Abstract
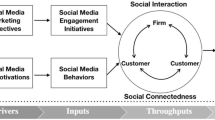
This article presents a review of the social media-based systems; an emerging area of information system research, design, and practice shaped by social media phenomenon. Social media-based system (SMS) is the application of a wider range of social software and social media phenomenon in organizational and non-organization context to facilitate every day interactions. To characterize SMS, a total of 274 articles (published during 2003–2011) were analyzed that were classified as computer science information system related in the Web of Science data base and had at least one social media phenomenon related keyword—social media; social network analysis; social network; social network site; and social network system. As a result, we found four main research streams in SMS research dealing with: (1) organizational aspect of SMS, (2) non-organizational aspect of SMS, (3) technical aspect of SMS, and (4) social as a tool. The results indicates that SMS research is fragmented and has not yet found way into the core IS journals, however, it is diverse and interdisciplinary in nature. We also proposed that unlike the conventional and socio-technical IS where information is bureaucratic, formal, bounded within the intranet, and tightly controlled by organizations; in the SMS context, information is social, informal, boundary-less (i.e. boundary is within the internet), has less control, and more sharing of information may lead to higher value/impact.


Similar content being viewed by others
Notes
Apart from theoretical reasoning provided here, we also provided empirical evidence of the emergence of SMS research area using data collected from the Web of Science database.
SMS, PSMS and OSMS research streams in the information system research are empirically validated using a mixed method in the results section.
References
Ackland, R. (2009). Social network services as data sources and platforms for e-researching social networks. Social Science Computer Review, 27(4), 481–492. doi:10.1177/0894439309332291.
Allen, S. M., Colombo, G., & Whitaker, R. M. (2010). Cooperation through self-similar social networks. ACM Transactions on Autonomous Adaptation of Systems, 5(1), 1–29. doi:10.1145/1671948.1671952.
Alon, N., Feldman, M., Procaccia, A. D., & Tennenholtz, M. (2010). A note on competitive diffusion through social networks. Information Processing Letters, 110(6), 221–225. doi:10.1016/j.ipl.2009.12.009.
Angus, E., Thelwall, M., & Stuart, D. (2008). General patterns of tag usage among university groups in Flickr. Online Information Review, 32(1), Online Information Review, Vol. 32, No. 31. (2008), pp. 2089–2101. Key: citeulike:5070428.
Bächle, M. (2006). Social software. Informatik-Spektrum, 29(2), 121–124.
Baden, R., Bender, A., Spring, N., Bhattacharjee, B., & Starin, D. (2009). Persona: An online social network with user-defined privacy. SIGCOMM Computer Communication Review, 39(4), 135–146. doi:10.1145/1594977.1592585.
Bar-Yossef, Z., Guy, I., Lempel, R., Maarek, Y. S., & Soroka, V. (2006). Cluster ranking with an application to mining mailbox networks. Paper presented at the Proceedings of the Sixth International Conference on Data Mining.
Bertot, J. C., Jaeger, P. T., & Grimes, J. M. (2010). Using ICTs to create a culture of transparency: E-government and social media as openness and anti-corruption tools for societies. Government Information Quarterly, 27(3), 264–271. doi:10.1016/j.giq.2010.03.001.
Bittner, S., & Müller, A. (2011). Social networking tools and research information systems: Do they compete? Webology, 8(1), Article 82.
Bollen, J., Van de Sompel, H., Smith, J. A., & Luce, R. (2005). Toward alternative metrics of journal impact: A comparison of download and citation data. Information Processing and Management, 41(6), 1419–1440. doi:10.1016/j.ipm.2005.03.024.
Bolton, G., Loebbecke, C., & Ockenfels, A. (2008). Does competition promote trust and trustworthiness in online trading? An experimental study. Journal of Management Information Systems, 25(2), 145–170. doi:10.2753/mis0742-1222250207.
Borgatti, S. P. (2002). NetDraw: Graph visualization software. Harvard: Analytic Technologies.
Borgatti, S. P., & Molina, J. L. (2003). Ethical and strategic issues in organizational social network analysis. The Journal of Applied Behavioral Science, 39(3), 337–349.
Bostrom, R., & Heinen, J. S. (1977). MIS problems and failures: A socio-technical perspective. MIS Quarterly, 1(3).
Boyd, D. (2006). The significance of social software (Blogtalks reloaded: social software research & cases). Norderstedt: Books on Demand.
Briggs, R. O., Nunamaker, J., & Sprague, R. (2010). Special section: Social aspects of sociotechnical systems. Journal of Management Information Systems, 27(1), 13–16.
Cai, J. (2006). Knowledge management within collaboration processes: A perspective modeling and analyzing methodology. Journal of Database Management, 17(1), 33–48. doi:10.4018/jdm.2006010103.
Carley, K. M., Diesner, J., Reminga, J., & Tsvetovat, M. (2007). Toward an interoperable dynamic network analysis toolkit. Decision Support Systems, 43(4), 1324–1347. doi:10.1016/j.dss.2006.04.003.
Caverlee, J., Liu, L., & Webb, S. (2010). The SocialTrust framework for trusted social information management: Architecture and algorithms. Information Sciences, 180(1), 95–112. doi:10.1016/j.ins.2009.06.027.
Chi, L., Holsapple, C. W., & Srinivasan, C. (2008). Digital systems, partnership networks, and competition: The co-evolution of IOS use and network position as antecedents of competitive action. Journal of Organizational Computing and Electronic Commerce, 18(1), 61–94. doi:10.1080/10919390701807350.
Chi, Z., Jinyuan, S., Xiaoyan, Z., & Yuguang, F. (2010). Privacy and security for online social networks: Challenges and opportunities. Network, IEEE, 24(4), 13–18.
Chow, W. S., & Chan, L. S. (2008). Social network, social trust and shared goals in organizational knowledge sharing. Information & Management, 45(7), 458–465. doi:10.1016/j.im.2008.06.007.
Chun, S. A., Shulman, S., & Sandoval, A. R. (2010). Government 2.0: Marking connections between citizens, data and government. Information Polity, 15(1–2), 1–9.
Cox, A. M. (2008). An exploration of concepts of community through a case study of UK university web production. Journal of Information Science, 34(3), 327–345. doi:10.1177/0165551507084354.
Davenport, T. (2005). Thinking for a living. Boston: Harvard University Press.
Dean, D. L., Lowry, P. B., & Humpherys, S. (2011). Profiling the research productivity of tenured information systems faculty at U.S. institutions. MIS Quarterly, 35(1), 1–15.
DiMicco, J., Millen, D. R., Geyer, W., Dugan, C., Brownholtz, B., & Muller, M. (2008). Motivations for social networking at work. Paper presented at the Proceedings of the 2008 ACM conference on Computer supported cooperative work, San Diego, CA, USA.
Dustdar, S., & Hoffmann, T. (2007). Interaction pattern detection in process oriented information systems. Data & Knowledge Engineering, 62(1), 138–155. doi:10.1016/j.datak.2006.07.010.
Dwivedi, Y., Lal, B., Mustafee, N., & Williams, M. (2009). Profiling a decade of Information Systems Frontiers’ research. Information Systems Frontiers, 11(1), 87–102. doi:10.1007/s10796-008-9147-7.
Fu, T. J., Abbasi, A., & Chen, H. C. (2008). A hybrid approach to web forum interactional coherence analysis. Journal of the American Society for Information Science and Technology, 59(8), 1195–1209. doi:10.1002/asi.20827.
Ganley, D., & Lampe, C. (2009). The ties that bind: Social network principles in online communities. Decision Support Systems, 47(3), 266–274. doi:10.1016/j.dss.2009.02.013.
Gewin, V. (2010). Collaboration: Social networking seeks critical mass. Nature, 468(7326), 993–994.
Golbeck, J. (2009). Trust and nuanced profile similarity in online social networks. ACM Transactions on Web, 3(4), 1–33. doi:10.1145/1594173.1594174.
Granovetter, M. (1983). The strength of weak ties: A network theory revisited. Sociological Theory, 1(201), 201–233. doi:10.2307/202051.
Grönlund, Å. (2004). State of the art in e-Gov research—A survey electronic government. In R. Traunmüller (Ed.), Lecture Notes in Computer Science, Vol. 3183 (pp. 178–185). Berlin: Springer.
Guo, J., & Gong, Z. (2011). Measuring virtual wealth in virtual worlds. Information Technology and Management, 12(2), 121–135. doi:10.1007/s10799-011-0082-9.
Guo, H., Weingart, S., & Börner, K. (2011). Mixed-indicators model for identifying emerging research areas. Scientometrics, 89(1), 421–435. doi:10.1007/s11192-011-0433-7.
Hansen, D., Shneiderman, B., & Smith, M. A. (2010). Analyzing social media networks with NodeXL: Insights from a connected world. Massachusetts: Morgan Kaufmann.
Hester, A. (2011). A comparative analysis of the usage and infusion of wiki and non-wiki-based knowledge management systems. Information Technology and Management, 12(4), 335–355. doi:10.1007/s10799-010-0079-9.
Highfield, T., Kirchhoff, L., & Nicolai, T. (2011). Challenges of tracking topical discussion networks online. Social Science Computer Review, 29(3), 340–353. doi:10.1177/0894439310382514.
Hou, H., Kretschmer, H., & Liu, Z. (2008). The structure of scientific collaboration networks in Scientometrics. Scientometrics, 75(2), 189–202. doi:10.1007/s11192-007-1771-3.
Hsiao, K.-L. (2011). Why internet users are willing to pay for social networking services. Online Information Review, 35(5), 770–788.
Hu, D. N., Kaza, S., & Chen, H. C. (2009). Identifying significant facilitators of dark network evolution. Journal of the American Society for Information Science and Technology, 60(4), 655–665. doi:10.1002/asi.21008.
Hwang, Y.-C., & Yuan, S.-T. (2009). Ubiquitous proximity e-service for trust collaboration. Internet Research, 19(2), 174–193.
Ji, S., Min, Q., & Han, W. (2007). Research in information systems in China (1999–2005) and international comparisons. Frontiers of Business Research in China, 1(1), 19–38. doi:10.1007/s11782-007-0002-3.
Jin, Y., Ishizuka, M., & Matsuo, Y. (2008). Extracting inter-firm networks from the World Wide Web using a general-purpose search engine. Online Information Review, 32(2), 196–210.
Johnson, B., & Oppenheim, C. (2007). How socially connected are citers to those that they cite? Journal of Documentation, 63(5), 609–637.
Juste, P. S., Wolinsky, D., Boykin, P. O., Covington, M. J., & Figueiredo, R. J. (2010). SocialVPN: Enabling wide-area collaboration with integrated social and overlay networks. Computer Networks, 54(12), 1926–1938. doi:10.1016/j.comnet.2009.11.019.
Kaplan, A. M., & Haenlein, M. (2010). Users of the world, unite! The challenges and opportunities of Social Media. Business Horizons, 53(1), 59–68. doi:10.1016/j.bushor.2009.09.003.
Khan, G. F., Moon, J., & Park, H. W. (2012). Network of the core: Mapping and visualizing the core of scientific domains. Scientometrics, 89(3), 759–779. doi:10.1007/s11192-011-0489-4.
Khan, G. F., Moon, J., Park, H. W., Swar, B., & Rho, J. (2011). A socio-technical perspective on e-government issues in developing countries: A scientometrics approach. Scientometrics, 87(2), 267–286. doi:10.1007/s11192-010-0322-5.
Khan, G. F., & Park, H. W. (2011). International collaboration within e-government domain: A scientometrics analysis. Paper presented at the KAPA-ASPA International Conference, Seoul, South Korea, October 28–29, 2011.
Kilduff, M., & Brass, D. J. (2010). Organizational social network research: Core ideas and key debates. In J. P. Walsh & A. P. Brief (Eds.), Academy of management annuals, Vol. 4 (pp. 317–357). London: Routledge.
Kitchenham, B., Pearl Brereton, O., Budgen, D., Turner, M., Bailey, J., & Linkman, S. (2009). Systematic literature reviews in software engineering—A systematic literature review. Information and Software Technology, 51(1), 7–15. doi:10.1016/j.infsof.2008.09.009.
Korfiatis, N. T., Poulos, M., & Bokos, G. (2006). Evaluating authoritative sources using social networks: An insight from Wikipedia. Online Information Review, 30(3), 252–262.
Kretschmer, H., & Aguillo, I. F. (2005). New indicators for gender studies in Web networks. Information Processing and Management, 41(6), 1481–1494. doi:10.1016/j.ipm.2005.03.009.
Lassen, D. S., & Brown, A. R. (2011). Twitter: The electoral connection? Social Science Computer Review, 29(4), 419–436. doi:10.1177/0894439310382749.
Lee, W. (2008). How to identify emerging research fields using scientometrics: An example in the field of Information Security. Scientometrics, 76(3), 503–525. doi:10.1007/s11192-007-1898-2.
Lee, B., & Jeong, Y.-I. (2008). Mapping Korea’s national R&D domain of robot technology by using the co-word analysis. Scientometrics, 77(1), 3–19. doi:10.1007/s11192-007-1819-4.
Lee, D., Park, J. Y., Kim, J., Kim, J., & Moon, J. (2011). Understanding music sharing behaviour on social network services. Online Information Review, 35(5), 716–733.
Leydesdorff, L. (2003). The mutual information of university-industry-government relations: An indicator of the Triple Helix dynamics. Scientometrics, 58(2), 445–467. doi:10.1023/a:1026253130577.
Leydesdorff, L. (2004a). Clusters and maps of science journals based on bi-connected graphs in Journal Citation Reports. Journal of Documentation, 60(4), 371–427. doi:10.1108/00220410410548144.
Leydesdorff, L. (2004b). Top-down decomposition of the Journal Citation Report of the Social Science Citation Index: Graph- and factor-analytical approaches. Scientometrics, 60(2), 159–180. doi:10.1023/B:SCIE.0000027678.31097.e0.
Leydesdorff, L. (2007). Betweenness centrality as an indicator of the interdisciplinarity of scientific journals. Journal of the American Society for Information Science and Technology, 58(9), 1303–1319. doi:10.1002/asi.20614.
Leydesdorff, L. (2009). How are new citation-based journal indicators adding to the bibliometric toolbox? Journal of the American Society for Information Science and Technology, 60(7), 1327–1336. doi:10.1002/asi.21024.
Leydesdorff, L., & Vaughan, L. (2006). Co-occurrence matrices and their applications in information science: Extending ACA to the Web environment. Journal of the American Society for Information Science and Technology, 57(12), 1616–1628. doi:10.1002/asi.20335.
Li, Y.-M., Lin, C.-H., & Lai, C.-Y. (2010). Identifying influential reviewers for word-of-mouth marketing. Electronic Commerce Research and Applications, 9(4), 294–304. doi:10.1016/j.elerap.2010.02.004.
Liang, X., Lu, R., Chen, L., Lin, X., & Shen, X. S. (2011). PEC: A privacy-preserving emergency call scheme for mobile healthcare social networks. Journal of Communications and Networks, 13(2), 102–112.
Li-chun, Y., Kretschmer, H., Hanneman, R. A., & Ze-yuan, L. (2006). Connection and stratification in research collaboration: An analysis of the COLLNET network. Information Processing and Management, 42(6), 1599–1613. doi:10.1016/j.ipm.2006.03.021.
Lin, F.-L., & Chiou, G.-F. (2010). Prestige as an indicator of knowledge exchange in the community of school technology coordinators. Online Information Review, 34(1), 5–20.
Lin, T.-C., & Huang, C.-C. (2009). Understanding the determinants of EKR usage from social, technological and personal perspectives. Journal of Information Science, 35(2), 165–179. doi:10.1177/0165551508095780.
Liu, X., Bollen, J., Nelson, M. L., & Van de Sompel, H. (2005). Co-authorship networks in the digital library research community. Information Processing and Management, 41(6), 1462–1480. doi:10.1016/j.ipm.2005.03.012.
Liu, X., Kaza, S., Zhang, P. Z., & Chen, H. C. (2011). Determining inventor status and its effect on knowledge diffusion: A study on nanotechnology literature from China, Russia, and India. Journal of the American Society for Information Science and Technology, 62(6), 1166–1176. doi:10.1002/asi.21528.
Liu, H., Maes, P., & Davenport, G. (2006). Unraveling the taste fabric of social networks. International Journal on Semantic Web and Information Systems, 2(1), 42–71. doi:citeulike-article-id:1080440.
Long, Y., & Siau, K. (2007). Social network structures in open source software development teams. Journal of Database Management, 18(2), 25–40. doi:10.4018/jdm.2007040102.
Lucio-Arias, D., & Leydesdorff, L. (2008). Main-path analysis and path-dependent transitions in HistCite (TM)-based historiograms. Journal of the American Society for Information Science and Technology, 59(12), 1948–1962. doi:10.1002/asi.20903.
Mackenzie, M. L. (2003). Information gathering revealed within the social network of line-managers. Proceedings of the American Society for Information Science and Technology, 40(1), 85–94. doi:10.1002/meet.1450400111.
Maicas, J. P., Polo, Y., & Sese, F. J. (2009). The role of (personal) network effects and switching costs in determining mobile users’ choice. Journal of Information Technology, 24, 160–171. doi:10.1057/jit.2008.35.
Malin, B., & Carley, K. (2007). A longitudinal social network analysis of the editorial boards of medical informatics and bioinformatics journals. Journal of the American Medical Informatics Association, 14(3), 340–348.
Massa, P., & Avesani, P. (2007). Trust metrics on controversial users: Balancing between Tyranny of the majority. International Journal on Semantic Web and Information Systems, 3(1), 39–64. doi:10.4018/jswis.2007010103.
Massari, L. (2010). Analysis of MySpace user profiles. Information Systems Frontiers, 12(4), 361–367. doi:10.1007/s10796-009-9206-8.
McAfee, A. (2006a). Enterprise 2.0: The dawn of emergent collaboration. MIT Sloan Management Review, 47(3), 21–28.
McAfee, A. (2006b). Enterprise 2.0: The dawn of emergent collaboration. MIT Sloan Management Review, 47(3), 21–28.
Mitra, S., Bagchi, A., & Bandyopadhyay, A. (2007). Design of a data model for social network applications. Journal of Database Management, 18(4), 51–79. doi:10.4018/jdm.2007100103.
Moturu, S. T., & Liu, H. (2011). Quantifying the trustworthiness of social media content. Distrib Parallel Databases. doi:10.1007/s10619-010-7077-0.
Nagpaul, P. (2002). Visualizing cooperation networks of elite institutions in India. Scientometrics, 54(2), 213–228. doi:10.1023/a:1016036711279.
Nanavati, A. A., Singh, R., Chakraborty, D., Dasgupta, K., Mukherjea, S., Das, G., et al. (2008). Analyzing the structure and evolution of massive telecom graphs. IEEE Transactions on Knowledge and Data Engineering, 20(5), 703–718. doi:10.1109/tkde.2007.190733.
Oh, W., Choi, J. N., & Kim, K. (2006). Coauthorship dynamics and knowledge capital: The patterns of cross-disciplinary collaboration in information systems research. Journal of Management Information Systems, 22(3), 265–292.
Olmeda-Gómez, C., Perianes-Rodriguez, A., Ovalle-Perandones, M. A., Guerrero-Bote, V. P., & Anegón, Fd. M. (2009). Visualization of scientific co-authorship in Spanish universities: From regionalization to internationalization. Aslib Proceedings: New Information Perspectives, 61(1), 83–100.
Omran, E. E., & Etten, Jv. (2007). Spatial-data sharing: Applying social-network analysis to study individual and collective behaviour. International Journal of Geographical Information Science, 21(6), 699–714. doi:10.1080/13658810601135726.
Park, H. W., & Leydesdorff, L. (2010). Longitudinal trends in networks of university-industry-government relations in South Korea: The role of programmatic incentives. Research Policy, 39(5), 640–649. doi:10.1016/j.respol.2010.02.009.
Retzer, S., Yoong, P., & Hooper, V. (2010). Inter-organisational knowledge transfer in social networks: A definition of intermediate ties. Information Systems Frontiers, 1–19, doi:10.1007/s10796-010-9250-4.
Richter, D., Riemer, K., & vom Brocke, J. (2011). Internet social networking research state of the art and implications for enterprise 20. Business & Information Systems Engineering, 3(2), 89–101. doi:10.1007/s12599-011-0151-y.
Rodriguez, M. A., Bollen, J., & Sompel, H. V. D. (2006). The convergence of digital libraries and the peer-review process. Journal of Information Science, 32(2), 149–159. doi:10.1177/0165551506062327.
Sæbo, O., Rose, J., & Skiftenes Flak, L. (2008). The shape of eParticipation: Characterizing an emerging research area. Government Information Quarterly, 25(3), 400–428. doi:10.1016/j.giq.2007.04.007.
Sci2Team. (2009). Science of Science (Sci2) Tool. Indiana University and SciTech Strategies. http://sci2.cns.iu.edu. Accessed 20 Sept. 2011.
Shapira, B., & Zabar, B. (2011). Personalized search: Integrating collaboration and social networks. Journal of the American Society for Information Science and Technology, 62(1), 146–160. doi:10.1002/asi.21446.
Shekarpour, S., & Katebi, S. D. (2010). Modeling and evaluation of trust with an extension in semantic web. Web Semantics, 8(1), 26–36. doi:10.1016/j.websem.2009.11.003.
Shin, S. K., Ishman, M., & Sanders, G. L. (2007). An empirical investigation of socio-cultural factors of information sharing in China. Information & Management, 44(2), 165–174. doi:10.1016/j.im.2006.11.004.
Shin, J. C., Lee, S. J., & Kim, Y. (2012). Knowledge-based innovation and collaboration: a triple-helix approach in Saudi Arabia. Scientometrics, 90(1), 311–326. doi:10.1007/s11192-011-0518-3
Sinclaire, J., & Vogus, C. (2011). Adoption of social networking sites: An exploratory adaptive structuration perspective for global organizations. Information Technology and Management, 12(4), 293–314. doi:10.1007/s10799-011-0086-5.
Sledgianowski, D., & Kulviwat, S. (2009). Using social network sites: The effets of playfulness, critical mass and trust in a hedonic context. Journal of Computer Information Systems, 49(4), 74–83.
Sowe, S., Stamelos, I., & Angelis, L. (2006). Identifying knowledge brokers that yield software engineering knowledge in OSS projects. Information and Software Technology, 48(11), 1025–1033. doi:10.1016/j.infsof.2005.12.019.
Squicciarini, A. C., Shehab, M., & Wede, J. (2010). Privacy policies for shared content in social network sites. The VLDB Journal, 19(6), 777–796. doi:10.1007/s00778-010-0193-7.
Squicciarini, A., & Sundareswaran, S. (2009). Web-traveler policies for images on social networks. World Wide Web, 12(4), 461–484. doi:10.1007/s11280-009-0070-8.
Squicciarini, A. C., Xu, H., & Zhang, X. (2011). CoPE: Enabling collaborative privacy management in online social networks. Journal of the American Society for Information Science and Technology, 62(3), 521–534. doi:10.1002/asi.21473.
Steinfield, C., DiMicco, J., Ellison, N., & Lampe, C. (2009). Bowling online: Social networking and social capital within the organization. Paper presented at the Proc fourth international conference on communities and technologies, University Park.
Suh, A., & Shin, K.-S. (2010). Exploring the effects of online social ties on knowledge sharing: A comparative analysis of collocated vs. dispersed teams. J. Inf. Sci., 36(4), 443–463. doi:10.1177/0165551510369632.
Teng, J. T. C., & Galletta, D. F. (1991). Mis research directions: A survey of researchers’ views. SIGMIS Database, 22(1–2), 53–62. doi:10.1145/110790.110804.
Thelwall, M. (2008). No place for news in social network web sites? Online Information Review, 32(6), 726–744. doi:10.1108/14684520810923908.
Thelwall, M. (2009a). Homophily in MySpace. Journal of the American Society for Information Science and Technology, 60(2), 219–231. doi:10.1002/asi.20978.
Thelwall, M. (2009b). MySpace comments. Online Information Review, 33(1), 58–76.
Thelwall, M., Buckley, K., Paltoglou, G., Cai, D., & Kappas, A. (2010a). Sentiment in short strength detection informal text. Journal of the American Society for Information Science and Technology, 61(12), 2544–2558. doi:10.1002/asi.21416.
Thelwall, M., Wilkinson, D., & Uppal, S. (2010b). Data mining emotion in social network communication: Gender differences in MySpace. Journal of the American Society for Information Science and Technology, 61(1), 190–199. doi:10.1002/asi.21180.
Truex, D., Cuellar, M., Takeda, H., & Vidgen, R. (2011). The scholarly influence of Heinz Klein: Ideational and social measures of his impact on IS research and IS scholars. European Journal of Information Systems, 20, 422–439.
Vogel, D. R., & Wetherbe, J. C. (1984). MIS research: A profile of leading journals and universities. SIGMIS Database, 16(1), 3–14. doi:10.1145/1113511.1113512.
Wang, F.-Y., Carley, K. M., Zeng, D., & Mao, W. (2007). Social computing: From social informatics to social intelligence. IEEE Intelligent Systems, 22(2), 79–83.
Wang, J.-C., & Chen, C.-L. (2004). An automated tool for managing interactions in virtual communities-using social network analysis approach. Journal of Organizational Computing and Electronic Commerce, 14(1), 1–26. doi:10.1207/s15327744joce1401_1.
Wang, J.-C., & Chiang, M.-J. (2009). Social interaction and continuance intention in online auctions: A social capital perspective. Decision Support Systems, 47(4), 466–476. doi:10.1016/j.dss.2009.04.013.
Wang, J.-C., Chiang, C.-h., & Lin, S.-W. (2010). Network structure of innovation: Can brokerage or closure predict patent quality? Scientometrics, 84(3), 735–748. doi:10.1007/s11192-010-0211-y.
Wasko, M. M., Teigland, R., & Faraj, S. (2009). The provision of online public goods: Examining social structure in an electronic network of practice. Decision Support Systems, 47(3), 254–265. doi:10.1016/j.dss.2009.02.012.
Wasserman, S., & Faust, K. (1994). Social network analysis: Methods and applications. Cambridge: Cambridge University Press.
Webster, J., & Watson, R. T. (2002). Analyzing the past to prepare for the future: writing a literature review. MIS Quarterly, 26(2), xiii–xxiii.
Widén-Wulff, G., Ek, S., Ginman, M., Perttilä, R., Södergård, P., & Tötterman, A.-K. (2008). Information behaviour meets social capital: A conceptual model. Journal of Information Science, 34(3), 346–355. doi:10.1177/0165551507084679.
Xu, J. J., & Chen, H. C. (2005). CrimeNet explorer: A framework for criminal network knowledge discovery. ACM Transactions on Information Systems, 23(2), 201–226. doi:10.1145/1059981.1059984.
Yang, M., Kiang, M., Chen, H. C., & Li, Y. J. (2012). Artificial immune system for illicit content identification in social media. Journal of the American Society for Information Science and Technology, 63(2), 256–269. doi:10.1002/asi.21673.
Yang, H.-L., & Tang, J.-H. (2004). Team structure and team performance in IS development: A social network perspective. Information Management, 41(3), 335–349. doi:10.1016/s0378-7206(03)00078-8.
Yeh, N.-C., Lin, J. C.-C., & Lu, H.-P. (2011). The moderating effect of social roles on user behaviour in virtual worlds. Online Information Review, 35(5), 747–769.
Yu, H., Kaminsky, M., Gibbons, P. B., & Flaxman, A. (2006). SybilGuard: Defending against sybil attacks via social networks. SIGCOMM Computer Communications Review, 36(4), 267–278. doi:10.1145/1151659.1159945.
Zac, S., & David, S. (2011). WhiteScript: Using social network analysis parameters to balance between browser usability and malware exposure. Computers & Security, 30(1), 4–12.
Zhou, B., & Pei, J. (2011). The k-anonymity and l-diversity approaches for privacy preservation in social networks against neighborhood attacks. Knowledge and Information Systems, 28(1), 47–77. doi:10.1007/s10115-010-0311-2.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Khan, G.F. Social media-based systems: an emerging area of information systems research and practice. Scientometrics 95, 159–180 (2013). https://doi.org/10.1007/s11192-012-0831-5
Received:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11192-012-0831-5