Abstract
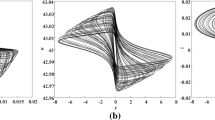
In this paper, we present a novel scheme for enhancing the security of speech information in communication systems. We build a hybridization of three approaches: Chaotic logistic and tent maps for generating an arbitrary vector by some primarily initiated values to be joined in the original speech signal, an integrated watermark image within the encrypted signal in order to verify, through decryption process, that the encrypted signal is authentic as well as does not suffer from eventual attacks, and the third approach is using an Arnold scrambling key (cat map) to spread signal samples by means of a secret key, then recuperate the original signal from samples which is not possible without this key. Obtained correlation value in the proposed scheme is closer to null which proves that original and encrypted signals are completely dissimilar. Moreover, we recovered the original speech without disturbing the quality. Numerical results of the Signal to Noise Ratio (SNR) and Correlation Coefficient (CC) reported below, and the comparison between the proposed approach to seven recently published works, also reported, reveal the superiority of the proposed scheme and validate our design to be considered amongst the best methods compared to other recently existing strong approaches.













Similar content being viewed by others
References
Abdelfatah RI (2020) Audio encryption scheme using self-adaptive bit scrambling and two multi chaotic-based dynamic DNA computations. IEEE Access 8:69894–69907. https://doi.org/10.1109/ACCESS.2020.2987197
Al-Hooti M, Ahmad T, Djanali S (2019) “Developing audio data hiding scheme using random sample bits with logical operators”, Indonesian J Electr Eng Comput Sci. https://doi.org/10.11591/ijeecs.v13.i1.pp147-154.
Dhar PK, Shimamura T (2015) “Advances in Audio Watermarking Based on Singular Value Decomposition”, Springer briefs in electrical and computer engineering. https://doi.org/10.1007/978-3-319-14800-7.
Elsafty AH, Tolba MF, Said LA, Madian AH, Radwan AG (2020) Enhanced hardware implementation of a mixed-order nonlinear chaotic system and speech encryption application. Int J Electron Commun 125:153347. https://doi.org/10.1016/j.aeue.2020.153347
Fantacci R, Menci S, Micciullo L, Pierucci L (2009) A secure radio communication system based on an efficient speech watermarking approach. Security and Communication Networks 2:305–314. https://doi.org/10.1002/sec.70
Farsana FJ, Gopakumar AK (2016) “A Novel Approach for Speech Encryption: Zaslavsky Map as Pseudo Random Number Generator”, 6th International Conference on Advances InComputing& Communications (Procedia Computer Science 2016) https://doi.org/10.1016/j.procs.2016.07.302.
Farsana FJ, Gopakumar K (2020) “Speech Encryption Algorithm Based on Nonorthogonal Quantum State with Hyperchaotic Keystreams”, Hindawi Advances in Mathematical Physics https://doi.org/10.1155/2020/8050934.
Farsana FJ, Devi VR, Gopakumar K (2020) An audio encryption scheme based on fast Walsh Hadamard transform and mixed chaotic keystreams. Appl Comput Inf. https://doi.org/10.1016/j.aci.2019.10.001
Huang CK (2009) H.H. Nien “multi chaotic systems based pixel shuffle for image encryption”. Opt Commun 282:2123–2127. https://doi.org/10.1016/j.optcom.2009.02.044
Joshi Subir Dr Amit M (2016) “DWT-DCT based Blind Audio Watermarking using Arnold Scrambling and Cyclic Codes”, 3rd International Conference on Signal Processing and Integrated Networks. https://doi.org/10.1109/SPIN.2016.7566666.
Jovic B (2011) Chaotic Signals and Their Use in Secure Communications. In: Synchronization Techniques for Chaotic Communication Systems. Signals and Communication Technology. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-21849-1_2
Kaur G,Singh K, Gill HS “Chaos-based joint speech encryption scheme using SHA-1”, Multimedia tools and applications (2021). https://doi.org/10.1007/s11042-020-10223-x.
Khanzadi H, Eshghi M, Borujeni SE (2014) Image encryption using random bit sequence based on chaotic maps. Arab J Sci Eng. https://doi.org/10.1007/s13369-013-0713-z
LalithaCh NV, JayaSree SRPVY (2013) "DWT-Arnold Transform Based Audio Watermarking", IEEE Asia Pacific Conference on Postgraduate Research in Microelectronics and Electronics. https://doi.org/10.1109/PrimeAsia.2013.6731204.
Lima JB, da Silva Neto EF (2015) Audio encryption based on the cosine number transform. Multimedia Tools Appl. https://doi.org/10.1007/s11042-015-2755-6
Lin Y, Abdulla WH, “Audio watermark: a Comprehensive Foundation using MATLAB”, springer Cham (2015). https://doi.org/10.1007/978-3-319-07974-5.
Liu H, Zhao B, Huang L (2019) Quantum image encryption scheme using Arnold transform and S-box scrambling. Entropy. https://doi.org/10.3390/e21040343
Merrad A, Saadi S (2018) Blind speech watermarking using hybrid scheme based on DWT/DCT and sub-sampling. Multimed Tools Appl. https://doi.org/10.1007/s11042-018-5939-z
Merrad A, Saadi S, Benziane A, Hafaifa A (2018) Robust Blind Approach for Digital SpeechWatermarking. In 2nd International Conference on Natural Language and Speech Processing. https://doi.org/10.1109/ICNLSP.2018.8374366.
Mosa E, Messiha N, Zahran O, El-Samie FEAbd (2011) “Chaotic encryption of speech signals”, Int J Speech Technol https://doi.org/10.1007/s10772-011-9103-7.
Nematollahi SAR Al-Haddad (2013) “An overview of digital speech watermarking”. Int JSpeech Technol. https://doi.org/10.1007/s10772-013-9192-6.
Ratner B (2009) The correlation coefficient: its values range between + 1 / − 1, or do they ? J Target Meas Anal Mark 17:139–142. https://doi.org/10.1057/jt.2009.5
Revathi A, Sasikaladevi N, Jeyalakshmi C (2018) Digital speech watermarking to enhance the security using speech as a biometric for person authentication. International Journal of Speech Technology 21:1021–1031. https://doi.org/10.1007/s10772-018-09563-9
Saadi S, Merrad A, Benziane A (2019) Novel secured scheme for blind audio/speech norm-space watermarking by Arnold algorithm. Signal Proc. https://doi.org/10.1016/j.sigpro.2018.08.011
Sathiyamurthi P, Ramakrishnan S (2017) “Speech encryption using chaotic shift keying for secured speech communication”, EURASIP Journal on Audio, Speech, and Music Processing https://doi.org/10.1186/s13636-017-0118-0.
Sathiyamurthi P, Ramakrishnan (2020) “Speech encryption algorithm using FFT and 3D-Lorenz–logistic chaotic map”, Multimed Tools Appl https://doi.org/10.1007/s11042-020-08729-5.
Shah D, Shah T, Ahamad I, Haider MI, Khalid I (2021) A three-dimensional chaotic map and their applications to digital audio security. Multimed Tools Appl. https://doi.org/10.1007/s11042-021-10697-3
Sheu LJ (2011) “A speech encryption using fractional chaotic systems”, Nonlinear Dyn https://doi.org/10.1007/s11071-010-9877-1.
Wangab B, Dong XC (2016) On the novel chaotic secure communication scheme design. Commun Nonlinear Sci Numer Simul 39:108–117. https://doi.org/10.1016/j.cnsns.2016.02.035
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest/Competing interests
no conflicts of interest.
Participants
no other research participants except authors that are all consent.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Ouguissi, H., Saadi, S., Merrad, A. et al. Hybrid scheme for safe speech transmission based on multiple chaotic maps, watermarking and Arnold scrambling algorithm. Multimed Tools Appl 82, 327–346 (2023). https://doi.org/10.1007/s11042-022-13301-4
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-022-13301-4