Abstract
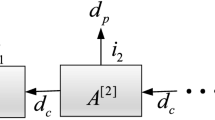
Almost currently published quantum key distribution (QKD) protocols are variants of the first protocol proposed by Bennett and Brassard, and the generic entanglement-based protocol. These protocols, however, are not very efficient. An improvement of key generation rate is possible by using quantum many-body systems, and tensor network states provides a compact model for them. The work presents an improved QKD protocol, which first uses partial isometries to compress a matrix product state (MPS) \(|\Psi \rangle \) into its compressed MPS \(|\Psi ^{(n)}\rangle \). Then, Alice uses \(|\Psi ^{(n)}\rangle \) to communicate with Bob via a quantum channel. Next, Alice transmits the number of compressed operations to Bob via a secure classical channel. Finally, according to the measured results, Alice and Bob share a cryptographic key from the MPS \(|\Psi \rangle \). Our protocol can obtain a higher key generation capability and a longer communication distance. We apply the flow network model to obtain the upper bound of the dimension of the geometric index.









Similar content being viewed by others
Data Availability
Data sharing not applicable to this article as no datasets were generated or analyzed during the current study.
References
Caleffi, M., Chandra, D., Cuomo, D., et al.: The rise of the quantum internet. Computer 53(6), 67–72 (2020)
Wehner, S., Elkouss, D., Hanson, R.: Quantum internet: a vision for the road ahead. Science 362(6412), eaam9288 (2018)
Caleffi, M., Cacciapuoti, A.S., Bianchi, G.: Quantum Internet: From communication to distributed computing! In: Proceedings of the 5th ACM International Conference on Nanoscale Computing and Communication, pp. 1–4 (2018)
Nielsen, M., Chuang, I.: Quantum computation and quantum information: 10th, anniversary Cambridge University Press, Cambridge (2010)
Elliott, C., Pearson, D., Troxel, G.: Quantum cryptography in practice. In: Proceedings of the 2003 conference on applications, technologies, architectures, and protocols for computer communications, pp. 227–238 (2003)
Peev, M., Pacher, C., Allaume, R., et al.: The SECOQC quantum key distribution network in Vienna. New J. Phys. 11(7), 075001 (2009)
Sasaki, M., Fujiwra, M., Ishizuka, H., et al.: Tokyo QKD network and the evolution to secure photonic network. In: CLEO: Science and Innovations. Optical Society of America, JTuC1 (2011)
Chen, T.Y., Wang, J., Liang, H., et al.: Metropolitan all-pass and inter-city quantum communication network. Opt. Express 18(26), 27217–27225 (2010)
Zhang, Q., Xu, F., Chen, Y.A., et al.: Large scale quantum key distribution: challenges and solutions. Opt. Express 26(18), 24260–24273 (2018)
Joshi, S.K., Aktas, D., Wengerowsky, S., et al.: A trusted nodeCfree eight-user metropolitan quantum communication network. Sci. Adv. 6(36), eaba0959 (2020)
Li, Q., Wang, Y., Mao, H., et al.: Mathematical model and topology evaluation of quantum key distribution network. Opt. Express 28(7), 9419–9434 (2020)
Gyöngyösi, L., Bacsardi, L., Imre, S.: A survey on quantum key distribution. Infocommun. J. 11(2), 14–21 (2019)
Sharma, A., Kumar, A.: A survey on quantum key distribution. In: 2019 International Conference on Issues and Challenges in Intelligent Computing Techniques (ICICT), vol. 1, pp. 1–4. IEEE (2019)
Ran, S.J., Sun, Z.Z., Fei, S.M., et al.: Tensor network compressed sensing with unsupervised machine learning. Phys. Rev. Res. 2(3), 033293 (2020)
Bourennane, M., Karlsson, A., Björk, G.: Quantum key distribution using multilevel encoding. Phys. Rev. A 64(1), 012306 (2001)
Djordjevic, I.B.: On global quantum communication networking. Entropy 22(8), 831 (2020)
Shao, C., Li, Y., Li, H.: Quantum algorithm design: techniques and applications. J. Syst. Sci. Complex. 32(1), 375–452 (2019)
Abubakar, M.Y., Jung, L.T., Zakaria, N., et al.: Reversible circuit synthesis by genetic programming using dynamic gate libraries. Quantum Inf. Process. 16(6), 160 (2017)
Younes, A.: On the universality of n-bit reversible gate libraries. Appl. Math. Inf. Sci. 9(5), 2579 (2015)
Castelvecchi, D.: The quantum internet has arrived (and it hasn’t). Nature 554(7690), 289–293 (2018)
Gyongyosi, L., Imre, S.: Entanglement accessibility measures for the quantum Internet. Quantum Inf. Process. 19(4), 1–28 (2020)
Sarma, S.D., Deng, D.L., Duan, L.M.: Machine learning meets quantum physics. arXiv preprint arXiv:1903.03516 (2019)
Sun, Z.Z., Peng, C., Liu, D., et al.: Generative tensor network classification model for supervised machine learning. Phys. Rev. B 101(7), 075135 (2020)
Cichocki, A.: Era of big data processing: a new approach via tensor networks and tensor decompositions. arXiv preprint arXiv:1403.2048 (2014)
Lee, N., Cichocki, A.: Fundamental tensor operations for large-scale data analysis using tensor network formats. Multidimens. Syst. Signal Process. 29(3), 921–960 (2018)
Wang, X., Yang, L.T., Wang, Y., et al.: A distributed tensor-train decomposition method for cyber-physical-social services. ACM Trans. Cyber-Phys. Syst. 3(4), 1–15 (2019)
Manzoni, M.T., Chang, D.E., Douglas, J.S.: Simulating quantum light propagation through atomic ensembles using matrix product states. Nat. Commun. 8(1), 1–11 (2017)
Ors, R.: Tensor networks for complex quantum systems. Nat. Rev. Phys. 1(9), 538–550 (2019)
Verstraete, F., Cirac, J.I.: Matrix product states represent ground states faithfully. Phys. Rev. B 73(9), 094423 (2006)
Ran, S.J., Tirrito, E., Peng, C., et al.: Tensor Network Contractions: Methods and Applications to Quantum Many-Body Systems. Springer Nature (2020)
Verstraete, F., Wolf, M.M., Perez-Garcia, D., et al.: Criticality, the area law, and the computational power of projected entangled pair states. Phys. Rev. Lett. 96(22), 220601 (2006)
Shi, Y.Y., Duan, L.M., Vidal, G.: Classical simulation of quantum many-body systems with a tree tensor network. Phys. Rev. A 74(2), 022320 (2006)
Vidal, G.: Entanglement renormalization. Phys. Rev. Lett. 99(22), 220405 (2007)
Bennett, C. H.: Quantum cryptography: public key distribution and coin tossing. In: Proc of IEEE International Conference on Computers. Institute of Electrical and Electronics Engineers (1984)
Wang, X.B.: Beating the photon-number-splitting attack in practical quantum cryptography. Phys. Rev. Lett. 94(23), 230503 (2005)
Lo, H.K., Ma, X., Chen, K.: Decoy state quantum key distribution. Phys. Rev. Lett. 94(23), 230504 (2005)
Ekert, A.K.: Quantum cryptography based on Bells theorem. Phys. Rev. Lett. 67(6), 661 (1991)
Bennett, C.H., Brassard, G., Mermin, N.D.: Quantum cryptography without Bells theorem. Phys. Rev. Lett. 68(5), 557 (1992)
Bai, G., Yang, Y., Chiribella, G.: Quantum compression of tensor network states. New J. Phys. 22(4), 043015 (2020)
Singh, S., Pfeifer, R.N.C., Vidal, G.: Tensor network states and algorithms in the presence of a global U (1) symmetry. Phys. Rev. B 83(11), 115125 (2011)
Hauru, M., Van Damme, M., Haegeman, J.: Riemannian optimization of isometric tensor networks. arXiv preprint arXiv:2007.03638 (2020)
Lin, Y.Y., Sun, J.R., Sun, Y.: Surface growth scheme for bulk reconstruction and tensor network. arXiv preprint arXiv:2010.01907 (2020)
Lashkari, N.: Modular zero modes and sewing the states of QFT. J. High Energ. Phys. 2021, 189 (2021)
Sanz, M., Egusquiza, I., Di Candia, R., et al.: Entanglement classification with matrix product states. Sci. Rep. 6, 30188 (2016)
Ors, R.: A practical introduction to tensor networks: Matrix product states and projected entangled pair states. Ann. Phys. 349, 117–158 (2014)
Kaltenbaek, R., Lavoie, J., Zeng, B., et al.: Optical one-way quantum computing with a simulated valence-bond solid. Nat. Phys. 6(11), 850–854 (2010)
Liu, L.L., Hwang, T.: Controlled remote state preparation protocols via AKLT states. Quantum Inf. Process. 13(7), 1639–1650 (2014)
Hauschild, J., Pollmann, F.: Efficient numerical simulations with tensor networks: tensor network python (TeNPy). SciPost Phys. Lect. Notes (2018). https://doi.org/10.21468/SciPostPhysLectNotes.5
Cohen, D.: Lecture notes in quantum mechanics. arXiv preprint arXiv:quant-ph/0605180 (2006)
Cormen, T.H., Leiserson, C.E., Rivest, R.L., Stein, C.: Introduction to Algorithms. MIT Press, Cambridge (2009)
Pirandola, S.: End-to-end capacities of a quantum communication network. Commun. Phys. 2(1), 1–10 (2019)
Xu, F., Ma, X., Zhang, Q., et al.: Secure quantum key distribution with realistic devices. Rev. Mod. Phys. 92(2), 025002 (2020)
Sarvaghad-Moghaddam, M.: Efficient controlled bidirectional quantum secure direct communication using entanglement swapping in a network. arXiv preprint arXiv:1902.11188 (2019)
Wang, Y., Li, Q., Han, Q., et al.: Modeling and simulation of practical quantum secure communication network. Quantum Inf. Process. 18(9), 278 (2019)
Gottesman, D., Lo, H. K., Lutkenhaus, N., et al.: Security of quantum key distribution with imperfect devices. In: International Symposium on Information Theory, ISIT 2004. Proceedings, p. 136. IEEE (2004)
Acknowledgements
Qiang Zhang and Hong Lai have been been supported by the National Natural Science Foundation of China (No. 61702427) and the Fundamental Research Funds for the Central Universities (XDJK2020B027), the Venture & Innovation Support Program for Chongqing Overseas Returnees (No. cx2018076), and the financial support in part by the 1000-Plan of Chongqing by Southwest University (No. SWU116007). Josef Pieprzyk has been supported by Australian Research Council (ARC) Grant DP180102199 and Polish National Science Center (NCN) Grant 2018/31/B/ST6/03003.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Zhang, Q., Lai, H., Pieprzyk, J. et al. An improved quantum network communication model based on compressed tensor network states. Quantum Inf Process 21, 253 (2022). https://doi.org/10.1007/s11128-022-03609-3
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-022-03609-3