Abstract
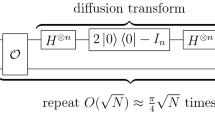
Due to the powerful computing capability of quantum computers, cryptographic researchers have applied quantum algorithms to cryptanalysis and obtained many interesting results. Finding the linear structure of a vector function is an important task in cryptography. In this work, we study how to reduce the complexity of finding linear structure using the Bernstein–Vazirani (BV) algorithm and give a new quantum linear structure finding algorithm with complexity O(n). Our result realizes a quadratic speedup compared with the previous algorithm (with complexity \(O(n^{2})\)). This leads to a more efficient analysis of symmetric cryptography, that is, the complexity of some previous BV-based attacks reduces from \(O(n^{2})\) to O(n). Besides, we find two new applications for this kind of BV-based attack, i.e., related-key attacks on iterated Even–Mansour ciphers and i-round Feistel ciphers with independent round keys.







Similar content being viewed by others
Notes
We can input x to the “black box" and ask it to compute f(x) , but we don’t have access to its internal computation process.
When there is no ambiguity, we write 0 for the vector \((0,0,\cdots ,0)\) of appropriate length.
References
Bernstein, Ethan, Vazirani, Umesh: Quantum complexity theory. In Proceedings of the 25th ACM Symposium on the Theory of Computing, pages 11-20, (1993)
Biham, E.: New types of cryptanalytic attacks using related keys. J. Cryptol. 7(4), 229–246 (1994)
Biryukov, A., Wagner, D.: Slide attacks. In: Knudsen, L. (ed.) Fast Software Encryption, FSE 1999, vol. 1636, pp. 245–259. Lecture Notes in Computer ScienceSpringer, Berlin, Heidelberg (1999)
Biryukov, A., Wagner, D.: Advanced slide attacks. In: Preneel, B. (ed.) Advances in Cryptology-EUROCRYPT 2000, vol. 1807, pp. 589–606. Lecture Notes in Computer ScienceSpringer, Berlin, Heidelberg (2000)
Boneh, D., Zhandry, M.: Secure signatures and chosen ciphertext security in a quantum computing world. In: Canetti, R., Garay, J.A. (eds.) CRYPTO 2013, Part II. LNCS, vol. 8043, pp. 361–379. Springer, Heidelberg (2013)
Daemen, j., Rijmen, V.: Probability distributions of correlation and differentials in block ciphers. Journal of Mathematical Cryptology. 1(3), 221-242 (2007)
Damgård, I., Funder, J., Nielsen, J.B., Salvail, L.: Superposition attacks on cryptographic protocols. In: Padró, C. (ed.) ICITS 2013. LNCS, vol. 8317, pp. 142–161. Springer, Heidelberg (2014)
Dong, X., Dong, B., Wang, X.: Quantum attacks on some feistel block ciphers. Des. Codes Cryptogr. 88, 1179–1203 (2020)
Dubuc, S.: Characterization of linear structures. Des., Codes Cryptogr. 22, 33–45 (2001)
Dunkelman, O., Keller, N., Shamir, A.: A Practical-Time Related-Key Attack on the KASUMI Cryptosystem Used in GSM and 3G Telephony. In: Rabin, T. (ed.) Advances in Cryptology-CRYPTO 2010, LNCS, vol. 6223, pp. 393–410. Springer, Heidelberg (2010)
Even, S., Mansour, Y.: A construction of a cipher from a single pseudorandom permutation. J. Crypt. 10(3), 151–162 (1997)
Ferguson, N., Kelsey, J., Lucks, S., et al.: Improved cryptanalysis of Rijndael. In: Goos, G., Hartmanis, J., van Leeuwen, J., Schneier, B. (eds.) Fast Software Encryption. FSE 2000. LNCS, vol. 1978, pp. 213-230. Springer, Heidelberg (2001)
Grilo, A.B., Kerenidis, I., Zijlstra, T.: Learning with errors is easy with quantum samples. Phys. Rev. A 99(3), 032314 (2019)
Grover, L.K.: A Fast Quantum Mechanical Algorithm for Database Search. In: Miller, G.L. (ed.) Proceedings of the Twenty-Eighth Annual ACM Symposium on the Theory of Computing, Philadelphia, Pennsylvania, USA, May 22-24, 1996. pp. 212-219. ACM (1996)
Guo, J., Peyrin, T., Poschmann, A., Robshaw, M.: The LED block cipher, in Proceedings of 2011 International Workshop on Cryptographic Hardware and Embedded Systems (CHES 2011), Nara, Japan, pp. 326-341 (2011)
Hao, Xuexuan, Zhang, Fengrong, Wei, Yongzhuang, Zhou, Yong: Quantum period finding based on the Bernstein-Vazirani algorithm. Quantum Inf. Comput. 20(1–2), 65–84 (2020)
Hoeffding, W.: Probability Inequalities for sums of Bounded Random Variables. In: Fisher, N.I., Sen, P.K. (eds) The Collected Works of Wassily Hoeffding. Springer Series in Statistics. Springer, New York, NY. (1994)
Hosoyamada A., Sasaki Y.: Quantum Demiric-Selçuk Meet-in-the-Middle Attacks. Applications to 6-Round Generic Feistel Constructions. In: Catalano D, De Prisco R, (eds.), Security and Cryptography for Networks-11th International Conference, SCN 2018. Lecture Notes in Computer Science, vol. 11035. Springer, Cham, pp. 386-403 (2018)
Hosoyamada, A., Aoki, K.: On Quantum Related-Key Attacks on Iterated Even-Mansour Ciphers. In: Obana, S., Chida, K. (eds.) Advances in Information and Computer Security, IWSEC 2017. LNCS, vol. 10418, pp. 3–18. Springer, Cham (2017)
Kaplan M., Leurent G., Leverrier A., et al.: Breaking symmetric cryptosystems using quantum period finding. In: CRYPTO 2016, Part II, pp. 207-237 (2016)
Kaplan, M., Leurent, G., Leverrier, A., et al.: Quantum differential and linear cryptanalysis. IACR Trans. Symmetric Cryptol. 1, 71–94 (2016)
Knudsen, L.R.: Cryptanalysis of LOKI91. In: Seberry, J., Zheng, Y. (eds.) Advances in Cryptology-AUSCRYPT’92 LNCS, vol. 718, pp. 22–35. Springer, Heidelberg (1993)
Kuwakado, H., Morii, M.: Quantum distinguisher between the 3-round Feistel cipher and the random permutation. In: 2010 IEEE International Symposium on Information Theory Proceedings (ISIT), June 2010, pp. 2682-2685 (2010)
Kuwakado, H., Morii, M.: Security on the quantum-type Even-Mansour cipher. In: Proceedings of the International Symposium on Information Theory and its Applications, ISITA 2012, Honolulu, HI, USA, October 28-31, 2012. pp. 312-316 (2012)
Leander, G., May, A.: Grover Meets Simon - Quantumly Attacking the FX-construction, Advances in Cryptology - ASIACRYPT, pp. 161-178 (2017)
Li, H., Yang, L.: A quantum algorithm to approximate the linear structures of Boolean functions. Math. Struct. Comput. Sci. 28, 1–13 (2018)
Liu, H.L., Wu, Y.S., Wan, L.C., et al.: Variational quantum algorithm for the Poisson equation. Phys. Rev. A 104(2), 022418 (2021)
Mantin, I.: A Practical Attack on the Fixed RC4 in the WEP Mode. In: Roy, B. (ed.) Advances in Cryptology-ASIACRYPT 2005, LNCS, vol. 3788, pp. 395–411. Springer, Heidelberg (2005)
Nyberg K.: Differentially uniform mappings for cryptography. In: EUROCRYPT, pp. 55-64 (1993)
O’connor, L., Klapper, A.: Algebraic nonlinearity and its applications to cryptography. J. Cryptol. 7(4), 213–227 (1994)
Pan, S.J., Wan, L.C., Liu, H.L., et al.: Improved quantum algorithm for A-optimal projection. Phys. Rev. A 102(5), 052402 (2020)
Santoli, T., Schaffner, C.: Using simons algorithm to attack symmetric-key cryptographic primitives. Quantum Inf. Comput. 17, 65–78 (2017)
Shi, T.R., Jin, C.H., Hu, B., et al.: Complete analysis of Simon’s quantum algorithm with additional collisions. Quantum Inf. Process 18, 334 (2019). https://doi.org/10.1007/s11128-019-2444-x
Shor, P.W.: Algorithms for quantum computation: Discrete logarithms and factoring. In: 35th Annual Symposium on Foundations of Computer Science. pp. 124-134. IEEE Computer Society (1994)
Simon, D.R.: On the power of quantum computation. SIAM J. Comput. 26(5), 1474–1483 (1997)
Wan, L.C., Yu, C.H., Pan, S.J., et al.: Asymptotic quantum algorithm for the Toeplitz systems. Phys. Rev. A 97(6), 062322 (2018)
Xie, H., Yang, L.: Using Bernstein-Vazirani algorithm to attack block ciphers. Des. Codes Cryptogr. 87, 1161–1182 (2019)
Xie, H., Yang, L.: A quantum related-key attack based on the Bernstein-Vazirani algorithm. Quantum Inf. Proc. 19(8), 1–20 (2020)
Yu, C.H., Gao, F., Wen, Q.: An improved quantum algorithm for ridge regression. IEEE Transactions on Knowledge and Data Engineering, (2019)
Yu, C.H., Gao, F., Wang, Q.L., et al.: Quantum algorithm for association rules mining. Phys. Rev. A 94(4), 042311 (2016)
Yu, C.H., Gao, F., Lin, S., et al.: Quantum data compression by principal component analysis. Quantum Inf. Proc. 18(8), 1–20 (2019)
Yu, C.H., Gao, F., Liu, C., et al.: Quantum algorithm for visual tracking. Phys. Rev. A 99(2), 022301 (2019)
Acknowledgements
We would like to thank the anonymous referees for their helpful comments. H.-W. Sun thanks L.-C. Wan, H.-L. Liu, and S.-J. Pan for fruitful discussions. This work is supported by the National Natural Science Foundation of China (Grant Nos. 61972048, 61976024, 61902166), Henan Key Laboratory of Network Cryptography Technology (LNCT2021-A10), and the Natural Science Foundation of Henan (Grant No. 212300410062).
Author information
Authors and Affiliations
Corresponding authors
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendices
A Proof of Theorem 3
Theorem 3
If \(\delta _{F}'\le p_{0}<1\), then algorithms 3 and 4 return \((a,i_{1}i_{2}\cdots i_{n})\) with cn queries, with probability at least \(1-(2p^{c}_{0})^{n}\).
Proof
The proof of Theorem 3 is based on the lemma as shown in [6]. This lemma shows that let \(f\in B_{n}\), then \(\forall a\in F^{n}_{2}\), \(\forall i\in F_{2}\), it holds that
Now we give the proof of Theorem 3, which is similar to Ref. [19, 38]. Without loss of generality, we prove the case that i is not known. The case with known i can be proved in a similar way. Then, according to the above lemma, the probability of getting an \(\omega \) satisfying \(\omega \cdot a=0\) after running the BV algorithm on \(\phi ^{j}_{s}\) is
Notice that the parameter \(\delta _{\phi }'\) satisfies
Let \(\omega _{1},\omega _{2},\cdots ,\omega _{cn}\in \{0,1\}^{n}\) be the vectors that are obtained by operating the subroutine (steps 1-4) of algorithm c times. Note that each \(\omega _{1},\omega _{2},\cdots ,\omega _{cn}\) is orthogonal to \(\sigma \), since \(Pr_{x}[\phi _{s}(x\oplus \sigma )=\phi _{s}(x)]=1\), and thus, outputs of the subroutine of algorithm 4 are always orthogonal to \(\sigma \) due to Lemma 1.
Then, we can determine \(\sigma \) if and only if \(dim(Span(\omega _{1},\omega _{2},\cdots ,\omega _{cn}))=dim(\sigma ^{\perp })\), and the probability that we cannot determine \(\sigma \) is equal to the probability that there exists \(t\notin \sigma ^{\perp }\) such that \(Span(\omega _{1},\omega _{2},\cdots ,\omega _{cn})\perp t\). Therefore,
where the first inequality results from the union bound and the second inequality follows from the fact that cn queries are independent.
After cn calls to the subroutine of our algorithm, the probability of obtaining the period \(\sigma \) is
Find a from \(\sigma \), and calculate \(i_{1}i_{2}\cdots i_{n}=F(x\oplus a)\oplus F(x)\). Then, we can obtain \((a,i_{1}i_{2}\cdots i_{n})\). Thus, the conclusion holds. \(\square \)
B Proof of Theorem 4
Theorem 4
If running algorithms 3 and 4 on a function \(F\in C_{n,n}\) return \((a,i_{1}i_{2}\cdots i_{n})\), then for all \(\epsilon \) satisfying \(0<\epsilon <1\), we have
Proof
Now we give the proof of Theorem 4, which is similar to Ref. [26, 38]. For the output vector \((a,i_{1}i_{2}\cdots i_{n})\), let the probability of getting an \(\omega \) satisfying \(\omega \cdot a=i_{j}\) after running the BV algorithm on \(F_{j}\) is
Then,
where \(1\le j\le n\), and \(p,q\in [0,1]\). Let Y be a random variable
where \(\omega \) is the output of the BV algorithm. Then, the expectation of Y is \(E(Y)=1\cdot q_{j}=q_{j}=1-p_{j}\). In addition, c runs of the BV algorithm on \(F_{j}\) correspond to c independent identical random variables \(Y_{1},Y_{2},\cdots ,Y_{c}\). Next, we prove that \(Pr[q_{j}\ge \epsilon ]\le e^{-2c\epsilon ^{2}}\), for which we first introduce Hoeffding’s inequality [18]. Consider a set of n independent random variables, such that \(X_{i}\in [a,b]\), \(i=1,2,\cdots ,n.\) Let \({\overline{X}}=\frac{X_{1}+\cdots +X_{n}}{n}\). Then, it follows that for \(\forall t>0\),
Thus, by Hoeffding’s inequality, we obtain
Now that we have obtained \((a,i_{1}i_{2}\cdots i_{n})\), \(\frac{1}{c}\Sigma ^{c}_{l=1}Y_{l}\) in Eq. 37 must equal 0 (because if there exists some \(Y_{l}=1\), we cannot obtain \((a,i_{1}i_{2}\cdots i_{n})\)). Hence,
From Eq. 38, it follows
Thus, the probability that
holds is greater than \(1-e^{-2c\epsilon ^{2}}\). Then, there are at least \(2^{n}[2(1-\epsilon )-1]=2^{m}(1-2\epsilon )\) x that satisfy \(F_{j}(x\oplus a)\oplus F_{j}(x)=i_{j}\) for both \(j=1\) and \(j=2\). That is, for all \(j=1,2,\cdots ,n\), we have
Thus, the conclusion holds. \(\square \)
Data sharing is not applicable to this article as no datasets were generated or analyzed during the current study.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Sun, HW., Wei, CY., Cai, BB. et al. Improved BV-based quantum attack on block ciphers. Quantum Inf Process 22, 9 (2023). https://doi.org/10.1007/s11128-022-03752-x
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-022-03752-x