Abstract
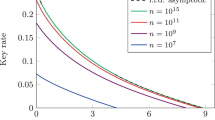
Partial information leakages of generation key undoubtedly influence the security of practical Quantum Key Distribution (QKD) system. In this paper, based on finite-key analysis and deep investigation on privacy amplification, we present a method for characterizing information leakages gained by adversary in each authentication round and therefore take the theory derived by Cederlöf and Larsson (IEEE Trans Inf Theory 54:1735–1741, 2008) into practical case. As the authentication key is fed from one round of generation keys to the next except the first round, by considering its security weakness due to information leakages and finite size effect, we further propose a universal formula for calculating the lifetime of initial authentication key used in QKD with finite resources. Numerical simulations indicate that our bound for estimating information leakages strictly characterizes the stability of practical QKD against information-leakage-based attacks, and our calculation formula in terms of lifetime can precisely evaluate the usage time of initial authentication key. Our work provides a practical solution for evaluating authentication security of QKD.










Similar content being viewed by others
Explore related subjects
Discover the latest articles, news and stories from top researchers in related subjects.References
Bennett, C.H., Brassard, G.: Quantum cryptography: public key distribution and coin tossing. In: Proceedings IEEE International Conference on Computers, Systems and Signal Processing, Bangalore, India, pp. 175–179. IEEE, New York (1984)
Lo, Hoi-Kwong, Chau, H.F.: Unconditional security of quantum key distribution over arbitrarily long distances. Science 283(5410), 2050–2056 (1999)
Shor, W., Preskill, J.: Simple proof of security of the BB84 quantum key distribution protocol. Phys. Rev. Lett. 85, 441–444 (2000)
Renner, R.: Security of quantum key distribution. Int. J. Quantum Inf. 6(1), 1–127 (2008)
Kraus, B., Gisin, N., Renner, R.: Lower and upper bounds on the secret-key rate for quantum key distribution protocols using one-way classical communication. Phys. Rev. Lett. 95(8), 080501 (2005)
Scarani, V., Bechmann-Pasquinucci, H., Cerf, N.J., Dusek, M., Lutkenhaus, N., Peev, M.: The security of practical quantum key distribution. Rev. Mod. Phys. 81(3), 1301–1350 (2009)
Gottesman, D., Lo, H.-K., Lukenhaus, N., Preskill, J.: Security of quantum key distribution with imperfect devices. Quantum Inf. Comput. 4(5), 325–360 (2004)
Lo, H.-K., Ma, X., Chen, K.: Decoy state quantum key distribution. Phys. Rev. Lett. 94(23), 230504 (2005)
Wang, X.-B.: Beating the PNS attack in practical quantum cryptography. Phys. Rev. Lett. 94(23), 230503 (2005)
Cederlöf, J., Larsson, J.-Ä.: Security aspects of the authentication used in quantum cryptography. IEEE Trans. Inf. Theory 54(4), 1735–1741 (2008)
Fung, C.-H.F., Tamaki, K., Qi, B., Lo, H.-K., Ma, X.: Security proof of quantum key distribution with detection efficiency. Quantum Inf. Comput. 9(1–2), 0131–0165 (2009)
Portmann, C.: Key recycling in authentication. arxiv: quant-ph/1202.1229v2 (2012)
Lydersen, L., Wiechers, C., Wittmann, C., et al.: Hacking commercial quantum cryptography systems by tailored bright illumination. Nat. Photonics 4(10), 686–689 (2010)
Lydersen, L., Skaar, J.: Security of quantum key distribution with bit and basis dependent detector flaws. Quantum Inf. Comput. 10(1–2), 60–76 (2010)
Zhou, C., Bao, W.S., Fu, X.Q.: Decoy-state quantum key distribution for the heralded pair coherent state photon source with intensity fluctuations. Sci. China Inf. Sci. 53(12), 2485–2494 (2010)
Fung, C.-H.F., Ma, X., Chau, H.F.: Practical issues in quantum-key-distribution postprocessing. Phys. Rev. A 81(1), 012318 (2010)
Marøy, Ø., Lydersen, L., Skaar, J.: Security of quantum key distribution with arbitrary individual imperfections. Phys. Rev. A 82(3), 032337 (2010)
Wegman, M.N., Carter, J.L.: New hash functions and their use in authentication and set equality. J. Comput. Syst. Sci. 22, 265–279 (1981)
Stinson, D.R.: Universal hashing and authentication codes, in advances in cryptology. In: Feigenbaum, J. (ed.) Proceedings of Crypto’91, Ser. Lecture Notes in Computer Science, vol. 576. Berlin, Springer, Germany. pp. 74–85 (1991)
Abidin, A., Larsson, J.-Ä.: Security of authentication with a fixed key in quantum key distribution. arxiv: quant-ph/1109.5168v1 (2011)
Scarani, V., Renner, R.: Quantum cryptography with finite resources: unconditional security bound for discrete-variable protocols with one-way postprocessing. Phys. Rev. Lett. 100(20), 200501 (2008)
König, R., Renner, R., Schaffner, C.: The operational meaning of min- and max-entropy. IEEE Trans. Inf. Theory 55(9), 4337–4347 (2009)
Bratzik, S., Mertz, M., Kampermann, H., Bruß, D.: Min-entropy and quantum key distribution: nonzero key rates for ”small” numbers of signals. Phys. Rev. A 83, 022330 (2011)
Christandl, M., König, R., Renner, R.: Postselection technique for quantum channels with applications to quantum cryptography. Phys. Rev. Lett. 102(2), 020504 (2009)
Tomamichel, M., Renner, R.: Uncertainty relation for smooth entropies. Phys. Rev. Lett. 106(11), 110506 (2011)
Tomamichel, M., Lim, C.C.W., Gisin, N., Renner, R.: Tight finite-key analysis for quantum cryptography. Nat. Commun. 3, 634 (2012). doi:10.1038/ncomms1631
Bennett, C.H., Brassard, G., Crepeau, C., Maurer, U.M.: Generalized privacy amplification. IEEE Trans. Inf. Theory 41(60), 1915–1923 (1995)
Lo, H.-K., Chau, H.F., Ardehali, M.: Efficient quantum key distribution scheme and a proof of its unconditional security. J. Cryptol. 18(2), 133–165 (2005)
Muller-Quade, J., Renner, R.: Composability in quantum cryptography. New J. Phys. 11(8), 085006 (2009)
Krawczyk, H.:LFSR-based hashing and authentication. In: Advances in Cryptology: CRYPTO’94, Lecture Notes in Computer Science vol. 893, pp. 129–139. Springer (1994)
Acknowledgments
The authors would like to thank Xiong-Feng Ma for valuable and enlightening discussions. They gratefully acknowledge the financial support from the National Basic Research Program of China (Grant No. 2013CB338002) and the National Natural Science Foundation of China (Grant No. 11304397).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Zhou, C., Bao, WS., Li, HW. et al. Key-leakage evaluation of authentication in quantum key distribution with finite resources. Quantum Inf Process 13, 935–955 (2014). https://doi.org/10.1007/s11128-013-0703-9
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11128-013-0703-9