Abstract
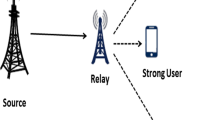
Although the progress in understanding 5G and beyond techniques such as Non-Orthogonal Multiple Access (NOMA) and full-duplex techniques has been overwhelming, still analyzing the security aspects of such systems under different scenarios and settings is an important concern that needs further exploration. In particular, when considering fading in wiretap channels and scenarios, achieving secrecy has posed many challenges. In this context, we propose to study the physical layer security (PLS) of cooperative NOMA (C-NOMA) system using the general fading distribution \(\kappa \)-\(\mu \). This distribution facilitates mainly the effect of light-of-sight as well as multipath fading. It also includes multiple distributions as special cases like: Rayleigh, Rice, Nakagami-m which help to understand the comportment of C-NOMA systems under different fading parameters. The use of Half-Duplex and Full-Duplex communication is also investigated for both Amplify-and-forward (AF) and Decode-and-Forward (DF) relaying protocols. To characterize the secrecy performance of the proposed C-NOMA systems, closed form expressions of the Secrecy Outage Probability (SOP) and the Strictly Positive Secrcey Capacity (SPSC) metrics for the strong and weak users are given for high signal-to-noise ratio (SNR) due to the intractable nature of the exact expressions. Based on the analytical analysis, numerical and simulation results are given under different network parameters. The results show, for low eavesdropper SNR, the positive effect of fading on the secrecy of the NOMA system. Whereas, fading deteriorates more the system secrecy with high eavesdropper SNR. We also deduce that FD relaying gives better secrecy to the weak user. While, more secrecy is granted to the strong user when using HD relaying.















Similar content being viewed by others
Availability of data and material :
Material and data are not available.
References
Vaezi, M., Ding, Z., & Poor, H. V. (Eds.). (2019). Multiple access techniques for 5G wireless networks and beyond. Berlin: Springer.
Dai, L., Wang, B., Ding, Z., Wang, Z., Chen, S., & Hanzo, L. (2018). A survey of non-orthogonal multiple access for 5G. IEEE Communications Surveys and Tutorials, 20(3), 2294–2323.
Liu, Y., Qin, Z., & Ding, Z. (2020). Non-orthogonal multiple access for massive connectivity. Berlin: Springer.
Higuchi, K., & Benjebbour, A. (2015). Non-orthogonal multiple access (NOMA) with successive interference cancellation for future radio access. IEICE Transactions on Communications, 98(3), 403–414.
Meng, L., Su, X., Zhang, X., Choi, C., & Choi, D. (2018). Signal reception for successive interference cancellation in NOMA downlink. In Proceedings of the 2018 conference on research in adaptive and convergent systems, https://doi.org/10.1145/3264746.3264751.
Ding, Z., Peng, M., & Poor, H. V. (2015). Cooperative non-orthogonal multiple access in 5G systems. IEEE Communications Letters, 19(8), 1462–1465.
Liaqat, M., Noordin, K. A., Latef, T. A., & Dimyati, K. (2020). Power-domain non orthogonal multiple access (PD-NOMA) in cooperative networks: an overview. Wireless Networks, 26(1), 181–203.
Fitzek, F. H., & Katz, M. D. (2006). Cooperation in wireless networks: principles and applications (421–461). New York: Springer.
Boujemâa, H. (2011). Static hybrid amplify and forward (AF) and decode and forward (DF) relaying for cooperative systems. Physical Communication, 4(3), 196–205.
Kim, J. B., & Lee, I. H. (2015). Capacity analysis of cooperative relaying systems using non-orthogonal multiple access. IEEE Communications Letters, 19(11), 1949–1952.
Liang, X., Wu, Y., Ng, D. W. K., Zuo, Y., Jin, S., & Zhu, H. (2017). Outage performance for cooperative NOMA transmission with an AF relay. IEEE Communications Letters, 21(11), 2428–2431.
Yang, Z., Ding, Z., Wu, Y., & Fan, P. (2017). Novel relay selection strategies for cooperative NOMA. IEEE Transactions on Vehicular Technology, 66(11), 10114–10123.
Men, J., Ge, J., & Zhang, C. (2016). Performance analysis of non orthogonal multiple access for relaying networks over Nakagami-\(m\) fading channels. IEEE Transactions on Vehicular Technology, 66(2), 1200–1208.
Zhong, C., & Zhang, Z. (2016). Non-orthogonal multiple access with cooperative full-duplex relaying. IEEE Communications Letters, 20(12), 2478–2481.
Chu, T. M. C., & Zepernick, H. J. (2018). Performance of a non-orthogonal multiple access system with full-duplex relaying. IEEE Communications Letters, 22(10), 2084–2087.
Nguyen, X. X., & Do, D. T. (2019). System performance of cooperative NOMA with full-duplex relay over nakagami-m fading channels. Mobile Information Systems. https://doi.org/10.1155/2019/7547431
Tregancini, A., Olivo, E. E. B., Osorio, D. P. M., de Lima, C. H., & Alves, H. (2019). Performance analysis of full-duplex relay-aided NOMA systems using partial relay selection. IEEE Transactions on Vehicular Technology, 69(1), 622–635.
Shen, Z., Liu, G., Ding, Z., Xiao, M., Ma, Z., & Yu, F. R. (2019). Optimal power allocations for 5G non-orthogonal multiple access with half/full duplex relaying. IEEE International Conference on Communications (ICC). https://doi.org/10.1109/ICC.2019.8761923
Mavoungou, S., Kaddoum, G., Taha, M., & Matar, G. (2016). Survey on threats and attacks on mobile networks. IEEE Access, 4, 4543–4572.
Zou, Y., Zhu, J., Wang, X., & Hanzo, L. (2016). A survey on wireless security: Technical challenges, recent advances, and future trends. Proceedings of the IEEE, 104(9), 1727–1765.
Pierrot, A. J., Chou, R. A., & Bloch, M. R. (2013). The effect of Eavesdropper’s statistics in experimental wireless secret-key generation. arXiv, https://arxiv.org/abs/1312.3304.
Trappe, W., Howard, R., & Moore, R. S. (2015). Low-energy security: Limits and opportunities in the internet of things. IEEE Security and Privacy, 13(1), 14–21.
Shannon, C. E. (1949). Communication theory of secrecy systems. The Bell System Technical Journal, 28(4), 656–715.
Wyner, A. D. (1975). The wire-tap channel. Bell System Technical Journal, 54(8), 1355–1387.
Fang, D., Qian, Y., & Hu, R. Q. (2017). Security for 5G mobile wireless networks. IEEE Access, 6, 4850–4874.
Ahmad, I., Kumar, T., Liyanage, M., Okwuibe, J., Ylianttila, M., & Gurtov, A. (2018). Overview of 5G security challenges and solutions. IEEE Communications Standards Magazine, 2(1), 36–43.
Khan, R., Kumar, P., Jayakody, D. N. K., & Liyanage, M. (2019). A survey on security and privacy of 5G technologies: Potential solutions, recent advancements, and future directions. IEEE Communications Surveys and Tutorials, 22(1), 196–248.
Chen, J., Yang, L., & Alouini, M. S. (2018). Physical layer security for cooperative NOMA systems. IEEE Transactions on Vehicular Technology, 67(5), 4645–4649.
ELHALAWANY, Basem M., RUBY, Rukhsana, RIIHONEN, Taneli, et al. Performance of cooperative NOMA systems under passive eavesdropping. In 2018 IEEE global communications conference (GLOBECOM). https://doi.org/10.1109/GLOCOM.2018.8647883.
Yu, C., Ko, H. L., Peng, X., & Xie, W. (2019). Secrecy outage performance analysis for cooperative NOMA over Nakagami-\( m \) channel. IEEE Access, 7, 79866–79876.
Abbasi, O., & Ebrahimi, A. (2017). Secrecy analysis of a NOMA system with full duplex and half duplex relay. In 2017 Iran workshop on communication and information theory (IWCIT), https://doi.org/10.1109/IWCIT.2017.7947676.
Feng, Y., Yang, Z., & Yan, S. (2017). Non-orthogonal multiple access and artificial-noise aided secure transmission in FD relay networks. In 2017 IEEE globecom workshops (GC Wkshps), https://doi.org/10.1109/GLOCOMW.2017.8269229.
Cao, Y., Tang, J., Zhao, N., Chen, Y., Zhang, X. Y., Jin, M., & Alouini, M. S. (2019). Full-duplex relay assisted secure transmission for NOMA networks. In IEEE/CIC International Conference on Communications in China (ICCC). https://doi.org/10.1109/ICCChina.2019.8855860
Cao, Y., Zhao, N., Pan, G., Chen, Y., Fan, L., Jin, M., & Alouini, M. S. (2019). Secrecy analysis for cooperative NOMA networks with multi-antenna full-duplex relay. IEEE Transactions on Communications, 67(8), 5574–5587.
Bloch, M., Barros, J., Rodrigues, M. R., & McLaughlin, S. W. (2008). Wireless information-theoretic security. IEEE Transactions on Information Theory, 54(6), 2515–2534.
Yacoub, M. D. (2001). The \(\kappa -\mu \) distribution: a general fading distribution. In IEEE 54th vehicular technology conference-fall 2001. https://doi.org/10.1109/VTC.2001.956432.
Yacoub, M. D. (2007). The \(\kappa -\mu \) distribution and the \(\eta -\mu \) distribution. IEEE Antennas and Propagation Magazine, 49(1), 68–81.
Fikadu, M. K., Sofotasios, P. C., Valkama, M., Muhaidat, S., Cui, Q., & Karagiannidis, G. K. (2015). Outage probability analysis of dual-hop full-duplex decode-and-forward relaying over generalized multipath fading conditions. In IEEE 11th international conference on wireless and mobile computing, networking and communications (WiMob), https://doi.org/10.1109/WiMOB.2015.7347992.
Simon, M. K., & Alouini, M. S. (2005). Digital communication over fading channels (Vol. 95). New Jersey: John Wiley and Sons.
Gradshteyn, I. S., & Ryzhik, I. M. (2015). Table of integrals, series, and products, 8th edn., ed. by D. Zwillinger.
Khoolenjani, N. B., & Khorshidian, K. (2009). On the ratio of Rice random variables.
Prudnikov, A. P., Brychkov, Y. A., & Marichev, O. I. (1986). Integrals and series, Volume 1: Elementary functions. New York: Gordon and Breach Science Publisher.
Prudnikov, A. P., Brychkov, I. A., & Marichev, O. I. (1986). Integrals and series: Special functions (Vol. 2). Boca Raton: CRC Press.
Funding
Publication supported by Canadian University of Dubai.
Author information
Authors and Affiliations
Contributions
It is the contribution of PHD student Nesrine Zaghdoud, Pr Adel Ben Mnaouer, Pr Hatem Boujemaa and Pr Farid Touati.
Corresponding author
Ethics declarations
Conflicts of interest/Competing interests :
The authors state that there is no conflict of interest for this paper.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendices
Proof of Equation Eq. (33)
In FD mode, We remind that \(\zeta =1\). Therefore, the CDF of \(\gamma _{R}^{FD}\) can be expressed as
Through the definition of the Marcum Q function in Eq 4.47 [39], \(F_{\gamma _{R}^{FD}}(x)\) will be written as
Using the defintion of the power series expansion in Eqs. (1.111) and (3.381.4) [40] to solve the integral, Eq. (61) can be solved as in Eq. (33).
Proof of Equation Eq. (34)
Using Eqs. (33) and (3) in Eq. (32), \(\varPhi _1^{FD,\varDelta }\) can be expressed as
where \(\kappa _e, \mu _e\) are the fading coefficient at the eavedropper, \(A_{R,E}=\frac{\mu _e(1+\kappa _e)}{\tilde{\gamma }_{R,E}}\) and \(G_e=\frac{\mu _e^2\kappa _e(1+\kappa _e)}{\tilde{\gamma }_{R,E}}\). Using Eq. (1.111)[40], Eq. (62) can be rewritten as
where \( B_1^{FD,\varDelta }=A_{R,E}+A_{S,R}X^{FD,\varDelta }\), \( D_1^{FD,\varDelta }=\frac{1}{\tilde{\gamma }_{R,R}A_{S,R}X^{FD,\varDelta }}+\frac{\theta _2^{FD,\varDelta }}{X^{FD,\varDelta }}\).
Using Eq. (2.3.6.9) in [42], we can solve Eq. (63) integral as in Eq. (34).
Proof of Equation Eq. (36)
From Eq. (31), \(\varPhi _{2}^{FD,\varDelta }\) can be expressed as
Using the series expansion of the marcum Q function in Eq. (4.47) [38] and the definition of the power series in Eq. (1.111)[41], \(\varPhi _{2}^{FD,\varDelta }\) can be expressed as
where \(B_2^{FD}=A_{R,E}+A_{R,1}C_1^{FD}\) and \(A_{R,1}=\frac{(1+\kappa )\mu }{\tilde{\gamma }_{R,1}}\). Let t = \(\sqrt{x}\), dx = 2tdt. By using Eq.2.15.5.4 [43] , we can rewrite last equation integral as
where \({}_1F_1\) is the Gauss hypergeometric function, as defined by Eq. (9.100) in[43].
Rights and permissions
About this article
Cite this article
Zaghdoud, N., Mnaouer, A.B., Boujemaa, H. et al. Secrecy performance analysis of half/full duplex AF/DF relaying in NOMA systems over \(\kappa -\mu \) fading channels. Telecommun Syst 79, 213–231 (2022). https://doi.org/10.1007/s11235-021-00851-5
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11235-021-00851-5