Abstract
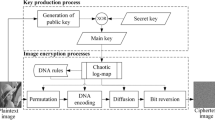
In this paper, a content-based image verification scheme is presented. This scheme is suitable for verifying the integrity of images transmitted over insecure networks. The Discrete Cosine Transform is used to embed a block-based mark for each block in another block according to a specific algorithm. To achieve higher protection, the marked image is then encrypted using 2-D chaotic Baker map before being transmitted over the communication channel. The encrypted marked image is transmitted over a wireless Additive White Gaussian Noise (AWGN) channel without error correction codes. At the receiver side, a decryption process is performed, and the marks embedded in each block are extracted to detect suspicious forgery activities. Simulation results show the suitability of the proposed scheme for applications with sensitive data types such as military and nuclear applications.








Similar content being viewed by others
References
Lou, D. C., Liu, J. L., & Li, C. T. (2003). Digital signature-based image authentication. In C. S. Lu (Ed.), Multimedia security: Steganography and digital watermarking techniques for protection of intellectual property. Hershey: Idea Group Inc.
Petrovic, R. (2005). Digital watermarks for audio integrity verification. Serbia and Montenegro, Nis, pp. 28–30.
Chang, W. H., & Chang, L. W. (2010). Semi-fragile watermarking for image authentication, localization, and recovery using Tchebichef moments. In Communications and Information Technologies (ISCIT).
Radharani, S., & Valarmathi, M. L. (2010). A study of watermarking scheme for image authentication. International Journal of Computer Applications, 2(4), 24–32.
Li, C.-T., & Yang, F.-M. (2003). One-dimensional neighborhood forming strategy for fragile watermarking. Journal of Electronic Imaging, 12(2), 284–291.
Barni, M., Bartolini, F., Cappellini, V., & Piva, A. (1998). A DCT-domain system for robust image watermarking. Signal Processing, 66, 357–372.
Cox, I. J., Kilian, J., Leighton, F. T., & Shamoon, T. (1997). Secure spread spectrum watermarking for multimedia. IEEE Transactions on Image Processing, 6(12), 1673–1687.
Hartung, F., & Girod, B. (1998). Watermarking of uncompressed and compressed video. Signal Processing, 66, 283–301.
Li, C.-T., Lou, D.-C., & Liu, J.-L. (2000). Image authentication and integrity verification via content-based watermarks and a public key cryptosystem. International Conference on Image Processing, 3, 694–697.
Sultana, F., Charles, S., & Govardhan, A. (2013). A tamper proof noise resilient end to end image based authentication system over wireless transmission with AWGN channel using wavelet based templates and AES. IJCSNS International Journal of Computer Science and Network Security, 13(5), 41–48.
Shoemaker, C. (2002). Rudko. Hidden bits: A survey of techniques for digital watermarking. Independent Study EER-290 Prof Rudko, Spring.
Tewfik, A. H. (2000). Digital watermarking. San Mercury News.
Goel, S., Rana, A., Kaur, M. (2013). A review of comparison techniques of image steganography. IOSR Journal of Electrical and Electronics Engineering (IOSR-JEEE), 6(1), 41–48. ISSN: 2278-1676, p-ISSN: 2320-3331.
El-Bendary, M. A. M., Abou-El-azm, A. E., El-Fishawy, N. A., Shawki, F., El-Tokhy, M. A. R., Kazemian, H. B. (2012). Performance of the audio signals transmission over wireless networks with the channel interleaving considerations. EURASIP Journal on Audio, Speech, and Music Processing, 1–14.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Nassar, S.S., Ayad, N.M., Kelash, H.M. et al. Content Verification of Encrypted Images Transmitted Over Wireless AWGN Channels. Wireless Pers Commun 88, 479–491 (2016). https://doi.org/10.1007/s11277-015-3142-3
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-015-3142-3