Abstract
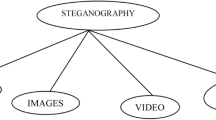
Securing data during transmission is critical to prevent unauthorized access, interception, or modification of the data. Data can be communicated securely while maintaining its confidentiality, integrity, and availability by using cryptographic algorithms and measures. In the proposed work, a hybrid data compression algorithm is proposed to increase the amount of input data that is encrypted using the Advanced Encryption Standard (AES) cryptography method to boost security level, and it can be utilized to carry out the lossy compacting Steganography method. By reducing the quantity of data transmitted, this technique can enable speedy transmission over a sluggish internet connection or use less space on different storage devices. The cover image is compressed using Discrete Wavelet Transform (DWT), which reduces the cover image's dimensions by lossyly compressing the image. The ordinary text is converted to hexadecimal format from text. The encrypted data will then be inserted into the compressed cover picture using the least significant bit (LSB) with Image vector array (IVA). Bits per pixel (BPP), Mean Squared Error (MSE), Peak Signal to Noise Ratio (PSNR), and Structural Similarity Index (SSIM) were some of the metrics we used to evaluate the proposed technique.





Similar content being viewed by others
Data availability
Data sharing not applicable to this article as no datasets were generated or analysed during the current study. No custom algorithm is used.
Abbreviations
- AES:
-
Advanced encryption standard
- DWT:
-
Discrete wavelet transform
- LSB:
-
Least significant bit
- IVA:
-
Image vector array
- DES:
-
Data encryption standard
- ECC:
-
Elliptic curve cryptography
- SSIM:
-
Structural similarity ındex measure
- PSNR:
-
Peak Signal-to-Noise Ratio
- MSE:
-
Mean square error
- BPP:
-
Bits per pixel
- FED:
-
Fuzzy edge detection
- EMD:
-
Exploiting modification direction
- HVS:
-
Human visual system
- DCT:
-
Discrete cosine transform
- BTC:
-
Block truncation coding
- PZMs:
-
Pseudo-Zernike moments
- QKD:
-
Quantum key distribution
- RSA:
-
Rivest–Shamir–Adleman
- PKI:
-
Public key ınfrastructure
- S-box:
-
Substitution box
- RPE:
-
Redundant pattern encoding
- SVD:
-
Singular value decomposition
- 3D DWT:
-
Three-dimensional discrete wavelet transform
- PIM:
-
Processing-In Memory
- AESPIM:
-
Architecture dubbed PIM
- LBP:
-
Local binary pattern
- PPM:
-
Pixel pair matching
- ECC:
-
Elliptic curve cryptography
- PCNG:
-
Pseudo-Chaotic Number Generator
- PRNG:
-
Pseudo-Random Number Generator
- ACRs:
-
Affine covariant regions
- AMBTC:
-
Absolute moment block truncation coding
- ZMs:
-
Zernike moments
References
Dhargupta S, Chakraborty A, Ghosal SK, Saha S, Sarkar R (2019) Fuzzy edge detection based steganography using modifed Gaussian distribution. Multimed Tools Appl. https://doi.org/10.1007/s11042-018-7123-x
Shen SY, Huang LH, Yu SS (2018) A novel adaptive data hiding based on improved EMD and interpolation. Multimed Tools Appl 77:131–141
Saha S, Chakraborty A, Chatterjee A, Dhargupta S, Ghosal SK, Sarkar R (2020) Extended exploiting modifcation direction based steganography using hashed-weightage array. Multimed Tools Appl 79:20973–20993
Chaı X, Haıyang Wu, Gan Z, Zhang Y, Chen Y, Nıxon KW (2020) An efficient visually meaningful image compression and encryption scheme based on compressive sensing and dynamıc Lsb embeddıng. Opt Lasers Eng 124:105837. https://doi.org/10.1016/J.Optlaseng.2019.105837
Kharı M, Garg AK, Gandomı AH, Gupta R, Patan R, Balusamy B (2020) Securıng data ın Internet Of Thıngs (Iot) usıng cryptography and steganography technıques. IEEE Trans Syst Man Cybern Syst 50(1):73–80. https://doi.org/10.1109/Tsmc.2019.2903785
Jeromel A, Žalık B (2020) An efficient lossy cartoon image compression method. Multımed Tools Appl 79:433–451. https://doi.org/10.1007/S11042-019-08126-7
Bhardwaj M, Singh L, Saini KK (2019) An efficient approach to ınformation hiding through ımage steganography using edge detection, 4th International Conference on Information Systems and Computer Networks (ISCON), Mathura, India
Shashi RK, Pavithra G, Manjunath TC (2022) Developing a novel steganography concept of audio data into audio streams. Int Conf Smart Syst Invent Technol (ICSSIT), 229–233. https://doi.org/10.1109/ICSSIT53264.2022.9716566
Li W, Lin CC, Pan JS (2016) Novel image authentication scheme with fine image quality for BTC-based compressed images. Multimed Tools Appl 75:4771–4793. https://doi.org/10.1007/s11042-015-2502-z
Chenthara S, Ahmed K, Wang H, Whittaker F (2019) Security and privacy-preserving challenges of e-health solutions in cloud computing. IEEE Access 7:74361–74382
Ahmed N, Natarajan T, Rao KR (1974) Discrete cosine transform. IEEE Transact Comput C–23(1):90–93. https://doi.org/10.1109/T-C.1974.223784
Bartolini F, Tefas A, Barni M, Pitas I (2001) Image authentication techniques for surveillance applications. IEEE 89(10):1403–1418. https://doi.org/10.1109/5.959338
Ramamurthi B, Gersho A (1986) Nonlinear space-variant postprocessing of block coded images. IEEE Trans Acoust Speech Signal Process 34(5):1258–1268. https://doi.org/10.1109/TASSP.1986.1164961
Xin Y, Liao S, Pawlak M (2007) Circularly orthogonal moments for geometrically robust image watermarking. Pattern Recogn 40:3740–3752. https://doi.org/10.1016/j.patcog.2007.05.004
Gao X, Deng C, Li X, Tao D (2010) Geometric distortion insensitive image watermarking in affine covariant regions. IEEE Trans Syst Man Cybern C 40:278–286. https://doi.org/10.1109/TSMCC.2009.2037512
Haralick R, Sternberg S, Zhuang X (1987) Image analysis using mathematical morphology. Pattern analysis and machine ıntelligence. IEEE Trans Pattern Anal Mach Intell PAMI-9:532–550. https://doi.org/10.1109/TPAMI.1987.4767941
Lema D, Mitchell O (1984) Absolute moment block truncation coding and its application to color images. IEEE Trans Commun 32:1148–1157. https://doi.org/10.1109/TCOM.1984.1095973
Zhang X, Wang S, Qian Z, Feng G (2011) Self-embedding watermark with flexible restoration quality. Multimedia Tools Appl 54:385–395. https://doi.org/10.1007/s11042-010-0541-z
Ravichandran D, Ahamad, M, Dhivakar M (2016) Performance analysis of three-dimensional medical image compression based on discrete wavelet transform. In: 22nd International Conference on Virtual System & Multimedia (VSMM), pp 1–8. https://doi.org/10.1109/VSMM.2016.7863176
ZainEldin H, Elhosseini MA, Ali HA (2015) Image compression algorithms in wireless multimedia sensor networks: a survey. Ain Shams Eng J 6(2):481–490
Thanki RM, Kothari A (2019) Data compression and ıts applicationin medical ımaging. In: Hybrid and advanced compression techniques for medical images, pp 1–15. https://link.springer.com/chapter/10.1007/978-3-030-12575-2_1
Liu Y, Wang L, Qouneh A, Xin Fu (2022) Enabling PIM-based AES encryption for online video streaming. J Syst Architect 132(2022):102734. https://doi.org/10.1016/j.sysarc.2022.102734
Chakraborty S, Jalal AS (2020) A novel local binary pattern based feature image steganography. Multimed Tools Appl 79:19561–19574
Arivazhagan S, Sylvia Lilly Jebarani W, Ananthi Roy S, Amrutha E (2019) Improving quality of stego images through dithering techniques for pixel pair matching steganographic schemes. Int J Eng Adv Technol (IJEAT) 8(6):4923–4931. https://doi.org/10.35940/ijeat.F9239.088619
Amrutha E, ArivazhaganJebarani SWSL (2022) Novel color image steganalysis method based on RGB channel empirical modes to expose stego images with diverse payloads. Pattern Anal Appl 26(1):239–253. https://doi.org/10.1007/s10044-022-01102-2
Duan D, Guo N, Lıu B, Lı MG, Qın C (2020) A new hıgh capacıty ımage steganography method combıned wıth ımage ellıptıc curve cryptography and deep neural network. IEEE Access 8:25777–25788. https://doi.org/10.1109/Access.2020.2971528
Qiao Z, El Assad S, Taralova I (2020) Design of secure cryptosystem based on chaotic components and AES S-Box. AEU – Int J Electron Commun 121:153205. https://doi.org/10.1016/j.aeue.2020.153205
Ajish S, AnilKumar KS (2021) Secure mobile internet voting system using biometric authentication and wavelet based AES. J Inform Secur Appl 61:102908. https://doi.org/10.1016/j.jisa.2021.102908
Bennett C, Brassard G (2020) Quantum cryptography: public key distribution and coin tossing. Theor Comput Sci - TCS 560:175–179. https://doi.org/10.1016/j.tcs.2011.08.039
Grzywak A, Pilch-Kowalczyk G (2009) Quantum cryptography: opportunities and challenges. In: Tkacz E, Kapczynski A (eds) Internet – technical development and applications. Advances in intelligent and soft computing, vol 64. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-05019-0_22
Sari A, Ardiansyah G, Rachmawanto E, Setiadi DRIM (2019) An improved security and message capacity using AES and Huffman coding on image steganography. TELKOMNIKA Indones J Electr Eng 17:2400–2409. https://doi.org/10.12928/TELKOMNIKA.v17i5.9570
Wahab OFA, Khalaf AAM, Hussein AI, Hamed HFA (2021) Hiding data using efficient combination of RSA cryptography, and compression steganography techniques. IEEE Access 9:31805–31815. https://doi.org/10.1109/ACCESS.2021.3060317.F
Sharma N, Batra U (2018) Performance analysis of compression algorithms for information security: a review. ICST Trans Scalable Inf Syst 7(27):163503
Dehshiri M, Sabouri SG, Khorsandi A (2021) Structural similarity assessment of an optical coherence tomographic image enhanced using the wavelet transform technique. J Opt Soc Amer A Opt Image Sci 38(1):1–9
Funding
No funds, grants, or other support was received.
Author information
Authors and Affiliations
Contributions
All authors contributed to the study conception and design. Material preparation, data collection and analysis were performed by Sathananthavathi, Ganesh kumar and Sathish kumar. The first draft of the manuscript was written by Sathananthavathi and all authors commented on previous versions of the manuscript. All authors read and approved the final manuscript.
Corresponding author
Ethics declarations
Conflict of interest
Nil.
Additional information
Publisher's note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Sathananthavathi, V., Ganesh Kumar, K. & Sathish Kumar, M. Secure visual communication with advanced cryptographic and ımage processing techniques. Multimed Tools Appl 83, 45367–45389 (2024). https://doi.org/10.1007/s11042-023-17224-6
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-023-17224-6