Abstract
We propose Multi-Spreader Routing, a store-carry-forward routing scheme for sparsely populated mobile ad hoc networks. Multi-Spreader Routing includes Epidemic Routing and Two-Hop Forwarding as special cases, and it can manage trade-off between message delivery delay and resource consumption effectively. We analyze various performance measures of Multi-Spreader Routing with a recovery scheme called VACCINE, and we evaluate its performance. Further, through simulation experiments with real mobility trace data, we demonstrate that Multi-Spreader Routing shows stable performance in various network environments.






















Similar content being viewed by others
References
Alresaini, M., Sathiamoorthy, M., Krishnamachari, B., & Neely, M. J. (2012). Backpressure with adaptive redundancy. In Proceedings of INFOCOM ’12 (pp. 2300–2308).
Altman, E., Başar, T., & De Pellegrini, F. (2010). Optimal monotone forwarding policies in delay tolerant mobile ad-hoc networks. Performance Evaluation, 67(4), 299–317.
Cao, Y., & Sun, Z. Routing in delay/disruption tolerant networks: A taxonomy, survey and challenges. IEEE Communications Surveys & Tutorials, to be published.
Chaintreau, A., Hui, P., Crowcroft, J., Diot, C., Gass, R., & Scott, J. (2007). Impact of human mobility on opportunistic forwarding algorithms. IEEE Transactions on Mobile Computing, 6(6), 606–620.
Conan, V., Leguay, J., & Friedman, T. (2008). Fixed point opportunistic routing in delay tolerant networks. IEEE Journal on Selected Areas in Communications, 26(5), 773–782.
Daly, E. M., & Haahr, M. (2007). Social network analysis for routing in disconnected delay-tolerant manets. In Proceedings of ACM MobiHoc 07 (pp. 32–40).
Dvir, A., & Vasilakos., A. V. (2010). Backpressure-based routing protocol for DTNs. In Proceedings of ACM SIGCOMM ’10 (pp. 405–406).
Farrell, S., & Cahill, V. (2006). Delay- and disruption-tolerant networking. Boston: Artech House.
Gaito, S., Pagani, E., & Rossi, G. P. (2009). Fine-grained tracking of human mobility in dense scenarios. In Proceedings of sixth IEEE SECON conference (pp. 40–42).
Gaito, S., Pagani, E., & Rossi, G. P. (2011). Strangers help friends to communicate in opportunistic networks. Computer Networks, 55(2), 374–385.
Groenevelt, R. (2005). Stochastic models for ad hoc networks. INRIA: Ph.D Thesis.
Groenevelt, R., Nain, P., & Koole, G. (2005). The message delay in mobile ad hoc networks. Performance Evaluation, 62(1), 210–228.
Grossglauser, M., & Tse, D. N. C. (2002). Mobility increases the capacity of ad hoc wireless networks. IEEE/ACM Transactions on Networking, 10(4), 477–486.
Haas, Z., & Small, T. (2006). A new networking model for biological applications of ad hoc sensor networks. IEEE/ACM Transactions on Networking, 14(1), 27–40.
Contacts.Exp6.dat, [Online]. Available: http://crawdad.cs.dartmouth.edu/meta.php?name=cambridge/haggle/imote/infocom2006.
Hui, P., Crowcroft, J., & Yoneki, E. (2008). Bubble rap: Social-based forwarding in delay tolerant networks. In Proceedings of ACM MobiHoc 08 (pp. 241–250).
Jones, E. P. C., & Ward, P. A. S. (2006). Routing strategies for delay-tolerant networks. University of Waterloo. [Online]. Available: http://ccng.uwaterloo.ca/~pasward/Publications/dtn-routing-survey.pdf.
Kulkarni, V. G. (1995). Modeling and analysis of stochastic systems. London: Chapman & Hall.
LeBrun, J., Chuah, C. N., Ghosal, D., & Zhang, M. (2005). Knowledge-based opportunistic forwarding in vehicular wireless ad hoc networks. In Proceedings of IEEE VTC 05-Spring (pp. 2289–2293).
Lindgren, A., Doria, A., & Schelén, O. (2003) Probabilistic routing in intermittently connected networks. ACM SIGMOBILE Mobile Computing and Communications Review, 7(3), 19–20.
Matsuda T., & Takine T. (2008) (p, q)-epidemic routing for sparsely populated mobile ad hoc networks. IEEE Journal on Selected Areas in Communications, 26(5), 783–793.
pmtr.txt, [Online]. Available: http://crawdad.cs.dartmouth.edu/unimi/pmtr.
Nelson, S. C., Bakht, M., & Kravets, R. (2009). Encounter-based routing in DTNs. In Proceedings of INFOCOM ’09 (pp. 846–854).
Singh, C., Kumar, A., & Sundaresan, R. (2010). Delay and energy optimal two-hop relaying in delay tolerant networks. In Proceedings of WiOpt2010: Modeling and optimization in mobile, ad hoc and wireless networks (pp. 256–265).
Spyropoulos, T., Psounis, K., & Raghavendra, C. (2005). Spray and wait: An efficient routing scheme for intermittently connected mobile networks. In Proceedings of SIGCOMM 2005 workshops (pp. 252–259).
Spyropoulos, T., Psounis, K., & Raghavendra, C. (2007). Spray and focus: Efficient mobility-assisted routing for heterogeneous and correlated mobility. In Proceedings of PerComW ’07 (pp. 79–85).
Spyropoulos, T., Psounis, K., & Raghavendra, C. (2008). Efficient routing in intermittently connected mobile networks: The single-copy case. IEEE/ACM Transactions on Networking, 16(1), 63–76.
Spyropoulos, T., Psounis, K., & Raghavendra, C. (2008). Efficient routing in intermittently connected mobile networks: The multiple-copy case. IEEE/ACM Transactions on Networking, 16(1), 77–90.
Spyropoulos, T., Rais, R. N. B., Thierry, T., Obraczka, K., & Vasilakos, A. V. (2010). Routing for disruption tolerant networks: Taxonomy and design. Wireless Networks, 16(8), 2349–2370.
Vahdat, A., & Becker, D. (2000). Epidemic routing for partially-connected ad hoc networks. Duke Technical Report, CS-2000-06.
Vasilakos, A. V., Zhang, Z., & Spyropoulos, T. (2012). Delay tolerant networks: Protocols and applications. New York: CRC Press.
Yuan, Q., Cardei, I., & Wu, J. (2009). Predict and relay: An efficient routing in disruption-tolerant networks. In Proceedings of ACM MobiHoc 09 (pp. 95–104).
Zhang, X., Neglia, G., Kurose, J., & Towsley, D. (2007). Performance modeling of epidemic routing. Computer Networks, 51(10), 2867–2891.
Zhang, Z. (2006). Routing in intermittently connected mobile ad hoc networks and delay tolerant networks: Overview and challenges. IEEE Communications Surveys & Tutorials, 8(1), 24–37.
Zeng, Y., Xiang, K., Li, D., & Vasilakos, A. V. (2013). Directional routing and scheduling for green vehicular delay tolerant networks. Wireless Networks, 19(2), 161–173.
Author information
Authors and Affiliations
Corresponding author
Appendices
Appendix 1: Transition rates from state (x, k, 0)
This appendix considers meetings of two nodes in state (\({\user2{x}},k,0\)).
-
1.
A spreader with counter value c j (\(j=1,2,\ldots,n(P)-1\)) encounters a vacant node: The vacant node becomes a spreader with counter value ⌊c j /2⌋. At the same time, the counter value of the spreader is updated to be \(\lceil c_j/2 \rceil.\) Therefore the state transition from state (\({\user2{x}},k,0\)) to state (\({\user2{x}}_j^{\prime},k+1,0\)) happens, where \({\user2{x}}_j^{\prime}\) is given in (3). Because there are x j spreaders with counter value c j and N − k vacant nodes in state (\({\user2{x}},k,0\)), the transition rate from state (\({\user2{x}},k,0\)) to state (\({\user2{x}}_j^{\prime},k+1,0\)) is given by (N − k) x j λ.
-
2.
A spreader with counter value c = 1 encounters a vacant node: The vacant node becomes a relay node. Therefore the state transition from state (\({\user2{x}},k,0\)) to state (\({\user2{x}},k+1,0\)) happens and its transition rate is given by (N − k) x n(P) λ.
-
3.
A spreader with counter value c j (\(j=1,2,\ldots,n(P)-1\)) encounters a relay node: As stated in Sect. 3.1, the relay node becomes a spreader with counter value ⌊c j /2⌋. At the same time, the counter value of the spreader is updated to be \(\lceil c_j/2\rceil.\) Thus the state transition from state (\({\user2{x}},k,0\)) to state (\({\user2{x}}_j^{\prime},k,0\)) happens, where \({\user2{x}}_j^{\prime}\) is given in (3). There are \(N_R^{[{\user2{x}},k]}\) relay nodes in state (\({\user2{x}},k,0\)), where \(N_R^{[{\user2{x}},k]}\) is given in (2). Thus the transition rate from state (\({\user2{x}},k,0\)) to state (\({\user2{x}}_j^{\prime},k,0\)) is given by \(N_R^{[{\user2{x}},k]} x_j \lambda.\)
-
4.
A spreader encounters the destination node: As soon as the spreader forwards the message to the destination node, both nodes generate the corresponding anti-packets. Therefore, when the counter value of the message that the spreader carries is equal to c j (\(j=1,2,\ldots,n(P)\)), the state transition from state (\({\user2{x}},k,0\)) to state (\({\user2{x}} - {\user2{e}}_j,k-1,2\)) happens. Because there is only one destination node, the transition rate from state (\({\user2{x}},k,0\)) to state (\({\user2{x}} - {\user2{e}}_j,k-1,2\)) is given by x j λ.
-
5.
A relay node encounters the destination node: As soon as the relay node forwards the message copy to the destination node, both nodes generate the corresponding anti-packets. Therefore the state transition from state (\({\user2{x}},k,0\)) to state (\({\user2{x}},k-1,2\)) happens, whose transition rate is given by \(N_R^{[{\user2{x}},k]} \lambda.\)
-
6.
Other cases: The numbers of spreaders and message copies remain the same, and therefore the state transition does not occur.
Appendix 2: Transition rates from state (x, k, m)
This appendix considers meetings of two nodes in state \(({\user2{x}},k,m)\) (m ≥ 2).
-
1.
A spreader with counter value c j (\(j=1,2,\cdots,n(P)-1\)) encounters a vacant node: The vacant node becomes a spreader with counter value ⌊c j /2⌋. At the same time, the counter value of the spreader is updated to be \(\lceil c_j/2 \rceil.\) Therefore the state transition from state (\({\user2{x}},k,m\)) to state (\({\user2{x}}_j^{\prime},k+1,m\)) happens, where \({\user2{x}}_j^{\prime}\) is given in (3), and its transition rate is given by (N + 1 − k − m) x j λ because there are x j spreaders with counter value c j and N + 1 − k − m vacant nodes in state (\({\user2{x}},k,m\)).
-
2.
A spreader with counter value c n(P) (=1) encounters a vacant node: The vacant node becomes a relay node. Therefore the state transition from state (\({\user2{x}},k,m\)) to state (\({\user2{x}},k+1,m\)) happens, whose transition rate is given by (N + 1 − k − m) x n(P) λ.
-
3.
A spreader with counter value c j (\(j=1,2,\cdots,n(P)-1\)) encounters a relay node: The relay node becomes a spreader with counter value ⌊c j /2⌋. At the same time, the counter value of the spreader is updated to be \(\lceil c_j/2 \rceil.\) Therefore the state transition from state \(({\user2{x}},k,m)\) to state \(({\user2{x}}_j^{\prime},k,m)\) happens. Because the number of relay nodes in state \(({\user2{x}},k,m)\) is given by \(N_R^{[{\user2{x}},k]}\) in (2), the transition rate is given by \(N_R^{[{\user2{x}},k]} x_j \lambda.\)
-
4
A spreader encounters a node with an anti-packet: The spreader receives an anti-packet and deletes the message. Therefore, when the spreader has the message with counter value c j (\(j=1,2,\cdots,n(P)\)), the state transition from state (\({\user2{x}},k,m\)) to state (\({\user2{x}} - {\user2{e}}_j,k-1,m+1\)) happens, and its transition rate is given by m x j λ because there are m nodes with anti-packets.
-
5.
A relay node encounters a node with an anti-packet: The relay node receives an anti-packet and deletes the message copy. Thus the state transition from state (\({\user2{x}},k,m\)) to state (\({\user2{x}},k-1,m+1\)) happens and its transition rate is given by \(m N_R^{[{\user2{x}},k]} \lambda.\)
-
6
A node with an anti-packet encounters a vacant node: The vacant node receives an anti-packet. Therefore the state transitions from state (\({\user2{x}},k,m\)) to state (\({\user2{x}},k,m+1\)) happens, and its transition rate is given by m (N + 1 − k − m)λ.
-
7
Other cases: The numbers of spreaders, message copies, and anti-packets remain the same, and therefore the state transition does not occur.
Appendix 3: Mean length of the lifetime of a message
We define \(T_E({\user2{x}},k,m)\) (\(m=0,2,3,\ldots,N+1,\) \({({\user2{x}},k,m) \in {\mathcal{S}}_P(m)}\)) as
where T E is defined in (7). By definition, \(\hbox{E}[T_E] = T_E({\user2{e}}_1,1,0).\) It follows from Table 2 that \(T_E({\user2{x}},k,0)\) (\(N_S^{[{\user2{x}}]} \le k \le N\)) satisfies
where \(T_E({\user2{x}},N+1,0) = T_E({\user2{x}},0,0) = T_E({\bf 0},k,0) = 0\).
Also, it follows from Table 3 that for m ≥ 2, the sum \(\lambda_2({\user2{x}},k,m)\) (\({({\user2{x}},k,m) \in {\mathcal{S}}_P(m)}\)) of transition rates from state \(({\user2{x}},k,m)\) is given by
Therefore \(T_E({\user2{x}},k,m)\) (\(N_S^{[{\user2{x}}]} \le k \le N - 1, 2 \le m \le N, k+m \le N+1\)) satisfies
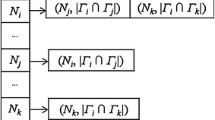
where \(T_E({\user2{x}},0,m) = T_E({\user2{x}},N+2-m,m) = 0.\) Recall that, for each m (\(m=0,2,3,\ldots,N+1\)), states \({{\user2{x}} \in {\mathcal{X}}_P(m)}\) of spreaders are labeled in ascending order of \(N_S^{[{\user2{x}}]}.\) For a given m, we denote the lth (\({l=1,2,\ldots,|{\mathcal{X}}_P(m)|}\)) element in \({{\mathcal{X}}_P(m)}\) by \({\user2{x}}^{[l]} = (x_1^{[l]}, x_2^{[l]}, \ldots, x_{n(P)}^{[l]}).\) As a result, we can compute \(\hbox{E}[T_E]=T_E({\user2{e}}_1,1,0)\) by the backward recursive procedure given in Fig. 23.
Appendix 4: Mean accumulated number of messages in the system
The offered load O L and the mean number E[N I ] of transmissions of information about the message are given in terms of \(R({\user2{e}}_1,1,0),\) which can be computed as follows. We define \(R({\user2{x}},k,m)\) (\(m=0,2,3,\ldots,N+1,\) \(({\user2{x}},k,m) \in {\mathcal{S}}_P(m))\) as
Similar to \(T_E({\user2{x}},k,m),\) it is easy to see that \(R({\user2{x}},k,0)\) (\(N_S^{[{\user2{x}}]} \le k \le N\)) satisfies
where \(R({\user2{x}},N+1,0) = R({\user2{x}},0,0) = R({\bf 0},k,0) = 0\). Also, \(R({\user2{x}},k,m)\) (\(N_S^{[{\user2{x}}]} \leq k \leq N-1,\) 2 ≤ m ≤ N, k + m ≤ N + 1) satisfies
where \(R({\user2{x}},0,m) = R({\user2{x}},N+2-m,m) =0.\) Therefore \(R({\user2{e}}_1,1,0)\) can be computed by the backward recursion in Fig. 23, where \(T_E({\user2{x}}^{[l]}, k, m)\) is replaced by \(R({\user2{x}}^{[l]}, k, m)\).
Appendix 5: Mean number of message copy transmissions
Let N D denote the accumulated number of message copy transmissions till extinction. We then define \(N_D({\user2{x}},k,m)\) (\({m=0,2,3,\ldots,N+1,\,({\user2{x}},k,m) \in {\mathcal{S}}_P(m)}\)) as
It then follows from Table 2 that \(N_D({\user2{x}},k,0)\) (\(N_S^{[{\user2{x}}]} \le k \le N\)) satisfies
where \(N_D({\user2{x}},N+1,0) = N_D({\user2{x}},0,0) = N_D({\bf 0},k,0) = 0\). Also, it follows from Table 3 that \(N_D({\user2{x}},k,m)\) (\(N_S^{[{\user2{x}}]} \le k \le N - 1, 2 \le m \le N, k+m \le N+1\)) satisfies
where \(N_D({\user2{x}},0,m) = N_D({\user2{x}},N+2-m,m) = 0.\) Therefore \(\hbox{E}[N_D] = N_D({\user2{e}}_1,1,0)\) can be computed by the backward recursive procedure in Fig. 23, where \(T_E({\user2{x}}^{[l]},k,m)\) is replaced by \(N_D({\user2{x}}^{[l]},k,m)\).
Rights and permissions
About this article
Cite this article
Kimura, T., Matsuda, T. & Takine, T. Multi-Spreader Routing for sparsely populated mobile ad hoc networks. Wireless Netw 20, 155–175 (2014). https://doi.org/10.1007/s11276-013-0597-6
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11276-013-0597-6