Abstract
Chaotic systems are widely used in various fields, but under the finite precision device, chaotic systems would fall into a cycle and subsequently the performance degrade. Thus, the suppression method of the dynamic degradation of digital chaos is receiving increasing attention. This paper proposes a new improvement model to suppress the dynamical degradation under finite computing accuracy equipment. By using the difference between two maps of the same type but with different initial values, and the state feedback function to improve the performance of the digital chaotic map and extend the time before the chaotic map enters the cycle. Take the 1D Logistic map and x-dimensional of Baker map as examples to prove the effectiveness of the improvement model. Then we proposed a new key selection method, in what part of information of the image would be selected by using a chaotic map to generate a special value. The special value would be used as part of the key. Based this method, a new image encryption algorithm was proposed. The information entropy of the image encrypted by our encryption algorithm is 7.9972, the NPCR and UACI are 0.996095 and 0.334635, respectively, what both are very close to ideal values. The experimental simulation results show that the image encryption scheme exhibits good performances and high security and effectively resists various attacks.



























Similar content being viewed by others
References
Abdulla AA (2015) Exploiting similarities between secret and cover images for improved embedding efficiency and security in digital steganography [D]. University of Buckingham
Adbulla AA, Sellahewa H, Jassim SA (2014) Stego quality enhancement by message size reduction and Fibonacci bit-plane mapping [C]. Security Standardisation Research, SSR 8893:151–166
Anand A, Raj A, Kohli R, Bibhu V (2016) Proposed symmetric key cryptography algorithm for data security. 2016 International Conference on Innovation and Challenges in Cyber Security (ICICCS-INBUSH), Noida, 159–162.
Bandt C, Pompe B (2002) Permutation entropy: a natural complexity measure for time series [J]. Phys Rev Lett 88(17):174102
Beiazi A, El-Latif AAA, Diaconu AV, Rhouma R, Belghith S (2017) Chaos-based partial image encryption scheme based on linear fractional and lifting wavelet transforms [J]. Opt Lasers Eng 88:37–50
Ben Farah MA, Guesmi R, Kachouri A et al (2020) A new design of cryptosystem based on S-box and chaotic permutation [J]. Multimed Tools Appl 79(27–28):19129–19150
Ben ZH, Min LS, Min G, et al. (2016) Chaotic image encryption & image sharing algorithm research based on wavelet transform and CRT [C].2016 13th International Computer Conference on Wavelet Active Media Technology and Information Processing (ICCWAMTIP), International Computer Conference on Wavelet Active Media Technology and Information Processing: 28–32
Bocheng L, Hongyue X, Lingfeng L (2020) Reducing the dynamical degradation of digital chaotic maps with time-delay linear feedback and parameter perturbation [J]. Math Probl Eng 2020(2):1–12
Chen Chen, Sun Kehui, He Shaobo. An improved image encryption algorithm with finite computing Precision [J]. Signal Process, 2019, 168, 107340.
ChengQing L, Lin DD, BingBing F et al (2018) Cryptanalysis of a chaotic image encryption algorithm based on information entropy [J]. IEEE Access 6:75834–75842
Chyun-Chau F, Wang M-C (2011) A combined input-state feedback linearization scheme and independent component analysis filter for the control of chaotic systems with significant measurement noise [J]. J Vib Control 17(2):215–221
Flores-Vergara A, Inzunza-Gonzalez E, Garcia-Guerrero EE et al (2019) Implementing a chaotic cryptosystem by performing parallel computing on embedded systems with multiprocessors [J]. Entropy 21(3):268
Guodong Y, Pan C, Xiaoling H et al (2018) An efficient pixel-level chaotic image encryption algorithm [J]. Nonlinear Dyn 94(1):745–756
Ismail SM, Said LA, Radwan AG, Madian AH, Abu-Elyazeed MF (2018) Generalized double-humped logistic map-based medical image encryption [J]. J Adv Res 10:85–98
Khlebodarova TM, Kogai VV, Fadeev SI, Likhosvai VA (2017) Chaos and hyperchaos in simple gene network with negative feedback and time delays [J]. J Bioinforma Comput Biol 15(2):1650042
Kohli R, Kumar M (2013) FPGA implementation of cryptographic algorithms using multi-encryption technique [J]. Computer Science
Lingfeng L, Suoxia M (2017) Delay-introducing method to improve the dynamical degradation of a digital chaotic map [J]. Inf Sci 396:1–13
Lingfeng L, Lin J, Suoxia M et al (2017) A double perturbation method for reducing dynamical degradation of the digital baker map [J]. Int J Bifurcation Chaos 27(7):14750103
Lingfeng L, Bocheng L, Hu H et al (2018) Reducing the dynamical degradation by bi-coupling digital chaotic maps [J]. Int J Bifurcation Chaos 28(5):1850059
Lingfeng L, Shidi H, Lin J et al (2018) Image block encryption algorithm based on chaotic maps [J]. IET Signal Process 12(1):22–30
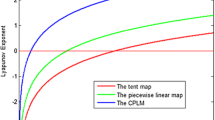
Lv-Chen C, Luo Y-L, Sen-Hui Q, Jun-Xiu L (2015) A perturbation method to the tent map based on Lyapunov exponent and its application [J]. Chinese Physics B 24(10):100501
Mondal B, Mandal T (2017) A light weight secure image encryption scheme based on chaos & DNA computing [N]. J King Saud Univ – Comput Inform Sci 29(4):499–504
Nagaraj N, Shastry MC, Vaidya PG (2008) Increasing average period lengths by switching of robust chaos maps infinite precision [J]. European Phys J Special Topics 165:73–83
Nan J, Dong X, Hu H et al (2019) Quantum image encryption based on Henon mapping [J]. Int J Theor Phys 58(3):979–991
Niyat AY, Moattar MH, Torshiz MN (2017) Color image encryption based on hybrid hyper-chaotic system and cellular automata [J]. Opt Lasers Eng 90:225–237
Parvaz R, Zarebnia M (2018) A combination chaotic system and application in color image encryption [J]. Opt Laser Technol 101:30–41
Pator KAK, Acharya B, Nath V (2019) A secure multi-stage one-round bit-plane permutation operation based chaotic image encryption [J]. Microsyst Technol Micro Nanosyst -Inf Storage Process Syst 25(6):2331–2338
Pincus S (1995) Approximate entropy (APEN) as a complexity measure [J]. Chaos 5(1):110–117
Preishuber M, Hutter T, Katzenbeisser S, Uhl A (2018) Depreciating motivation and empirical security analysis of Chaos-based image and video encryption [J]. IEEE Trans Inform Foren Secur 13(9):2137–2150
Souyah A, Faraoun KM (2016) Fast and efficient randomized encryption scheme for digital images based on Quadtree decomposition and reversible memory cellular automata [J]. Nonlinear Dyn 84(2):715–732
Wheeler DD, Matthews RAJ (1991) Supercomputer investigations of a chaotic encryption algorithm [J]. Cryptologia 15(2):140–152
Wu XJ, Wang KS, Wang X, Kan H, Kurths J (2018) Color image DNA encryption using NCA map-based CML and one-time keys [J]. Signal Process 148:272–287
Xiaojun T, Wang Z, Miao Z et al (2015) An image encryption algorithm based on the perturbed high-dimensional chaotic map [J]. Nonlinear Dyn 80(3):1493–1508
Xiao-Jun T, Miao Z, Wang Z, Yang L (2014) A image encryption scheme based on dynamical perturbation and linear feedback shift register [J]. Nonlinear Dyn 78(3):2277–2291
Yueping L, Wang C, Hua C (2017) A hyper-chaos-based image encryption algorithm using pixel-level permutation and bit-level permutation [J]. Opt Lasers Eng 90:238–246
Yunqi L, Luo Y, Shuxiang S et al (2017) Counteracting dynamical degradation of digital chaotic Chebyshev map via perturbation [J]. Int J Bifurcation Chaos 27(3):1750033
Zenggang X, Wu Y, Conghuan Y et al (2019) Color image chaos encryption algorithm combining CRC and nine palace map [J]. Multimed Tools Appl 78(22):31035–31055
Zhongyun H, Yicong Z, Chi-man P et al (2015) 2D sine logistic modulation map for image encryption [J]. Inf Sci 297:80–94
Zhongyun H, Fan J, Xu B et al (2018) 2D logistic-sine-coupling map for image encryption [J]. Signal Process 149:148–161
Zhongyun H, Yicong Z, Hejiao H (2019) Cosine-transform-based chaotic system for image encryption [J]. Inf Sci 480:403–419
Acknowledgements
This work is supported by the National Natural Science Foundation of China (61862042); Innovation Special Fund Designated for Graduate Students of Jiangxi Province (YC2019-S101).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Xiang, H., Liu, L. A novel image encryption algorithm based on improved key selection and digital chaotic map. Multimed Tools Appl 80, 22135–22162 (2021). https://doi.org/10.1007/s11042-021-10807-1
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-021-10807-1