Abstract
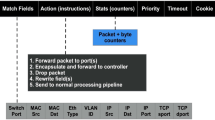
Currently, the Internet of Thing has become an integral part of the world's Internet infrastructure. One of the important matters in this field is the security of the network. Some networks like Software-defined Networking are proposed to improve it. In this paper, cyber-attacks have been simulated and various parameters such as the average rate of receiving traffic, the average response time and network delay have been analyzed. In the following, a new plan for switch buffers and their effect on the state of CPU performance, the controller bandwidth and the amount of packet loss have been discussed. The new buffer structure is proposed using a hash table, which uses a DRAM combination structure. To implement the proposed technique, AS5710-54X-EC switch and floodlight controller were used, and also Eclipse Neon 3.1 was used for writing modules. The results imply that this method had a great impact on detecting attacks in SDN-based IoT frameworks.













Similar content being viewed by others
Data and materials availability
This declaration is “Not applicable”.
References
Laghari AA, Wu K, Laghari RA, Ali M, Khan AA (2021) A review and state of art of Internet of Things (IoT). Arch Comput Methods Eng. https://doi.org/10.1007/s11831-021-09622-6
Shah Y, Sengupta S (2020, October). A Survey On Classification of Cyber-Attacks on IoT and IIoT Devices. In: 2020 11th IEEE Annual Ubiquitous Computing, Electronics & Mobile Communication Conference (UEMCON) (pp. 0406–0413). IEEE
Priyadarsini M, Bera P (2021) Software defined networking architecture, traffic management, security, and placement: a survey. Comput Netw 192:108047
Wazirali R, Ahmad R, Alhiyari S (2021) SDN-openflow topology discovery: an overview of performance issues. Appl Sci 11(15):6999
Yu H, Qi H, Li K (2020) WECAN: an efficient west-east control associated network for large-scale SDN systems. Mobile Netw Appl 25:114–124
Echeverría A, Cevallos C, Ortiz-Garces I, Andrade RO (2021) Cybersecurity model based on hardening for secure internet of things implementation. Appl Sci 11(7):3260
Manogaran G, Baabdullah T, Rawat DB, Shakeel PM (2021) AI assisted service virtualization and flow management framework for 6G-enabled cloud-software-defined network based IoT. IEEE Internet Things J 9(16):14644–14654
Chen YW, Sheu JP, Kuo YC, Van Cuong N (2020, June) Design and Implementation of IoT DDoS Attacks Detection System Based on Machine Learning. In: 2020 European Conference on Networks and Communications (EuCNC) (pp. 122–127). IEEE
Yin D, Zhang L, Yang K (2018) A DDoS attack detection and mitigation with software-defined internet of things framework. IEEE Access 6:24694–24705
Li J, Liu M, Xue Z, Fan X, He X (2020) RTVD: a real-time volumetric detection scheme for DDoS in the internet of things. IEEE Access 8:36191–36201
Bhayo J, Jafaq R, Ahmed A, Hameed S, Shah SA (2021) A time-efficient approach toward DDoS attack detection in IoT network using SDN. IEEE Internet Things J 9(5):3612–3630
Moudoud H, Khoukhi L, Cherkaoui S (2020) Prediction and detection of fdia and ddos attacks in 5g enabled IoT. IEEE Network 35(2):194–201
Gupta BB, Chaudhary P, Chang X, Nedjah N (2022) Smart defense against distributed denial of service attack in IoT networks using supervised learning classifiers. Comput Electr Eng 98:107726
Almaraz-Rivera JG, Perez-Diaz JA, Cantoral-Ceballos JA (2022) Transport and application layer DDoS attacks detection to IoT devices by using machine learning and deep learning models. Sensors 22(9):3367
Kumar P, Bagga H, Netam BS, Uduthalapally V (2022) Sad-IoT: Security analysis of ddos attacks in IoT networks. Wireless Pers Commun 122(1):87–108
Negera WG, Schwenker F, Debelee TG, Melaku HM, Ayano YM (2022) Review of botnet attack detection in SDN-enabled IoT Using machine learning. Sensors 22(24):9837
Kandoi R, Antikainen M (2015, May) Denial-of-Service Attacks in OpenFlow SDN Networks. In: 2015 IFIP/IEEE International Symposium on Integrated Network Management (IM) (pp. 1322–1326). IEEE
Adeniji OD, Adekeye DB, Ajagbe SA, Adesina AO, Oguns YJ, Oladipupo MA (2023) Development of DDoS attack detection approach in software defined network using support vector machine classifier. In: Ranganathan G, Bestak R, Fernando X (eds) Pervasive computing and social networking. Springer, Singapore, pp 319–331
Ono D, Guillen L, Izumi S, Abe T, Suganuma T (2021) A proposal of port scan detection method based on packet-in messages in OpenFlow networks and its evaluation. Int J Netw Manage 31(6):e2174
Yu H, Li K, Qi H (2019) An active controller selection scheme for minimizing packet-in processing latency in sdn. Secur Commun Netw 2019:1–11
Yue M, Yan Q, Zheng H, Wu Z (2022) Cross-plane DDoS attack defense architecture based on flow table features in SDN. Secur Commun Netw. https://doi.org/10.1155/2022/7409083
Ethilu T, Sathappan A, Rodrigues P (2023) Improving performance and efficiency of software-defined networking by identifying malicious switches through deep learning model
Brahmanand SH, Lal ND, Sahana DS, Nijguna GS, Nayak P (2022) A Systematic approach of analysing network traffic using packet sniffing with scapy framework. In: Smys S, Bestak R, Palanisamy R, Kotuliak I (eds) Computer networks and inventive communication technologies. Springer, Singapore
Ahmed AESF, Elsayed HA (2022, March) Performance Comparison of SDN Wireless Network Under Floodlight and POX Controllers. In: 2022 13th International Conference on Electrical Engineering (ICEENG) (pp. 91–95). IEEE
Gupta N, Maashi MS, Tanwar S, Badotra S, Aljebreen M, Bharany S (2022) A comparative study of software defined networking controllers using mininet. Electronics 11(17):2715
Jain G (2021, March) Application of SNORT and Wireshark in network traffic analysis. In: IOP Conference Series: Materials Science and Engineering. IOP Publishing, 1119(1):012007
Funding
This declaration is “Not applicable”.
Author information
Authors and Affiliations
Contributions
All parts of the article were done by ABD.
Corresponding author
Ethics declarations
Conflict of interest
I declare that the authors have no competing interests as defined by Springer, or other interests that might be perceived to influence the results and/or discussion reported in this paper.
Ethical approval
This declaration is “Not applicable”.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Banitalebi Dehkordi, A. Examining the status of CPU working load, processing load and controller bandwidth under the influence of packet-in buffer status located in Openflow switches in SDN-based IoT framework. J Supercomput 79, 15814–15834 (2023). https://doi.org/10.1007/s11227-023-05258-4
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11227-023-05258-4