Abstract
We propose a multi-mode plug-and-play dual-phase-modulated continuous-variable (CV) quantum key distribution (QKD) protocol where Bob prepares independent and identically distributed dual-phase-modulated coherent states in multiple independent modes and Alice uses a conventional noisy, coherent detector to perform homodyne detection. Benefiting from the plug-and-play configuration, our protocol waives the necessity of propagation of a local oscillator (LO) between trusted parties and generates a real local LO for coherent detection. Therefore, the proposed protocol can effectively against the LO-aimed attacks. Moreover, we obtain enhancement in signal-to-noise ratio thanks to multi-mode coherent states. Simulation results show the performance of our protocol outperforms that of the single-mode plug-and-play dual-phase-modulated CV-QKD protocol. In addition, the performance of the proposed scheme is enhanced with the increased signal modes. Furthermore, we take the finite-size effect and composable security into consideration and thus obtain more practical results than those achieved in the asymptotic limit.









Similar content being viewed by others
References
Lo, H.K., Curty, M., Tamaki, K.: Secure quantum key distribution. Nat. Photonics 8(8), 595 (2014)
Pirandola, S., Andersen, U.L., Banchi, L., Berta, M., Bunandar, D., Colbeck, R., Englund, D., Gehring, T., Lupo, C., Ottaviani, C., Pereira, J.: Advances in quantum cryptography. Adv. Opt. Photon. 12, 1012 (2020)
Lucamarini, M., Yuan, Z.L., Dynes, J.F., Shields, A.J.: Overcoming the rate-distance limit of quantum key distribution without quantum repeaters. Nature 557(7705), 400 (2018)
Scarani, V., Bechmann-Pasquinucci, H., Cerf, N.J., Dušek, M., Lütkenhaus, N., Peev, M.: The security of practical quantum key distribution. Rev. Mod. Phys. 81(3), 1301 (2009)
Liang, L.M., Sun, S.H., Jiang, M.S., Li, C.Y.: Security analysis on some experimental quantum key distribution systems with imperfect optical and electrical devices. Front. Phys. 9(5), 613 (2014)
Xu, F.H., Ma, X.F., Zhang, Q., Lo, H.K., Pan, J.W.: Secure quantum key distribution with realistic devices. Rev. Mod. Phys. 92(2), 025002 (2020)
Weedbrook, C., Pirandola, S., García-Patrón, R., Cerf, N.J., Ralph, T.C., Shapiro, J.H., Lloyd, S.: Gaussian quantum information. Rev. Mod. Phys. 84(2), 621 (2012)
Grosshans, F., Grangier, P.: Continuous variable quantum cryptography using coherent states. Phys. Rev. Lett. 88(5), 057902 (2002)
Grosshans, F., Van Assche, G., Wenger, J., Brouri, R., Cerf, N.J., Grangier, P.: Quantum key distribution using Gaussian-modulated coherent states. Nature 421, 238 (2003)
Navascués, M., Grosshans, F., Acin, A.: Optimality of Gaussian attacks in continuous-variable quantum cryptography. Phys. Rev. Lett. 97(19), 190502 (2006)
García-Patrón, R., Cerf, N.J.: Unconditional optimality of Gaussian attacks against continuous-variable quantum key distribution. Phys. Rev. Lett. 97(19), 190503 (2006)
Leverrier, A., Grosshans, F., Grangier, P.: Finite-size analysis of a continuous-variable quantum key distribution. Phys. Rev. A 81(6), 062343 (2011)
Leverrier, A.: Composable security proof for continuous-variable quantum key distribution with coherent states. Phys. Rev. Lett. 114(7), 070501 (2015)
Renner, R., Cirac, J.I.: de Finetti representation theorem for infinite-dimensional quantum systems and applications to quantum cryptography. Phys. Rev. Lett. 102(11), 110504 (2009)
Furrer, F., Franz, T., Berta, M., Leverrier, A., Scholz, V.B., Tomamichel, M., Werner, R.F.: Continuous variable quantum key distribution: finite-key analysis of composable security against coherent attacks. Phys. Rev. Lett. 109(10), 100502 (2012)
Leverrier, A., García-Patrón, R., Renner, R., Cerf, N.J.: Security of continuous-variable quantum key distribution against general attacks. Phys. Rev. Lett. 110(3), 030502 (2013)
Leverrier, A.: Security of continuous-variable quantum key distribution via a Gaussian de Finetti reduction. Phys. Rev. Lett. 118(20), 200501 (2017)
Huang, D., Huang, P., Lin, D., Zeng, G.: Long-distance continuous-variable quantum key distribution by controlling excess noise. Sci. Rep. 6(1), 19201 (2016)
Jouguet, P., Kunz-Jacques, S., Leverrier, A., Grangier, P., Diamanti, E.: Experimental demonstration of long-distance continuous-variable quantum key distribution. Nat. Photonics 7(5), 378 (2013)
Zhang, Y., Li, Z., Chen, Z., Weedbrook, C., Zhao, Y., Wang, X., Huang, Y., Xu, C., Zhang, X., Wang, Z., Wang, G., Yu, S., Guo, H.: Continuous-variable QKD over 50km commercial fiber. Quantum Sci. Technol. 4(3), 035006 (2019)
Qi, B., Huang, L.L., Qian, L., Lo, H.K.: Experimental study on the Gaussian-modulated coherent-state quantum key distribution over standard telecommunication fibers. Phys. Rev. A 76(5), 052323 (2007)
Jouguet, P., Kunz-Jacques, S., Diamanti, E.: Preventing calibration attacks on the local oscillator in continuous-variable quantum key distribution. Phys. Rev. A 87(6), 062313 (2013)
Ma, X.C., Sun, S.H., Jiang, M.S., Liang, L.M.: Local oscillator fluctuation opens a loophole for Eve in practical continuous-variable quantum-key-distribution systems. Phys. Rev. A 88(2), 022339 (2013)
Qi, B., Lougovski, P., Pooser, R., Grice, W., Bobrek, M.: Generating the local oscillator “locally” in continuous-variable quantum key distribution based on coherent detection. Phys. Rev. X 5(4), 041009 (2015)
Soh, D.B., Brif, C., Coles, P.J., Lütkenhaus, N., Camacho, R.M., Urayama, J., Sarovar, M.: Self-referenced continuous-variable quantum key distribution protocol. Phys. Rev. X 5(4), 041010 (2015)
Huang, D., Huang, P., Lin, D., Wang, C., Zeng, G.: High-speed continuous-variable quantum key distribution without sending a local oscillator. Opt. Lett. 40(16), 3695–3698 (2015)
Wu, X., Wang, Y., Guo, Y., Zhong, H., Huang, D.: Passive continuous-variable quantum key distribution using a locally generated local oscillator. Phys. Rev. A 103(3), 032604 (2021)
Wu, X., Wang, Y., Huang, D.: Passive continuous-variable quantum secret sharing using a thermal source. Phys. Rev. A 101(2), 022301 (2020)
Grice, W.P., Qi, B.: Quantum secret sharing using weak coherent states. Phys. Rev. A 100(2), 022339 (2019)
Pirandola, S., Ottaviani, C., Spedalieri, G., Weedbrook, C., Braunstein, S.L., Lloyd, S., Gehring, T., Jacobsen, C.S., Andersen, U.L.: High-rate measurement-device-independent quantum cryptography. Nat. Photonics 9(6), 397 (2015)
Zhang, Y.C., Li, Z., Yu, S., Gu, W.Y., Peng, X., Guo, H.: Continuous-variable measurement-device-independent quantum key distribution using squeezed states. Phys. Rev. A 90(5), 052325 (2014)
Li, Z., Zhang, Y., Xu, F., Peng, X., Guo, H.: Continuous-variable measurement-device-independent quantum key distribution. Phys. Rev. A 89(5), 052301 (2014)
Wu, X.D., Wang, Y.J., Huang, D., Guo, Y.: Simultaneous measurement-device-independent continuous variable quantum key distribution with realistic detector compensation. Front. Phys. 15(3), 31601 (2020)
Liao, Q., Wang, Y., Huang, D., Guo, Y.: Dual-phase-modulated plug-and-play measurement-device-independent continuous-variable quantum key distribution. Opt. Express 26(16), 19907 (2018)
Wu, X., Wang, Y., Li, S., Zhang, W., Huang, D., Guo, Y.: Security analysis of passive measurement-device-independent continuous-variable quantum key distribution with almost no public communication. Quantum Inf. Process. 18(12), 372 (2019)
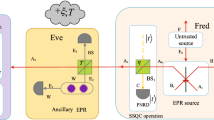
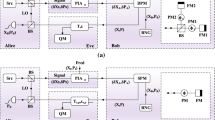
Huang, D., Huang, P., Wang, T., Li, H., Zhou, Y., Zeng, G.: Continuous-variable quantum key distribution based on a plug-and-play dual-phase-modulated coherent-states protocol. Phys. Rev. A 94(3), 032305 (2016)
Wu, X., Wang, Y., Liao, Q., Zhong, H., Guo, Y.: Simultaneous classical communication and quantum key distribution based on plug-and-play configuration with an optical amplifier. Entropy 21(4), 333 (2019)
Bai, D., Huang, P., Ma, H., Wang, T., Zeng, G.: Performance improvement of plug-and-play dual-phase-modulated quantum key distribution by using a noiseless amplifier. Entropy 19(10), 546 (2017)
Wu, X.D., Wang, Y.J., Zhong, H., Liao, Q., Guo, Y.: Plug-and-play dual-phase-modulated continuous-variable quantum key distribution with photon subtraction. Front. Phys. 14(4), 41501 (2019)
Wu, X., Wang, Y., Zhong, H., Ye, W., Huang, D., Guo, Y.: Performance improvement of plug-and-play dual-phase-modulated continuous-variable quantum key distribution with quantum catalysis. Quantum Inf. Process. 19(8), 234 (2020)
Kumar, R., Tang, X., Wonfor, A., Penty, R., White, I.: Continuous variable quantum key distribution with multi-mode signals for noisy detectors. J. Opt. Soc. Am. B 36(3), B109 (2019)
Fang, J., Huang, P., Zeng, G.: Multichannel parallel continuous-variable quantum key distribution with Gaussian modulation. Phys. Rev. A 89(2), 022315 (2014)
Usenko, V.C., Ruppert, L., Filip, R.: Entanglement-based continuous-variable quantum key distribution with multimode states and detectors. Phys. Rev. A 90(6), 062326 (2014)
Derkach, I., Usenko, V.C., Filip, R.: Continuous-variable quantum key distribution with a leakage from state preparation. Phys. Rev. A 96(6), 062309 (2017)
Qu, Z., Djordjevic, I.B.: High-speed free-space optical continuous-variable quantum key distribution enabled by three-dimensional multiplexing. Opt. Express 25(7), 7919 (2017)
Qu, Z., Djordjevic, I.B.: Four-dimensionally multiplexed eight-state continuous-variable quantum key distribution over turbulent channels. IEEE Photon. J. 9(6), 7600408 (2017)
Pirandola, S., Laurenza, R., Ottaviani, C., Banchi, L.: Fundamental limits of repeaterless quantum communications. Nat. Commun. 8(1), 15043 (2017)
Kumar, R., Qin, H., Alléaume, R.: Coexistence of continuous variable QKD with intense DWDM classical channels. New J. Phys. 17(4), 043027 (2015)
Acknowledgements
This work was supported by the National Natural Science Foundation of China (Grant No. 61801522) and National Nature Science Foundation of Hunan Province, China (Grant No. 2019JJ40352).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendices
Appendix A: Calculation of asymptotic secret key rate of multi-mode plug-and-play DPMCS protocol
We now perform the calculation of asymptotic secret key rate of our multi-mode plug-and-play DPMCS protocol. In the case of reverse reconciliation, the asymptotic secret key rate under collective attack is given by
where \(I^{n}(A:B)=\frac{1}{2}\mathrm{log}_{2}(1+\mathrm{SNR}_{n})\) represents the mutual information between Alice and Bob and \(\mathrm{SNR}_{n}\) has been analyzed in Eq. (6), \(\chi (A:E)\) represents the maximum information available to Eve on Alice’s key, and \(\beta \) represents the efficiency of the reconciliation algorithm.
The channel transmittance is described as \(T=10^{\frac{-\gamma d}{10}}\) under the assumption that the quantum channel between Alice and Bob is telecom fiber, parameters \(\gamma \) and d stand for an attenuation coefficient and the fiber length in kilometers, respectively.
In order to estimate \(\chi (A:E)\), the realistic noise model is adopted where Eve cannot control the loss inside Alice’s system, and the detector noise from Alice can be deemed to be trusted [9], which has been utilized widely in CV-QKD experiments [19, 21, 48]. Based on this model, \(\chi (A:E)\) can be given by
where \(G(x)=(x+1)\mathrm{log}_{2}(x+1)-x\mathrm{log}_{2}x\).
where
where
Appendix B: Finite-size secret key rate of multi-mode plug-and-play DPMCS protocol
For the proposed multi-mode plug-and-play DPMCS protocol, the finite-size secret key rate is given by
where \(\beta \) and \(I^{n}(A:B)\) have been defined above. m represents the number of signals which is utilized to share key between Alice and Bob and M represents the total exchanged signals. Then, the remained signals \(h=M-m\) is utilized to perform parameter estimation. \(\epsilon _{\mathrm{PE}}\) denotes the failure probability of parameter estimation. Parameter \(\varDelta (m)\) is related to the security of the privacy amplification, which is given by
where \(\bar{\epsilon }\) stands for the smoothing parameter, \(\epsilon _{\mathrm{PA}}\) stands for the failure probability of privacy amplification, and the Hilbert space corresponding to the Alice’s raw key is represented by \(\mathrm{dim}\varPi _{A}\). Here, \(\mathrm{dim}\varPi _{A}\) is set to be 2 due to that the raw key is usually encoded on binary bits.
Note that it is necessary to compute \(\chi _{\epsilon _{\mathrm{PE}}}(A:E)\) in parameter estimation procedure with the help of the covariance matrix \(\varXi _{\epsilon _{\mathrm{PE}}}\). This covariance matrix can minimize the finite-size secret key rate with a probability of \(1-\epsilon _{\mathrm{PE}}\). By using h couples of correlated variables \((x_{j},y_{j})_{j=1\ldots h}\), we can calculate the covariance matrix \(\varXi _{\epsilon _{\mathrm{PE}}}\). Consequently, we need to sample h couples of correlated variables \((x_{j},y_{j})_{j=1\ldots h}\) and use a normal model for these correlated variables to link Alice’s and Bob’s data, which is given by
where \(\delta =\sqrt{T}\) and z follows a centered normal distribution with variance \(\omega ^{2}=1+T\xi _{t}\). Then, the covariance matrix \(\varXi _{\epsilon _{\mathrm{PE}}}\) can be expressed as
where \(\delta _{\mathrm{min}}\) and \(\omega ^{2}_{\mathrm{max}}\) represent the minimum of \(\delta \) and maximum of \(\omega ^{2}\) compatible with sampled couples except with probability \(\epsilon _{\mathrm{PE}}/2\), and \(Z=\sqrt{V^{2}_{B}+2V_{B}}\). Then, the Maximum-likelihood estimators \(\hat{\delta }\) and \(\hat{\omega }^{2}\) are, respectively, given by
Besides, \(\hat{\delta }\) and \(\hat{\omega }^{2}\) follow the distributions
which indicates that \(\hat{\delta }\) and \(\hat{\omega }^{2}\) are independent for each other. Because parameters \(\delta \) and \(\omega ^{2}\) shown in Eq. (20) are true values, we can write the expressions of \(\hat{\delta }\) and \(\hat{\omega }^{2}\), which are
where \(z_{\epsilon _{\mathrm{PE}}/2}\) is such that \(1-erf(z_{\epsilon _{\mathrm{PE}}/2}/\sqrt{2})/2=\epsilon _{\mathrm{PE}}/2\), and \(erf(x)=\frac{2}{\sqrt{\pi }}\int ^{x}_{0}e^{-t^{2}}dt\) represents error function. Based on the expected values of \(\hat{\delta }\) and \(\hat{\omega }^{2}\), which are given by \(E[\hat{\delta }]=\sqrt{T}\) and \(E[\hat{\omega }^{2}]=1+T\xi _{t}\), \(\hat{\delta }\) and \(\hat{\omega }^{2}\) are expressed as
It is noteworthy that we can choose the optimal value of the error probabilities as
Therefore, we can obtain the finite-size secret key rate of multi-mode plug-and-play DPMCS protocol by utilizing the derived bound \(\delta _{\mathrm{min}}\) and \(\omega ^{2}_{\mathrm{max}}\).
Appendix C: Multi-mode plug-and-play DPMCS protocol in composable security
Here, we calculate the secret key rate of the proposed multi-mode plug-and-play DPMCS protocol in composable security framework. According to Ref. [13], the proposed multi-mode plug-and-play DPMCS protocol is \(\epsilon \)-secure against collective attacks if \(\epsilon =2\epsilon _{sm}+\bar{\epsilon }+\epsilon _{\mathrm{PE}}/\epsilon +\epsilon _{\mathrm{cor}}/\epsilon +\epsilon _{\mathrm{ent}}/\epsilon \) and if the length of final key m is chosen such that
where \(\hat{H}_{\mathrm{MLE}}(U)\) represents the empiric entropy of U, \(F(\varTheta ^{\mathrm{max}}_{a}, \varTheta ^{\mathrm{max}}_{b}, \varTheta ^{\mathrm{max}}_{c})\) stands for the function computing the Holevo information between Eve and Alice, and
In the following, we analyze the secret key rate of the multi-mode plug-and-play DPMCS protocol in composable security framework. The following model is taken advantage of for the error correction
where \(\beta \) represents reconciliation efficiency and \(I^{n}(A:B)\) stands for the mutual information between Alice and Bob in multi-mode plug-and-play DPMCS protocol. For our protocol, we have
What is more, the robustness of our protocol is chosen \(\epsilon _{\mathrm{rob}}\le 10^{-2}\), which can be achieved when the probability of parameter estimation is at least 0.99. Based on this, the values of random variables ||X||, ||Y|| and \(\langle X,Y\rangle \) satisfy the following restraints
where \(C^{n}_{BA}\) represents the correlation between Bob’s and Alice’s data after channel in our protocol. Using these bound, we can achieve
Finally, the secret key rate of our protocol can be calculated in composable security framework as follows:
It is worth mentioning that the parameters shown above are set
in order to be \(\epsilon \) secure against collective attacks with \(\epsilon =10^{-20}\).
Rights and permissions
About this article
Cite this article
Wu, X., Wang, Y., Huang, D. et al. Multi-mode plug-and-play dual-phase-modulated continuous-variable quantum key distribution. Quantum Inf Process 20, 143 (2021). https://doi.org/10.1007/s11128-021-03076-2
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-021-03076-2