Abstract
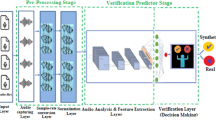
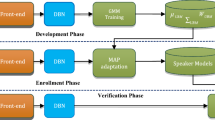
The current speech content authentication process directly constructs the extracted biometrics into a binary hashing sequence and stores them in the cloud for hashing matching, so the authentication process is vulnerable to similarity attacks, which may lead to the disclosure of biometrics and hash sequences. In order to solve the above problem, this paper proposes an algorithm that is speech BioHashing security authentication algorithm based on CNN hyperchaotic map. Firstly, the user terminal conducts on linear prediction coefficients (LPC) analysis for the pre-processed speech signal, then extracts the improved Mel frequency cepstral coefficients (MFCC) features to obtains the new feature parameter, and calculates the Euclidean distance of the parameter as the biometric vector. Then, the biometrics and the orthogonal set matrix which is constructed by the improved random Fourier measurement matrix are inner product to form biosafety templates, and the templates are further quantified into BioHashing sequences. Finally, the BioHashing sequences are encrypted by CNN hyperchaotic map encryption algorithm and upload them to the cloud server. The experimental results show that the biosafety template not only provides the safe template for the biometric, but also the encryption algorithm of CNN hyperchaotic map guarantees the safety of the BioHashing sequence. At the same time, the algorithm has better robustness and discrimination, and tamper detection and location can better detect and locate mute attacks and substitution attacks.
























Similar content being viewed by others
References
Ajish S, Anil KKS (2020) Security and performance enhancement of fingerprint biometric template using symmetric hashing. Comput Secur 90:101714
Bedad F, Réda A (2018) Multi-biometric template protection: an overview. In: International Conference in Artificial Intelligence in Renewable Energetic Systems. Springer, pp 70–79
Chang D, Garg S, Hasan M, Sweta M (2020) Cancelable multi-biometric approach using fuzzy extractor and novel bit-wise encryption. IEEE Trans Inf Forensic Secur 15:3152–3167
Chen Y, Wo Y, Xie R, Wu C, Guoqiang H (2019) Deep secure quantization: On secure biometric hashing against similarity-based attacks. Signal Process 154:314–323
Deng M, Meng T, Cao J, Wang S, Zhang J, Huijie F (2020) Heart sound classification based on improved mfcc features and convolutional recurrent neural networks. Neural Netw 130:22–32
Dong X, Jin Z, Beng J A T (2019) A genetic algorithm enabled similarity-based attack on cancellable biometrics. In: 2019 IEEE 10th International Conference on Biometrics Theory, Applications and Systems (BTAS). IEEE, pp 1–8
Feng Y C, Lim M-H, Yuen Pong C (2014) Masquerade attack on transform-based binary-template protection based on perceptron learning. Pattern Recogn 47(9):3019–3033
Hua Z, Zhang Y, Yicong Z (2020) Two-dimensional modular chaotification system for improving chaos complexity. IEEE Trans Signal Process 68:1937–1949
Hua Z, Zhu Z, Chen Y, Yuanman L (2021) Color image encryption using orthogonal latin squares and a new 2d chaotic system. Nonlinear Dyn:1–18
Jiang Y, Wu C, Deng K, Yan W (2019) An audio fingerprinting extraction algorithm based on lifting wavelet packet and improved optimal-basis selection. Multimed Tools Appl 78(21):30011–30025
Joseph T, Kalaiselvan SA, Aswathy SU, Radhakrishnan R, Shamna AR (2020) A multimodal biometric authentication scheme based on feature fusion for improving security in cloud environment. J Ambient Intell Human Comput:1–9
Kadyan V, Mandeep K (2020) Sgmm-based modeling classifier for punjabi automatic speech recognition system. In: Smart Computing Paradigms: New Progresses and Challenges. Springer, pp 149–155
Kaur H, Pritee K (2018) Random distance method for generating unimodal and multimodal cancelable biometric features. IEEE Trans Inf Forensic Secur 14(3):709–719
Kaur H, Pritee K Privacy preserving remote multi-server biometric authentication using cancelable biometrics and secret sharing. Futur Gener Comput Syst 102:30–41
Kim H-G, Cho H-S, Young K J (2016) Robust audio fingerprinting using peak-pair-based hash of non-repeating foreground audio in a real environment. Clust Comput 19(1):315–323
Krobba A, Debyeche M, Sid-Ahmed S (2020) Mixture linear prediction gammatone cepstral features for robust speaker verification under transmission channel noise. Multimed Tools Appl:1–15
Kumar N, Manisha R (2020) Rp-lpp: a random permutation based locality preserving projection for cancelable biometric recognition. Multimed Tools Appl 79(3):2363–2381
Kumar S R, Bharathi B (2020) A novel approach towards generalization of countermeasure for spoofing attack on asv systems. Circ Syst Signal Process:1–18
Li J, Wang H, Yi J (2015) Audio perceptual hashing based on nmf and mdct coefficients. Chin J Electron 24(3):579–588
Liu N, Gao J, Zhang B, Wang Q, Xiudi J (2019) Self-adaptive generalized s-transform and its application in seismic time–frequency analysis. IEEE Trans Geosci Remote Sens 57(10):7849–7859
Morampudi M K, Prasad MVNK, Raju USN (2020) Privacy-preserving iris authentication using fully homomorphic encryption. Multimed Tools Appl:1–23
Nguyen T A T, Dang T K, Thanh N D (2019) A new biometric template protection using random orthonormal projection and fuzzy commitment. In: International Conference on Ubiquitous Information Management and Communication. Springer, pp 723–733
Olanrewaju L, Oyebiyi O, Misra S, Maskeliunas R, Robertas D (2020) Secure ear biometrics using circular kernel principal component analysis, chebyshev transform hashing and bose–chaudhuri–hocquenghem error-correcting codes. SIViP:1–9
Oo Z, Wang L, Phapatanaburi K, Iwahashi M, Nakagawa S, Jianwu D (2018) Phase and reverberation aware dnn for distant-talking speech enhancement. Multimed Tools Appl 77(14):18865–18880
Oo Z, Wang L, Phapatanaburi K, Liu M, Nakagawa S, Iwahashi M, Jianwu D (2019) Replay attack detection with auditory filter-based relative phase features. EURASIP J Audio Speech Music Process 2019(1):8
Parkavi R, Babu KRC, Neelambika T, Shilpa P (2018) Cancelable biometrics using geometric transformations and bio hashing. In: Computational Vision and Bio Inspired Computing. Springer, pp 652–662
Pawade D, Sakhapara A, Andrade M, Badgujar A, Divya A (2019) Implementation of fingerprint-based authentication system using blockchain. In: Soft Computing and Signal Processing. Springer, pp 233–242
Ponnaian D, Kavitha C (2017) Crypt analysis of an image compression–encryption algorithm and a modified scheme using compressive sensing. Optik 147:263–276
Qiu J, Li H, Chuan Z (2019) Cancelable palmprint templates based on random measurement and noise data for security and privacy-preserving authentication. Comput Secur 82:1–14
Qiuyu Z, Tao Z, Dongfang W, Ge Z (2018) Strong robust speech authentication algorithm based on quasi-harmonic model. J Huazhong Univ Sci Technol (Nat Sci Edn) 28(3):11
Sandhya M, Prasad MVNK (2017) Biometric template protection: A systematic literature review of approaches and modalities. In: Biometric Security and Privacy. Springer, pp 323–370
Sheela SJ, Suresh KV, Tandur D, Sanjay A (2020) Cellular neural network-based medical image encryption. SN Comput Sci 1(6):1–11
Sonnleitner R, Gerhard W (2015) Robust quad-based audio fingerprinting. IEEE/ACM Trans Audio Speech Lang Process 24(3):409–421
Trivedi A K, Thounaojam D M, Shyamosree P (2020) Non-invertible cancellable fingerprint template for fingerprint biometric. Comput Secur 90:101690
Yadav I C, Gayadhar P (2020) Pitch and noise normalized acoustic feature for children’s asr. Digital Signal Process 109:102922
Yang J, Das R K, Haizhou L (2019) Significance of subband features for synthetic speech detection. IEEE Trans Inf Forensic Secur 15:2160–2170
Zhang Q-y, Ge Z-x, Hu Y-j, Bai J, Yi-bo H (2020) An encrypted speech retrieval algorithm based on chirp-z transform and perceptual hashing second feature extraction. Multimed Tools Appl 79(9):6337–6361
Zhang Q-y, Hu W-j, Huang Y-b, Si-bin Q (2018) An efficient perceptual hashing based on improved spectral entropy for speech authentication. Multimed Tools Appl 77(2):1555–1581
Zhang Q-y, Qiao S-b, Huang Y-b, Tao Z (2018) A high-performance speech perceptual hashing authentication algorithm based on discrete wavelet transform and measurement matrix. Multimed Tools Appl 77(16):21653–21669
Zhang Q-Y, Xing P-F, Huang Y-B, Dong R-H, Zhong-Ping Y (2015) An efficient speech perceptual hashing authentication algorithm based on wavelet packet decomposition. J Inf Hiding Multimed Signal Process 6(2):311–322
Zhang Q, Zhang D, Liang Z (2020) An encrypted speech authentication method based on uniform subband spectrum variance and perceptual hashing. Turkish J Electr Eng Comput Sci 28(5):2467–2482
Zhao S, Bob Z (2020) Joint constrained least-square regression with deep convolutional feature for palmprint recognition. IEEE Trans Syst Man Cybern: Syst 15:2160–2170
Acknowledgements
This work is supported by the National Natural Science Foundation of China (No.61862041), Science and Technology Program of Gansu Province of China (No.21JR7RA120).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Huang, Yb., Yuan-Zhang, Chen, TF. et al. Speech BioHashing security authentication algorithm based on CNN hyperchaotic map. Multimed Tools Appl 81, 37953–37979 (2022). https://doi.org/10.1007/s11042-022-12985-y
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-022-12985-y