Abstract
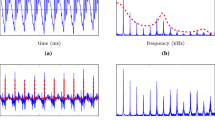
New hybrid cryptosystems represent a highly effective method for increasing security levels of Voice over Internet Protocol (VoIP) systems. In this paper, a dual-security cryptosystem for VoIP voicemail is proposed based on two-factor authentication, followed by Baker Map and RC6 encryption. Two security system models are proposed: the first involves biometric voiceprint encryption with pin code, and the second involves dual-biometric encryption via voiceprint with fingerprint. Parameters were selected to assess the proposed security systems for both quality of function and real-life practicality. An experiment was conducted with a true VoIP call manager, VoIP terminals and fingerprint reader. In addition, Visual Basic and MATLAB were utilized for development and testing of the new cryptosystems. Behind this orthogonal frequency division multiplexing (OFDM) simulation system was developed to ensure efficiency with different signal-to-noise ratio (SNR). Comparative analysis among both encryption methods determined that the first scenario is more cost-effective than the second owing to the lack of fingerprint-reading device, but the second is more secure due to combined biometric print requirements.
A comparison with techniques used by other, recently developed voice cryptosystems demonstrated lower correlation coefficient (25% improvement) and encryption processing time by the presented hybrid cryptosystem. Collectively, this paper presents a VoIP system with high security and immunity vis-à-vis image encryption noise.





Similar content being viewed by others
References
Aissa B, Khaled M, Mohamed L (2015) Speech encryption using stream cipher. Br J Appl Sci Technol 8(1):107–125
Albin C, Narayan D, Varu R, Thanikaiselvan V (2018) DWT based audio encryption scheme. In: International Conference of Electronics, Communication and Aerospace Technology (ICECA) Conference – IEEE Xplore, pp 29–31
Aleksandr O, Sergey B (2018) Multi-factor authentication: a survey. Cryptography, pp 1–31
Augustine N, George SN, Pattathil DP (2015) An audio encryption technique through compressive sensing and Arnold transform. Int J Trust Manag Comput Commun 3(1):74–92
Dharavath K, Talukdar FA, Laskar RH (2013) Study on biometric authentication system, challenges and future trends. In: A review in International Conference on Computational Intelligence and Computing Research (ICCIC). IEEE, Enathi
Eldin SMS, Khamis SA, Hassanin AAIM, Alsharqawy MA (2014) New audio encryption package for TV cloud computing. Int J Speech Technol 18(1):131–142
El-Fishawy N, Abu Zaid OM (2007) Quality of encryption measurement of bitmap images with RC6, MRC6, and Rijndael Block cipher algorithms. Int J Netw Secur 5(3):241–251
Elsayed M, Farag Allah EOS (2015) Efficient audio cryptosystem based on chaotic maps and double random phase encoding. Int J Speech Technol, Springer 18(4):13–15
Elshamy AM, Ahmed N, Abd E-NA, Osama S, Yi M, Saleh A, Fathi E (2013) Optical image encryption based on chaotic baker map and double random phase encoding. Light Wave Technol J-IEEE 31(15):2533–2539
Elshamy AM, Fathi E, El-Samie A, Osama S, Faragallah E, Elshamy M, El-sayed HS, El-zoghdy SF, Rashed ANZ, Abd El-Naser A, Alhamad AQ (2016) Optical image cryptosystem using double random phase encoding and Arnold’s cat map. Springer J 48(3):1–18
Fujii H, Tsuruoka Y (2013) SV-2FA: Two-factor user authentication with sms and voiceprint challenge response. In: 8th International Conference for Internet Technology and Secured Transactions (ICITST), Dec. 9–12, 2013. IEEE, London
Fyyaz Y, Mohammad D (2016) The evaluation of voice-over internet protocol (VoIP) by means of Trixbox. Int J Nat Eng Sci 10(3):33–41
Ghasemzadeh A, Esmaeili E (2017) Anovel method in audio message encryption based on a mixture of chaos function. Int J Speech Technol 20(4):829–837
Honglei Y, Guang-shou W, Ting W, Diantao L, Jun Y, Weitao M, Shaolei FY, Yuankao M (2009) An image encryption algorithm based on two dimensional baker map. In: Proc. International Conference on Intelligent Computation Technology and Automation ICICTA. IEEE, Changsha, pp 536–540
Kakaei KH, Jafar R, Ayaz I (2018) A novel fast and secure approach for voice encryption based on DNA computing. In: 3D Research Center. Kwangwoon University and Springer-Verlag, GmbH Germany
Kataria AN, Adhyaru DM, Sharma AK, Zaveri TH (2013) A survey of Automated Biometric Authentication Techniques. In: Engenerring (NUiCONE), Nirma University Conference. IEEE, Ahmedabad
Khanapur NH, Patro A (2015) Design and implementation of enhanced version of MRC6 algorithm for data security. Int J Adv Comput Res 5(19):225–232
Li RDY (2014) Application of compound chaotic mapping in voice encryption algorithm. International Journal of Computer Science and Network Security (IJCSNS) 14(8):44
Li P, Zhang R, Li H (2019) A research on transmission performance of MIMO-OFDM Wireless Channel. In: Signal Processing, and Systems Springer, International Conference in Communications, pp 308–316
Lima JB, Da Silva Neto EF (2016) Audio encryption based on the cosine number transform. Multimed Tools Appl 75(14):8403–8418
Liu H, Kadir A, Li Y (2016) Audio encryption scheme by confusion and diffusion based on multi-scroll chaotic system and one time keys. Optik 127(19):7431–7438
Maher K, Al-Azawi M, Gaze AM (2018) Combined speech compression and encryption using chaotic compressive sensing with large key size. IET Signal Process 12:214–218
Padmanabhan M, Saon G, Huang J, Kingsbury B, Mangu L (2002) Automatic speech recognition performance on a voicemail transcription task. IEEE Trans Speech Audio Process 10(7):433–442
Ramesh S, Milind N (2018) Audio encryption algorithm using modified elliptical curve cryptography and Arnold transform for audio watermarking. In: I2CT - IEEE Xplore, Pune, pp 1–4
Rohloff K, Cousins DB, Sumorok D (2017) Scalable, practical VoIP teleconferencing with end-to-end Homomorphic encryption. IEEE Trans Inf Forensic Secur 12:1031–1041
Sathiyamurthi P, Ramakrishnan S (2017) Speech encryption using chaotic shift keying for secured speech communication. Eurasip J Audio Speech Music Process 20(2017). https://doi.org/10.1186/s13636-017-0118-0
Sinha K, Darshani MP, Kumari S (2017) Enhanced, efficient end-to-end voice encryption using A5/3RC6 over GSM network. Imperial Journal of Interdisciplinary Research (IJIR) 3(1):1981–1984
Tamimi AA, Abdalla AM (2014) An audio shuffleencryption algorithm. In: The world congress on engineering and computer science. WCECS, San Francisco
Wickramanayake DK, Brayant M (2011) Utilizing an Opensource VolP solution to replace traditional PBX systems at UTech. Paper presented at the IEEE Computer. Society-Jamaica Section Technical Session, Kingston, Jamaica
Xingyuan Wang A, Yining Su B (2019) An audio encryption algorithm based on DNA coding and chaotic system. IEEE Access 8:9260–9270
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Elshamy, E.M., Hussein, A.I., Hamed, H.F.A. et al. Voice over internet protocol voicemail security system using two factor authentication and biometric prints with new efficient hybrid cryptosystem. Multimed Tools Appl 80, 9877–9893 (2021). https://doi.org/10.1007/s11042-020-09986-0
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-020-09986-0