Abstract
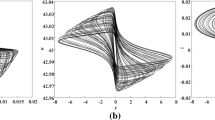
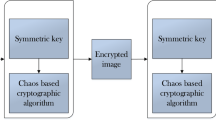
To take into account the invisibility, recovery quality, detection ability, and security, a new digital image fragile watermarking method based on block truncation coding (BTC) and quantum chaos map is proposed. In this method generates the authentication watermark for each 4 × 4 block and generates the recovery watermark for each 2 × 2 block by block truncation coding. For each block, the block truncation coding is used to classify the image blocks into smooth blocks and rough blocks. For different blocks, recovery data can be generated by allocating fewer bits to the smooth blocks and more bits to the rough blocks to encoding the block content. Quantum chaos map is used to generate the block mapping sequence for embedding recovery watermark to improve the shortcoming of watermarking such as small keyspace and low security. The experimental results show that the proposed scheme improves the quality of watermarked and recovered images. Additionally, this approach achieves higher security than the existing methods, under different attacks, such as general tampering, collage attack, content-only, and a hybrid attack.


























Similar content being viewed by others
References
Behnia S, Ayubi P, Soltanpoor W. (2012). Image encryption based on quantum chaotic map and FSM transforms. Proc. Telecommunications Network Strategy and Planning Symposium (NETWORKS), 2012 XVth International, 2012:1-6.
Benrhouma O, Hermassi H, Belghith S (2015) Tamper detection and self-recovery scheme by DWT watermarking. Nonlinear Dynamics 79:1817–1833
Betancourth GP. (2012). Fragile watermarking scheme for image authentication. Proc. Human System Interactions (HSI), 2012 5th International Conference, 2012:168-74.
Chang C-C, Hu Y-S, Lu T-C (2006) Watermarking-based image ownership and tampering authentication scheme. Pattern Recogn Lett 27:439–446
Dadkhah S, Manaf AA, Hori Y, Hassanien AE, Sadeghi S (2014) An effective SVD-based image tampering detection and self-recovery using active watermarking. Signal Process Image Commun 29:1197–1210
Delp EJ, Mitchell OR (1979) Image compression using block truncation coding. IEEE Trans Commun 27:1335–1342
Edupuganti VG, Shih FY, Chang I-C (2011) An efficient block-based fragile watermarking system for tamper localization and recovery. Intelligent Automation & Soft Computing 17:257–267
Fridrich, J. (1999). Protection of digital images using self-embedding. Proc. Symposium on Content Security and Data Hiding in Digital Media, Institute of Technology, New Jersey, USA.
Fridrich J, Goljan M (1999) Images with self-correcting capabilities. Proc international conference on image processing 1999(3):792–796
Fridrich JJ, Goljan M, Memon ND (2002) Cryptanalysis of the Yeung-Mintzer fragile watermarking technique. Journal of Electronic Imaging 11:262–274
Haouzia A, Noumeir R (2008) Methods for image authentication: a survey. Multimed Tools Appl 39:1–46
H-b Z, Yang C (2004) Tamper detection and self-recovery of images using self-embedding. Acta Electron Sin 32:196–199
He H-J, Zhang J-S, Chen F (2009) Adjacent-block based statistical detection method for self-embedding watermarking techniques. Signal Process 89:1557–1566
He H, Zhang J, Tai H (2009) Self-recovery fragile watermarking using block-neighborhood tampering characterization. Proc information hiding 2009:132–145
Hemida O, Huo Y, Chen F, He H. (2017). Block-DCT based alterable-coding restorable fragile watermarking scheme with superior localization. Proc. Asia-Pacific Signal and Information Processing Association Annual Summit and Conference (APSIPA ASC), IEEE,2017, 2017:846-51.
Hemida O, Huo Y, He H, Chen F (2018) A restorable fragile watermarking scheme with superior localization for both natural and text images. Multimed Tools Appl
Huo Y, Chen F, He H, Yin Z. (2010). An alterable-capacity authentication watermarking algorithm with superior localization. Proc. Information Theory and Information Security (ICITIS), 2010 IEEE International Conference, 2010:608-11.
Lee T-Y, Lin SD (2008) Dual watermark for image tamper detection and recovery. Pattern Recogn 41:3497–3506
Li C-T (2004) Digital fragile watermarking scheme for authentication of JPEG images. IEE proceedings-vision, image and signal processing 151:460–466
Lin P-L, Huang P-W, Peng A-W. (2004) A fragile watermarking scheme for image authentication with localization and recovery. Proc. Multimedia Software Engineering, 2004. Proceedings. IEEE Sixth International Symposium on, 146-53.
Liu Z, Zhang F, Wang J, Wang H, Huang J (2016) Authentication and recovery algorithm for speech signal based on digital watermarking. Signal Process 123:157–166
Nyeem H, Boles W, Boyd C (2016) Modeling attacks on self-authentication watermarking. Multimed Tools Appl 75:15849–15880
Piper A, Safavi-Naini R (2013) Scalable fragile watermarking for image authentication. IET Inf Secur 7:300–311
Qian Z, Feng G, Zhang X, Wang S (2011) Image self-embedding with high-quality restoration capability. Digital Signal Processing 21:278–286
Qin C, Chang C-C, Chen P-Y (2012) Self-embedding fragile watermarking with restoration capability based on an adaptive bit allocation mechanism. Signal Process 92:1137–1150
Qin C, Wang H, Zhang X, Sun X (2016) Self-embedding fragile watermarking based on reference-data interleaving and adaptive selection of embedding mode. Inf Sci 373:233–250
Shi H, Wang XH, Li MC, Bai J, Feng B (2017) Secure variable-capacity self-recovery watermarking scheme. Multimed Tools Appl 76:6941–6972
Singh P, Agarwal S (2016) An efficient fragile watermarking scheme with multilevel tamper detection and recovery based on dynamic domain selection. Multimed Tools Appl 75:8165–8194
Singh D, Singh SK (2016) Effective self-embedding watermarking scheme for image tampered detection and localization with recovery capability. J Vis Commun Image Represent 38:775–789
Singh D, Singh SK. (2017). Block Truncation Coding based effective watermarking scheme for image authentication with recovery capability. Multimedia Tools and Applications:1–19.
Singh D, Singh SK (2017) DCT based efficient fragile watermarking scheme for image authentication and restoration. Multimed Tools Appl 76:953–977
Sreenivas K, Prasad VK (2018) Fragile watermarking schemes for image authentication: a survey. Int J Mach Learn Cybern 9:1193–1218
Stinson DR (2005) Cryptography: theory and practice. CRC press
Wang Z, Bovik AC, Sheikh HR, Simoncelli EP (2004) Image quality assessment: from error visibility to structural similarity. IEEE Trans Image Process 13:600–612
Wei L, Chia-Chen L, Jeng-Shyang P. (2016). Novel image authentication scheme with fine image quality for BTC-based compressed images. Multimedia Tools and Applications75:4771–4793.
Yang C-W, Shen J-J (2010) Recover the tampered image based on VQ indexing. Signal Process 90:331–343
Zain JM, Fauzi AR. (2006). Medical image watermarking with tamper detection and recovery. Proc. Engineering in Medicine and Biology Society, 2006. EMBS'06. 28th Annual International Conference of the IEEE, 2006:3270-3.
Acknowledgments
This work is supported by National Natural Science Foundation of China (NSFC) Under grants (61872303) and Technology Innovation Talent Program of Science & Technology Department of Sichuan Province(2018RZ0143).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Hemida, O., He, H. A self-recovery watermarking scheme based on block truncation coding and quantum chaos map. Multimed Tools Appl 79, 18695–18725 (2020). https://doi.org/10.1007/s11042-020-08727-7
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-020-08727-7