Abstract
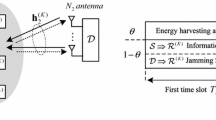
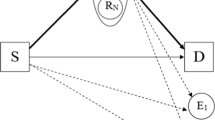
In this paper, we propose three secrecy cooperative transmission protocols for a two-way energy-constrained relaying network in which two sources wish to exchange information with the help of multiple intermediate relays being subjected to wiretapping by multiple eavesdroppers. In the secure two-way communication (STW protocol), an energy-constrained relay is preselected via one of three investigated relay-selection strategies, which harvest the energy from the radio-frequency signals of one source and decode-and-forward the signals to another source. In secure two-way communication with network coding (STWNC protocol), the network coding technique is applied at a relay preselected via one of two investigated relay-selection strategies. In secure two-way communication with cooperative jamming and network coding (STWJNC protocol), under cooperative jamming, the network coding technique is applied at two sources and a preselected relay where a jammer-relay pair is preselected via one of two investigated selection strategies. The power-splitting receiver is applied at the energy-constrained relay for all proposed protocols. To evaluate performance, we derive new closed-form expressions for the secrecy outage probability and the throughput performance of the three protocols with the different relay and jammer-selection strategies. Our analysis is verified using Monte Carlo simulations.







Similar content being viewed by others
References
Raghunathan, V., Ganeriwal, S., & Srivastava, M. (2006). Emerging techniques for long lived wireless sensor networks. IEEE Communications Magazine, 44(4), 108–114.
Paradiso, J. A., & Starner, T. (2005). Energy scavenging for mobile and wireless electronics. IEEE Pervasive Computing, 4(1), 18–27.
Ulukus, S., Yener, A., Erkip, E., Simeone, O., Zorzi, M., Grover, P., et al. (2015). Energy harvesting wireless communications: A review of recent advances. IEEE Journal on Selected Areas in Communications, 33(3), 360–381.
Medepally, B., & Mehta, N. B. (2010). Voluntary energy harvesting relays and selection in cooperative wireless networks. IEEE Transactions on Wireless Communications, 8(11), 3543–3553.
Zhou, X., Zhang, R., & Ho, C. K. (2013). Wireless information and power transfer: Architecture design and rate-energy tradeoff. IEEE Transactions on communications, 61(11), 4754–4767.
Lumpkins, W. (2014). Nikola Teslas dream realized: Wireless power energy harvesting. IEEE Consumer Electronics Magazine, 3(1), 39–42.
Pinuela, M., Mitcheson, P. D., & Lucyszyn, S. (2013). Ambient RF energy harvesting in urban and semi-urban environments. IEEE Transactions on Microwave Theory and Techniques, 61(7), 2715–2726.
Grover, P., & Sahai, A. (2010). Shannon meet Tesla: Wireless information and power transfer. In IEEE international symposium on information theory proceedings (ISIT), pp. 2363–2367.
Zhang, R., & Ho, C. K. (2013). MIMO broadcasting for simultaneous wireless information and power transfer. IEEE Transactions on Wireless Communications, 12(5), 1989–2001.
Varshney, L. R. (2008). Transporting information and energy simultaneously. In IEEE international symposium on information theory (ISIT), pp. 1612–1616.
Liu, L., Zhang, R., & Chua, K. C. (2013). Wireless information transfer with opportunistic energy harvesting. IEEE Transactions on Wireless Communications, 12(1), 288–300.
Nasir, A. A., Xiangyun, Z., Durrani, S., & Kennedy, R. A. (2013). Relaying protocols for wireless energy harvesting and information processing. IEEE Transactions on Wireless Communications, 12(7), 3622–3636.
Nasir, A. A., Zhou, X., Durrani, S., & Kennedy, R. A. (2015). Wireless-powered relays in cooperative communications: Time-switching relaying protocols and throughput analysis. IEEE Transactions on Communications, 63(5), 1607–1622.
Ding, Z., Perlaza, S. M., Esnaola, I., & Poor, H. V. (2014). Power allocation strategies in energy harvesting wireless cooperative networks. IEEE Transactions on Wireless Communications, 13(2), 846–860.
Liu, Y., Wang, L., Elkashlan, M., & Duong, T. Q. (2014). Two-way relaying networks with wireless power transfer: Policies design and throughput analysis. In IEEE global communications conference (GLOBECOM), pp. 4030–4035.
Son, P. N., & Kong, H. Y. (2015). Energy-harvesting relay selection schemes for decode-and-forward dual-hop networks. IEICE Transactions on Communications, E98-B(4), 661–672.
Stallings, W. (2003). Cryptography and network security principles and practices (3rd ed.). Upper Saddle River, NJ: Prentice Hall.
Wyner, A. D. (1975). The wire-tap channel. The Bell System Technical Journal, 54(8), 1355–1387.
Leung-Yan-Cheong, S., & Hellman, M. E. (1978). The Gaussian wire-tap channel. IEEE Transaction on Information Theory, 24(4), 451–456.
Csiszar, I., & Korner, J. (1978). Broadcast channels with confidential messages. IEEE Transactions on Information Theory, 24(3), 339–348.
Liang, Y., Poor, H. V., & Shamai, S. (2008). Secure communication over fading channels. IEEE Transactions on Information Theory, 54(6), 2470–2492.
Dong, L., Han, Z., Petropulu, A. P., & Poor, H. V. (2010). Improving wireless physical layer security via cooperating relays. IEEE Transactions on Signal Processing, 58(3), 1875–1888.
Zang, R., Song, L., Han, Z., Jiao, B., & Debbah, M. (2010). Physical layer security for for two way relay communications with friendly jammers. In: IEEE global telecommunications conference (GLOBECOM), pp. 1–6.
Wang, L., Elkashlan, M., Huang, J., Tran, N. H., & Duong, T. Q. (2014). Secure transmission with optimal power allocation in untrusted relay networks. IEEE Wireless Communications Letters, 3(3), 289–292.
Wang, L., Kim, K. J., Duong, T. Q., Elkashlan, M., & Poor, H. V. (2014). On the security of cooperative single carrier systems. In IEEE global telecommunications conference (GLOBECOM), Austin, TX, pp. 1596–1601.
Duong, T. Q., Duy, T. T., Elkashlan, M., Tran, N. H., & Dobre, O. A. (2014). Secured cooperative cognitive radio networks with relay selection. In IEEE global telecommunications conference (GLOBECOM), Austin, TX, pp. 3074–3079.
Liu, Y., Wang, L., Duy, T. T., Elkashlan, M., & Duong, T. Q. (2015). Relay selection for security enhancement in cognitive relay networks. IEEE Wireless Communication Letters, 4(1), 46–49.
Jong-Ho, L. (2015). Cooperative relaying protocol for improving physical layer security in wireless decode-and-forward relaying networks. Wireless Personal Communications, 83(4), 3033–3044.
Krikidis, I., Thompson, J. S., & Mclaughlin, S. (2009). Relay selection for secure cooperative networks with jamming. IEEE Transactions on Wireless Communications, 8(10), 50035011.
Long, H., Xiang, W., Wang, J., Zhang, Y., & Wang, W. (2014). Cooperative jamming and power allocation with untrusty two-way relay nodes. IET Communications, 8(13), 2290–2297.
Duy, T. T., Duong, T. Q., Benevides da Costa, D., Bao, V. N. Q., & Elkashlan, M. (2015). Proactive relay selection with joint impact of hardware impairment and co-channel interference. IEEE Transaction on Communications, 64(5), 1594–1606.
Gradshteyn, I. S., Ryzhik, I. M., Jeffrey, A., & Zwillinger, D. (2007). Table of integral, series and products (7th ed.). London: Academic Press.
Author information
Authors and Affiliations
Corresponding author
Appendices
Appendix 1: The PDF of RVs \({\varvec{g_{{R_s}E\max }}}\), \({\varvec{g_{S2E\max }}}\), and \({\varvec{g_{S1E\max }}}\) When Using the Relay Selection Strategy in (19a)
The CDFs of RVs \({g_{{R_s}E\max }}\), \({g_{S2E\max }}\), and \({g_{S1E\max }}\) can be given respectively as
Then, by differentiating (66), (67), and (68), we obtain the PDFs of RVs \({g_{{R_s}E\max }}\), \({g_{S2E\max }}\), and \({g_{S1E\max }}\), respectively, as follows:
Appendix 2: Proof of Lemma 1
At first, the integral \({I_{{\mathrm{1,MAS1R}}}}\) can be expressed as
where (72.2) is obtained by approximating \({e^{\frac{{ - \left( {\varphi - 1} \right) {\lambda _{RS2}}}}{{{\omega _3}\psi {x_3}}}}} \approx 1 + \frac{{ - \left( {\varphi - 1} \right) {\lambda _{RS2}}}}{{{\omega _3}\psi {x_3}}}\).
The term \({I_3}\) and \({I_4}\) in (72) are denoted and derived as in (73) and (74) as follows
where (74.1) is obtained from by using \(\int _0^\infty {L{\lambda _{S2 E}} \sum \limits _{w = 0}^{L - 1} {C_{L - 1}^w} {{\left( { - 1} \right) }^w}{e^{ - \left[ {\frac{{\left( {1 + w} \right) {\omega _2}{\lambda _{S2E}} + \varphi {\omega _1}{\lambda _{S2R}}}}{{{\omega _2}}}} \right] {x_2}}}} = {\varOmega _3} \left( { L, \varphi , {\omega _1}, {\omega _2},{\lambda _{S2 R}}, {\lambda _{S2 E}}} \right)\) and \(\int _{\frac{{\varphi - 1}}{{{\omega _2}\psi }} + \frac{{\varphi {\omega _1}{x_1}}}{{{\omega _2}}}}^\infty {\frac{{{e^{ - \left( {1 + k} \right) {\lambda _{S1R}}{x_3}}}}}{{{x_3}}}} d{x_3} = \varGamma \left[ {0,\left( {1 + k} \right) {\lambda _{S1R}}\left( {\frac{{\varphi - 1}}{{{\omega _2}\psi }} + \frac{{\varphi {\omega _1}{x_1}}}{{{\omega _2}}}} \right) } \right]\) (see [32, Eq. (3.381.3)]); (74.2) is obtained from (74.1) by approximating \(\frac{{\varphi - 1}}{{{\omega _2}\psi }}\mathop \approx \limits ^{{\mathrm{high}}\,\,\psi \,} 0\); (73.3) is obtained from (74.2) by using the Eq. (6.455.1) of [32] in the case of \(\mu = 1\) and \(v = 0\), as \(\int _0^\infty {{e^{ - \beta x}}} \varGamma \left( {0,\alpha x} \right) dx = \frac{1}{{\alpha + \beta }}_2{F_1}\left( {1,\,1\,;\,2\,;\frac{\beta }{{\alpha + \beta }}} \right).\)
We finish the proof by combining (72), (73), and (74).
Appendix 3: Proof of Lemma 2
The integral \({I_{2,\mathrm{MAS1R}}}\) can be obtained after some steps with using [32, Eq. (3.381.3)] and approximating \(\frac{{\varphi - 1}}{{{\omega _2}\psi }} \approx 0\), and \(\frac{{ - \left( {\varphi - 1} \right) {\lambda _{RS2}}}}{{{\omega _3}\psi {x_3}}} \approx 0\) when \(\psi\) is high, as follows
where \({I_5}\) and \({I_6}\) are denoted and derived as in (76) and (77), respectively
We finish the proof by combining (75), (76), and (77).
Appendix 4: Proof of Equation (59.2)
The expression for the probability term \(\Pr \left[ {\min \left( {{C_{{J_1}S1}},{C_{{J_1}S2}}} \right) \ge {C_t}} \right]\) can be obtained as follows:
By substituting (78) into (59.1), we finish the proof.
Appendix 5: Proof of Lemma 3
By substituting (49), (50), (51), and (5) into (61), we obtain
From the optimal jammer and relay selection strategy, in (48a), the CDF of RV \({g_{{J_s}{R_s}}}\) is expressed as
By substituting (80), \({f_{{g_{S1{R_s}}}}}( {{x_1}} ) = {\lambda _{S1R}}{e^{ - {\lambda _{S1R}}{x_1}}}\), \({f_{{g_{S2{R_s}}}}}\left( {{x_2}} \right) = {\lambda _{S2R}}{e^{ - {\lambda _{S2R}}{x_2}}}\), \({f_{{g_{{J_s}{R_s}}}}}\left( {{x_3}} \right) = KM{\lambda _{JR}}\sum \nolimits _{k = 0}^{KM - 1} {C_{KM - 1}^k{{\left( { - 1} \right) }^k}{e^{ - \left( {1 + k} \right) {\lambda _{JR}}{x_3}}}}\), \({f_{{g_{{R_s}S1}}}}\left( {{x_4}} \right) = {\lambda _{RS1}}{e^{ - {\lambda _{RS1}}{x_4}}}\), and \({f_{{g_{{R_s}S2}}}}\left( {{x_5}} \right) = {\lambda _{RS2}}{e^{ - {\lambda _{RS2}}{x_5}}}\) into (79), we can obtain
From [32, Eq. (3.381.1)], \(\int _0^\infty {{e^{ - \beta /4x - \gamma x}}dx} = \sqrt{\beta /\gamma } {K_1}\left( {\sqrt{\beta \gamma } } \right)\), we obtain
By substituting (82) into (81), we complete the proof.
Appendix 6: Proof of Lemma 4
By substituting (54), (55), (56), and (57) into (62), we obtain
By substituting the PDFs of the eight RVs \({{g_{S1E\max }}}\), \({S2E\max }\), \({S1{R_s}}\), \({S2{R_s}}\), \({{g_{{J_s}{R_s}}}}\), \({{g_{{R_s}E\max }}}\), \({{g_{{R_s}S1}}}\), and \({{g_{{R_s}S2}}}\), into (83) and after some manipulations of (83), the Eq. (64) in Lemma 4 is obtained. This completes the proof.
Rights and permissions
About this article
Cite this article
Nguyen, S.Q., Kong, H.Y. Improving Secrecy Outage and Throughput Performance in Two-Way Energy-Constraint Relaying Networks Under Physical Layer Security. Wireless Pers Commun 96, 6425–6457 (2017). https://doi.org/10.1007/s11277-017-4485-8
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-017-4485-8