Phan RC-W (2002) Mini advanced encryption standard (Mini-AES): A testbed for cryptanalysis students. Cryptologia XXVI(4):283–306
Pieprzyk J, Finkelstein G (1988) Towards effective nonlinear cryptosystem design. IEE proceedings 135, part E(6):325–335
Shannon C (1949) Communication theory of security systems. Bell Systems Technical Journal 28(4):656–715
Siegenthaler T (1985) Decrypting a class of stream ciphers using Ciphertexts only. IEEE Trans Computer C34:81–85
Singh AK, Kumar B, Singh G, Mohan A (2017) Medical image watermarking: Techniques and applications, Springer
Steinwandt R (2001) Loopholes in two public key cryptosystems using the modular group, International workshop on public key cryptography, pp 180–189
Tom MA (1976) Modular functions and Dirichlet series in number theory, 2nd edn. Springer, New York
Wang Z, Bovik AC (2002) A universal image quality index. IEEE Signal Process Lett 9(3):81–84
Wilson JS (1999) Simple images of triangle groups. Quart Jour Math Ser 50:523–531
Yamamura A (1998) Public-key cryptosystems using the modular group, public key cryptography. In: 1st international workshop on practice and theory in public key cryptography, lecture notes in computer science, vol 1431. Springer, Berlin, pp 203–216
Yamamura A (1999) A functional cryptosystem using a group action, information security and privacy. In: 4th australasian conference, lecture notes in computer science, vol 1587. Springer, Berlin, pp 314–325
Acknowledgements
The authors would like to thank the anonymous referees for their helpful comments and suggestions, which improved significantly the presentation of the paper. The authors are thankful to the Higher Education Commission (HEC) of Pakistan for the financial support under-vide No. 21-1743/SRGP/R&D/HEC/2017.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Rafiq, A., Khan, M. Construction of new S-boxes based on triangle groups and its applications in copyright protection. Multimed Tools Appl 78, 15527–15544 (2019). https://doi.org/10.1007/s11042-018-6953-x
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-018-6953-x