Abstract
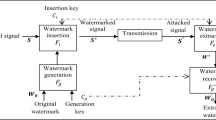
The work proposed in this paper aims at two major concerns of wireless transmission, which are security and imperceptibility of the transmitting data. This method uses a digital audio signal as carrier for the actual message data to be transmitted in a concealed form and has two complementary parts, insertion of payload in a source audio signal at the sender end and retrieval of payload at the receiver end. To enhance security of the system, three fold measure has been taken to safeguard the hidden data from any potential hacking attempt. These are, (1) insertion of payload in transformed domain based on DFT instead of time domain, (2) use of pseudo-random bit positions for insertion and (3) using a common secret key by both sending and receiving parties. Imperceptibility of the transmitting data is also emphasized by reducing the internal noise impact within the carrier audio signal at the time of insertion. Furthermore, the integrity and authenticity of the retrieved message is verified at the receiving end. The proposed method has been thoroughly examined by various performance metrics in different scenarios, which prove its effectiveness.


Similar content being viewed by others
References
Bender, W., Gruhl, D., & Morimoto, N. (1996). Techniques for data hiding. IBM Systems Journal, 35(3), 313–336.
Zwicker, E., & Fastl, H. (2007). Psychoacoustics–facts and models (3rd ed.). Berlin: Springer.
Cvejic, N. (2004). Algorithms for audio watermarking and steganography. Oulu: University of Oulu.
Acevedo, A. (2003). Digital watermarking for audio data in techniques and applications of digital watermarking and content protection. Norwood: Artech House.
Arnold, M. (2000). Audio watermarking: Features, applications and algorithms. In IEEE international conference on multimedia and expo (pp. 1013–1016).
Bhalshankar, S. (2015). Audio steganography: LSB technique using a pyramid structure and range of bytes. International Journal of Advanced Computer Research, 5(20), 233.
Pal, D., Goswami, A., & Ghoshal, N. (2012). Lossless audio steganography in spatial domain. In International conference on frontiers of intelligent computing: theory and applications, AISC 199 (pp. 575–582). Springer, Berlin. https://doi.org/10.1007/978-3-642-35314-7.
Erfani, Y., & Siahpoush, S. (2009). Robust audio watermarking using improved TS echo hiding. Digital Signal Process, 19, 809–814.
Johnson, N., & Katzenbeisser, S. C. (1999) A survey of steganographic techniques.
Zhang, Y., Lu, Z. M., & Zhao, D. N. (2010). Quantization based semi-fragile watermarking scheme for H264 video. Information Technology Journal, 9(7), 1476–1482.
Gang, L., Akansu, A. N., & Ramkumar, M. (2001) MP3 resistant oblivious steganography. In IEEE international conference on acoustics, speech, and signal processing (Vol. 3, pp. 1365–1368). Salt Lake City.
Djebbar, F., Ayad, B., Abed-Meraim, K., & Habib, H. (2012). Unified phase and magnitude speech spectra data hiding algorithm. Journal of Security and Communication Networks, 6, 961–971.
Cox, I. J., Kilian, J., Leighton, F. T., & Shamoon, T. (1997). Secure spread spectrum watermarking for multimedia. IEEE Transactions on Image Processing, 6(12), 1673–1687.
Khan, K. (1984). Cryptology and the origins of spread spectrum. IEEE Spectrum, 21, 70–80.
Gopalan, K., & Wenndt, S. (2004). Audio steganography for covert data transmission by imperceptible tone insertion. In WOC 2004, Banff, Canada.
Ghoshal, N., & Mandal, J. K. (2011). Discrete Fourier transform based multimedia color image authentication for wireless communication. In 2nd International conference on wireless communications, vehiculare on emetechnology, information theory and aerospace and electronic systems technology, wireless vitae 2011, Chennai, India.
Ghoshal, N., & Mandal, J. K. (2011). Controlled data hiding technique for color image authentication in frequency domain. In 2nd international conference on emerging applications of information technology, EAIT-2011, CSI Kolkata Chapter, Kolkata, India (pp. 284–287).
Yang, S., Tan, W., Chen, Y., & Ma, W. (2010). Quantization-Based digital audio watermarking in discrete Fourier transform domain. Journal of Multimedia, 5(2), 151.
Dhar, P. K., Khan, M. I., & Ahmad, S. (2010). New DCT based watermarking method for copyright protection of digital audio. International Journal of Computer Science and Information TECHNOLOGY (IJCSIT), 2(5), 91–101.
Al-Haj, A., Mohammad, A., & Bata, L. (2011). DWT–based audio watermarking. The International Arab Journal of Information Technology, 8(3), 326–333.
Foo, S. W., Ho, S. M., & Ng, L. M. (2004). Audio watermarking using time-frequency compression expansion. In IEEE international symposium on circuits and systems (pp. 201–204).
Djebbar, F., Ayad, B., Meraim, K. A., & Hamam, H. (2012). Comparative study of digital audio steganography techniques. EURASIP Journal on Audio, Speech and Music Processing.
Al-haj, A. (2014). An imperceptible and robust audio watermarking algorithm. EURASIP Journal on Audio, Speech and Music Processing,. https://doi.org/10.1186/s13636-014-0037-2.
Tvs, G. P., & Varadarajan, S. (2015) A novel hybrid audio steganography for imperceptible data hiding. In International conference on communications and signal processing (ICCSP) Melmaruvathur, India (pp. 0634–0638). https://doi.org/10.1109/ICCSP.2015.7322565.
El-Khamy, S. E., Korany, N. O., & El-Sherif, M. H. (2017). A security enhanced robust audio steganography algorithm for image hiding using sample comparison in discrete wavelet transform domain and RSA encryption. Multimedia Tools and Applications. New York: Springer.
Deshpande, A. R., & Kant, N. N. (2016). Security Enhancement in Audio Steganography by Encryption Algorithm. International Journal of Emerging Technologies in Engineering Research, 4(2), 73–76.
Ghoshal, N., Mandal, J. K., Sarkar, A., Chakraborty, D., & Ghosh, S. (2009). Image authentication by hiding large volume of data and secure message transmission technique using mask. In IEEE international advanced computing conference (pp. 3177–3182). Patiala: Thapar University.
Ghoshal, N., Mandal, J. K., & Khamrui, A. (2009). A framework for block based image authentication. In 4th IEEE international conference on industrial and information systems, ICIIS09 (pp. 343–348). Peradeniya: Peradeniya University.
Cvejic, N., & Seppanen, T. (2008). Digital audio watermarking techniques and technologies: Applications and benchmarks. Information Science Reference. New York: Hershey.
Campbell, D., Jones, E., & Glavin, M. (2009). Audio quality assessment techniques–A review and recent developments. Journal of Signal Processing. https://doi.org/10.1016/j.sigpro.2009.02.015.
Acknowledgements
The authors express their deep sense of gratitude to the faculty members of the Department of Engineering and Technological Studies, University of Kalyani, West Bengal, India, where the work has been carried out.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Pal, D., Ghoshal, N. Secured and Imperceptible Data Transmission Through Digital Audio Signal with Reduced Internal Noise. Wireless Pers Commun 100, 505–518 (2018). https://doi.org/10.1007/s11277-017-5095-1
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-017-5095-1