Abstract
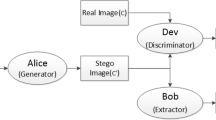
Recent advancements in steganography analysis based on deep neural networks have led to the development of steganography schemes that incorporate deep network technology like adversarial example, GAN, and reinforce learning. However, most deep network-based steganography schemes are unable to ensure error-free extraction of secret information because of the design similar to information reconstruction. To address this issue, this work proposes a novel audio steganography cover enhancement framework that leverages two networks—a policy network and an environment network—to enhance the undetectability and imperceptibility of the steganographic audio. The proposed schemes utilize the reinforcement algorithm to optimize steganography cover modification for improving undetectability and imperceptibility. And our method guarantees 100% extracting accuracy by only enhancing on domains that do not affect information extraction. The experimental results demonstrate that our method significantly enhances the missing detection rate of the target audio steganography analysis network over 90% when resisting a steganalysis network, and meanwhile, our method has strong imperceptibility which can hardly be distinguished by human ears.



Similar content being viewed by others
Data availability
The dataset can be shared by the corresponding author upon request.
References
Tang, W., Li, B., Tan, S., Barni, M., Huang, J.: CNN-based adversarial embedding for image steganography. IEEE Trans. Inf. Forensics Secur. 14(8), 2074–2087 (2019). https://doi.org/10.1109/TIFS.2019.2891237
Bernard, S., Pevnỳ, T., Bas, P., Klein, J.: Exploiting adversarial embeddings for better steganography. In: Proceedings of the ACM Workshop on Information Hiding and Multimedia Security, pp. 216– 221 ( 2019)
Wu, J., Chen, B., Luo, W., Fang, Y.: Audio steganography based on iterative adversarial attacks against convolutional neural networks. IEEE Trans. Inf. Forensics Secur. 15, 2282–2294 (2020). https://doi.org/10.1109/TIFS.2019.2963764
Hayes, J., Danezis, G.: Generating steganographic images via adversarial training. Adv. Neural Inf. Proc. Syst. 30 (2017)
Shi, H., Dong, J., Wang, W., Qian, Y., Zhang, X.: Ssgan: secure steganography based on generative adversarial networks. In: Pacific Rim conference on multimedia, Springer, pp. 534– 544 ( 2017)
Volkhonskiy, D., Nazarov, I., Burnaev, E.: Steganographic generative adversarial networks. In: Osten, W., Nikolaev, D.P. (eds.) Twelfth international conference on machine vision (ICMV 2019), vol. 11433. https://doi.org/10.1117/12.2559429 . International Society for Optics and Photonics. https://doi.org/10.1117/12.2559429
Tang, W., Tan, S., Li, B., Huang, J.: Automatic steganographic distortion learning using a generative adversarial network. IEEE Signal Process. Lett. 24(10), 1547–1551 (2017). https://doi.org/10.1109/LSP.2017.2745572
Yang, J., Ruan, D., Kang, X., Shi, Y.-Q.: Towards automatic embedding cost learning for jpeg steganography. In: Proceedings of the ACM workshop on information hiding and multimedia security. IH &MMSec’19, pp. 37– 46. Association for Computing Machinery, New York, NY, USA ( 2019)
Yang, J., Ruan, D., Huang, J., Kang, X., Shi, Y.-Q.: An embedding cost learning framework using GAN. IEEE Trans. Inf. Forensics Secur. 15, 839–851 (2020). https://doi.org/10.1109/TIFS.2019.2922229
Mo, X., Tan, S., Tang, W., Li, B., Huang, J.: Reload: using reinforcement learning to optimize asymmetric distortion for additive steganography. IEEE Trans. Inf. Forensics Secur. 18, 1524–1538 (2023). https://doi.org/10.1109/TIFS.2023.3244094
Tang, W., Li, B., Barni, M., Li, J., Huang, J.: An automatic cost learning framework for image steganography using deep reinforcement learning. IEEE Trans. Inf. Forensics Secur. 16, 952–967 (2021). https://doi.org/10.1109/TIFS.2020.3025438
François-Lavet, V., Henderson, P., Islam, R., Bellemare, M.G., Pineau, J.: An introduction to deep reinforcement learning. Found. Trends® Mach. Learn. 11(3–4), 219–354 (2018). https://doi.org/10.1561/2200000071
Zhang, X., Wang, R., Yan, D., Dong, L., Lin, Y.: Selecting optimal submatrix for syndrome-trellis codes (STCS)-based steganography with segmentation. IEEE Access 8, 61754–61766 (2020). https://doi.org/10.1109/ACCESS.2020.2983869
Yang, C., Kortylewski, A., Xie, C., Cao, Y., Yuille, A.: Patchattack: a black-box texture-based attack with reinforcement learning. In: Vedaldi, A., Bischof, H., Brox, T., Frahm, J.-M. (eds.) Computer Vision - ECCV 2020, pp. 681–698. Springer, Cham (2020)
Chen, B., Luo, W., Li, H.: Audio steganalysis with convolutional neural network. In: Proceedings of the 5th ACM workshop on information hiding and multimedia security, pp. 85– 90 ( 2017)
Wu, J., Chen, B., Luo, W., Fang, Y.: Audio steganography based on iterative adversarial attacks against convolutional neural networks. IEEE Trans. Inf. Forensics Secur. 15, 2282–2294 (2020). https://doi.org/10.1109/TIFS.2019.2963764
Lin, Y., Wang, R., Yan, D., Dong, L., Zhang, X.: Audio steganalysis with improved convolutional neural network. In: Proceedings of the ACM workshop on information hiding and multimedia security, pp. 210– 215 ( 2019)
Zhang, Z., Yi, X., Zhao, X.: Improving audio steganalysis using deep residual networks. In: Digital forensics and watermarking: 18th international workshop, IWDW 2019, Chengdu, China, Accessed 2–4 Nov 2019, Revised Selected Papers 18, Springer, pp. 57– 70 ( 2020)
Garofolo, J.S., Lamel, L.F., Fisher, W.M., Fiscus, J.G., Dahlgren, N.L.: The DARPA TIMIT acoustic-phonetic continuous speech corpus CDROM. Linguistic Data Consortium, 1993 (1993)
Funding
This work was supported by the National Natural Science Foundation of China (Grant No. 61300055, 61901237), Zhejiang Natural Science Foundation (Grant No. LY20F020010), Ningbo Science and Technology Innovation Project (Grant No. 2022Z075), Ningbo Natural Science Foundation (Grant No. 202003N4089) and K.C. Wong Magna Fund in Ningbo University.
Author information
Authors and Affiliations
Contributions
PZ, KY: Scheme and algorithm design, network architecture design, code implementation, paper writing DY, RW, LD: Reinforcement learning framework design, paper writing.
Corresponding author
Ethics declarations
Conflict of interest
There is no conflict of interest in the study.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Zhuo, P., Yan, D., Ying, K. et al. Audio steganography cover enhancement via reinforcement learning. SIViP 18, 1007–1013 (2024). https://doi.org/10.1007/s11760-023-02819-1
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11760-023-02819-1