Abstract
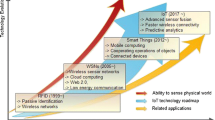
Internet of Things (IoT), as an emerging technology, describes a smart world that enables objects to interact with each other and with end-users through developed communication platforms such as the Internet. The limited communication range of things allows packets to be transmitted between objects that are not in each other's range through intermediate objects, which highlights the necessity of routing in this technology. Therefore, the Quality of Service parameters of IoT entirely depend on the cooperation of things in the routing process. Several factors such as energy depletion, conquering objects by an enemy, and resource constraints lead to selfish behavior that may cause network collapse. In this paper, a new watchdog-based identification method is presented to diagnosis selfish objects in the Internet of Things, in which the selected watchdogs are responsible for evaluating the activity of other objects. In the proposed method to achieve a uniform distribution of watchdog objects in the network, the IoT objects are partitioned into disjoint cells using the Voronoi diagram, and a watchdog is selected for each cell. In this way, while the supervision overhead is distributed, the watchdog objects can identify the selfish things through examining the remaining energy and cooperation degree of other objects. The conducted simulations in the MATLAB tool have validated the effectiveness of the proposed method in terms of detection rate, false-positive rate, throughput, end-to-end delay, and energy consumption.







Similar content being viewed by others
Data availability
Not applicable.
Code availability
Not applicable.
References
Azad P, Navimipour NJ, Rahmani AM, Sharifi A (2020) The role of structured and unstructured data managing mechanisms in the Internet of things. Cluster Comput 23:1185–1198. https://doi.org/10.1007/s10586-019-02986-2
Sharma S, Verma VK (2021) Security explorations for routing attacks in low power networks on internet of things. J Supercomput 77:4778–4812. https://doi.org/10.1007/s11227-020-03471-z
de Oliveira Júnior WG, de Oliveira JM, Munoz R, de Albuquerque VHC (2020) A proposal for Internet of Smart Home Things based on BCI system to aid patients with amyotrophic lateral sclerosis. Neural Comput Appl 32:11007–11017. https://doi.org/10.1007/s00521-018-3820-7
Idwan S, Mahmood I, Zubairi JA, Matar I (2020) Optimal management of solid waste in smart cities using Internet of Things. Wirel Pers Commun 110:485–501. https://doi.org/10.1007/s11277-019-06738-8
Choudhary G, Sharma V, You I (2019) Sustainable and secure trajectories for the military Internet of Drones (IoD) through an efficient Medium Access Control (MAC) protocol. Comput Electr Eng 74:59–73. https://doi.org/10.1016/J.COMPELECENG.2019.01.007
Zhang Y, Wen J (2017) The IoT electric business model: Using blockchain technology for the internet of things. Peer-to-Peer Netw Appl 10:983–994. https://doi.org/10.1007/s12083-016-0456-1
Balaji S, Nathani K, Santhakumar R (2019) IoT technology, applications and challenges: a contemporary survey. Wirel Pers Commun 108:363–388. https://doi.org/10.1007/s11277-019-06407-w
Stoyanova M, Nikoloudakis Y, Panagiotakis S et al (2020) A Survey on the Internet of Things (IoT) forensics: challenges, approaches, and open issues. IEEE Commun Surv Tutorials 22:1191–1221. https://doi.org/10.1109/COMST.2019.2962586
Hail MAM, Amadeo M, Molinaro A, Fischer S (2015) On the performance of caching and forwarding in information-centric networking for the IoT. In: Lecture Notes in Computer Science. Springer Verlag, pp 313–326
Anagnostopoulos T, Zaslavsky A, Kolomvatsos K et al (2017) Challenges and opportunities of waste management in IoT-enabled smart cities: a survey. IEEE Trans Sustain Comput 2:275–289. https://doi.org/10.1109/TSUSC.2017.2691049
Varjovi AE, Babaie S (2020) Green Internet of Things (GIoT): vision, applications and research challenges. Sustain Comput Informatics Syst. https://doi.org/10.1016/J.SUSCOM.2020.100448
Gharamaleki MM, Babaie S (2020) A new distributed fault detection method for wireless sensor networks. IEEE Syst J 14:4883–4890. https://doi.org/10.1109/JSYST.2020.2976827
Jedari B, Xia F, Chen H et al (2019) A social-based watchdog system to detect selfish nodes in opportunistic mobile networks. Futur Gener Comput Syst 92:777–788. https://doi.org/10.1016/j.future.2017.10.049
Hasani H, Babaie S (2019) Selfish node detection in ad hoc networks based on fuzzy logic. Neural Comput Appl 31:6079–6090. https://doi.org/10.1007/s00521-018-3431-3
Gomathy V, Padhy N, Samanta D et al (2020) Malicious node detection using heterogeneous cluster based secure routing protocol (HCBS) in wireless adhoc sensor networks. J Ambient Intell Humaniz Comput. https://doi.org/10.1007/s12652-020-01797-3
Liu L, Ma Z, Meng W (2019) Detection of multiple-mix-attack malicious nodes using perceptron-based trust in IoT networks. Futur Gener Comput Syst 101:865–879. https://doi.org/10.1016/j.future.2019.07.021
Rama Abirami K, Sumithra MG (2019) Evaluation of neighbor credit value based AODV routing algorithms for selfish node behavior detection. Cluster Comput 22:13307–13316. https://doi.org/10.1007/s10586-018-1851-6
Zhang C, Ge J, Gong F et al (2020) Security-reliability tradeoff for untrusted and selfish relay-assisted D2D communications in heterogeneous cellular networks for IoT. IEEE Syst J 14:2192–2201. https://doi.org/10.1109/JSYST.2019.2925033
Zhao R, Wang Y, Xiao G et al (2021) A selfish herd optimization algorithm based on the simplex method for clustering analysis. J Supercomput. https://doi.org/10.1007/s11227-020-03597-0
Raju S, Chandrasekaran M (2019) An improved neighbor cooperation using adjacent node cooperation in peer to peer networks. Cluster Comput 22:12263–12274. https://doi.org/10.1007/s10586-017-1607-8
Nobahary S, Babaie S (2018) A credit-based method to selfish node detection in mobile ad-hoc network. Appl Comput Syst 23:118–127. https://doi.org/10.2478/acss-2018-0015
Ullah N, Kong X, Lin L et al (2020) Real-time dissemination of emergency warning messages in 5G enabled selfish vehicular social networks. Comput Networks 182:107482. https://doi.org/10.1016/J.COMNET.2020.107482
Ponnusamy M et al (2021) Detection of selfish nodes through reputation model in mobile adhoc network—MANET. Turk J Comput Math Educ 12:2404–2410. https://doi.org/10.17762/TURCOMAT.V12I9.3720
Esmailifar S, Saghafi F (2015) Moving target localization by cooperation of multiple flying vehicles. IEEE Trans Aerosp Electron Syst 51:739–746. https://doi.org/10.1109/TAES.2014.130168
Ying T, Feng W, Su W, Jiang W (2017) On the degrees of freedom of MIMO X networks with non-cooperation transmitters. IEEE Trans Wirel Commun 16:2490–2504. https://doi.org/10.1109/TWC.2017.2665544
Shang F, Niu X, He D et al (2020) Resource allocation and admission control algorithm based on non-cooperation game in wireless mesh networks. Comput Commun 152:63–71. https://doi.org/10.1016/J.COMCOM.2020.01.009
Sharma A, Goyal N, Guleria K (2021) Performance optimization in delay tolerant networks using backtracking algorithm for fully credits distribution to contrast selfish nodes. J Supercomput 77:6036–6055. https://doi.org/10.1007/s11227-020-03507-4
Socievole A, Caputo A, De Rango F, Fazio P (2019) Routing in mobile opportunistic social networks with selfish nodes. Wirel Commun Mob Comput 2019:1–15. https://doi.org/10.1155/2019/6359806
Razaque A, Abdulghafour M, Khan MJ (2017) Detection of selfish attack over wireless body area networks. In: 2017 IEEE Conference on Open Systems. IEEE, pp 48–52
Hilal AE, MacKenzie AB (2019) A distributed coalition game model for cooperation in MANETs. Ad Hoc Netw 85:46–59. https://doi.org/10.1016/J.ADHOC.2018.10.019
Sharma A, Goyal N, Guleria K (2020) Performance optimization in delay tolerant networks using backtracking algorithm for fully credits distribution to contrast selfish nodes. J Supercomput. https://doi.org/10.1007/s11227-020-03507-4
Jain S, Verma A (2019) Bubble rap incentive scheme for prevention of node selfishness in delay-tolerant networks. In: Advances in Intelligent Systems and Computing. Springer, Singapore, pp 289–303
Wang H, Wang H, Guo F et al (2018) ARAG: a routing algorithm based on incentive mechanisms for DTN with nodes’ selfishness. IEEE Access 6:29419–29425. https://doi.org/10.1109/ACCESS.2018.2834912
Jesudoss A, Raja SVK, Sulaiman A (2015) Stimulating truth-telling and cooperation among nodes in VANETs through payment and punishment scheme. Ad Hoc Netw 24:250–263. https://doi.org/10.1016/j.adhoc.2014.08.018
Sun Y, Guo Y, Ge Y et al (2013) Improving the transmission efficiency by considering non-cooperation in ad hoc networks. Comput J 56:1034–1042. https://doi.org/10.1093/comjnl/bxt042
Zhang W, Zhu S, Tang J, Xiong N (2018) A novel trust management scheme based on Dempster–Shafer evidence theory for malicious nodes detection in wireless sensor networks. J Supercomput 74:1779–1801. https://doi.org/10.1007/s11227-017-2150-3
Nobahary S, Garakani HG, Khademzadeh A, Rahmani AM (2019) Selfish node detection based on hierarchical game theory in IoT. Eurasip J Wirel Commun Netw. https://doi.org/10.1186/s13638-019-1564-4
Li J, Gao X, Yang Q et al (2018) Neural-network aided dynamic control for delivering media streams in selfish wireless networks with unknown node-selfishness. IEEE Access 6:31759–31771. https://doi.org/10.1109/ACCESS.2018.2833210
Funding
Funding information is not applicable/no funding was received.
Author information
Authors and Affiliations
Contributions
SB helped in conceptualization, methodology, validation, writing—review & editing, supervision. NR was involved in searching, writing—original draft, simulation.
Corresponding author
Ethics declarations
Conflict of interest
All authors have participated in (a) conception and design, or analysis and interpretation of the data; (b) drafting the article or revising it critically for important intellectual content; and (c) approval of the final version. This manuscript has not been submitted to, nor is under review at, another journal or other publishing venue. The following authors have affiliations with organizations with direct or indirect financial interest in the subject matter discussed in the manuscript:
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Razzaghi, N., Babaie, S. A new selfish thing detection method based on Voronoi diagram for Internet of Things. J Supercomput 78, 8389–8408 (2022). https://doi.org/10.1007/s11227-021-04202-8
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11227-021-04202-8